American Rescue Plan Act Lures in the Wild

Executive Summary
DomainTools researchers discovered a cluster of credential harvesting sites masquerading as American Rescue Plan Act signup sites for those looking to receive their federal aid. Through historical WHOIS information and OSINT techniques DomainTools attributed this campaign to a Nigerian web development firm GoldenWaves Innovations. In this article, DomainTools researchers will walk through the techniques and methods used to enumerate these websites and associated attribution with medium-high confidence.
Background
On March 11, 2021, President Joe Biden signed the American Rescue Plan Act into law. The COVID-19 pandemic relief bill was designed to provide $1,400 in immediate relief to working families, emergency paid leave for over 100 million Americans, and expand the child tax credit among a number of other grants and pillars to assist with other budget shortfalls. Since this act was signed into law, DomainTools researchers have monitored for new registrations of domains that targeted relief recipients. Unfortunately, many relief recipients are unaware that this relief will be automatically assigned to them by the IRS, so scammers are using this as an opportunity to collect social security numbers and driver’s license photographs to use in identity theft.

Hunting for More
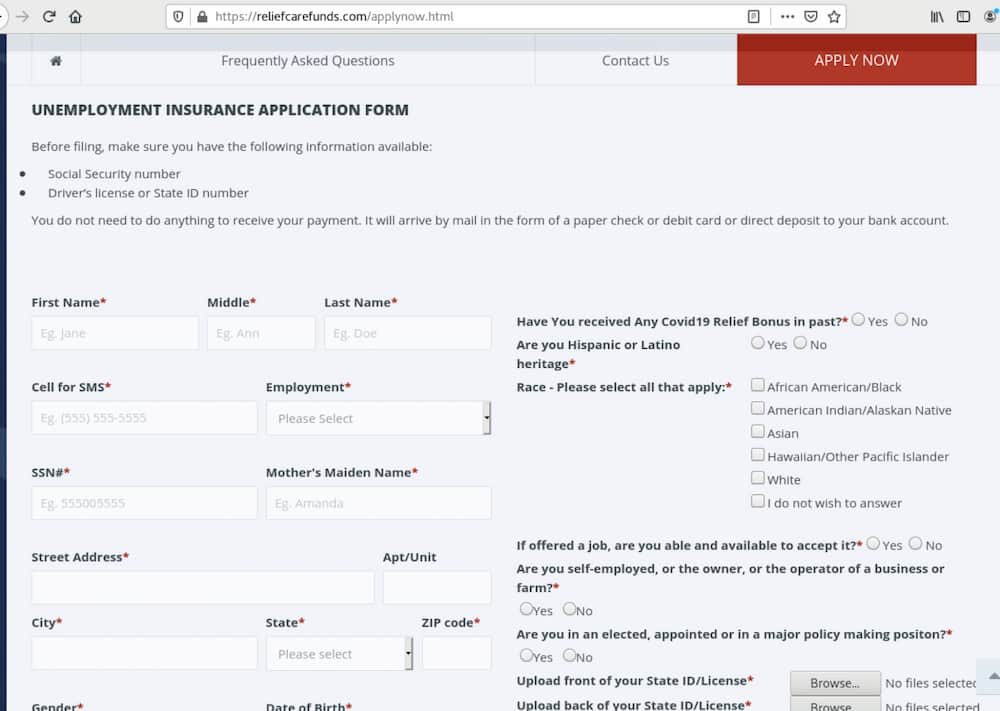
The initial domain found by DomainTools researchers was reliefcarefunds[.]com that contained the above application form with a typical upload to a PHP destination on the same domain. However, buried in the code was a comment that the page had been mirrored from americaforgivenrelieffund[.]com and a contact page that submitted to a PHP script on that domain as well. With evidence of more domains, DomainTools researchers took a look at the architecture behind the pages for similarities. As readers of this blog will know, DomainTools is a strong proponent of the composite objects method for building out indicators and through examining these two pages we could see that what they had in common was:
- Registration through NameCheap
- Containing the “relief” substring
- Containing the “eric” as in America substring or the “care” substringRegistration after the signing of the bill into law on March 11, 2021
- Hosting on NameCheap hosting infrastructure
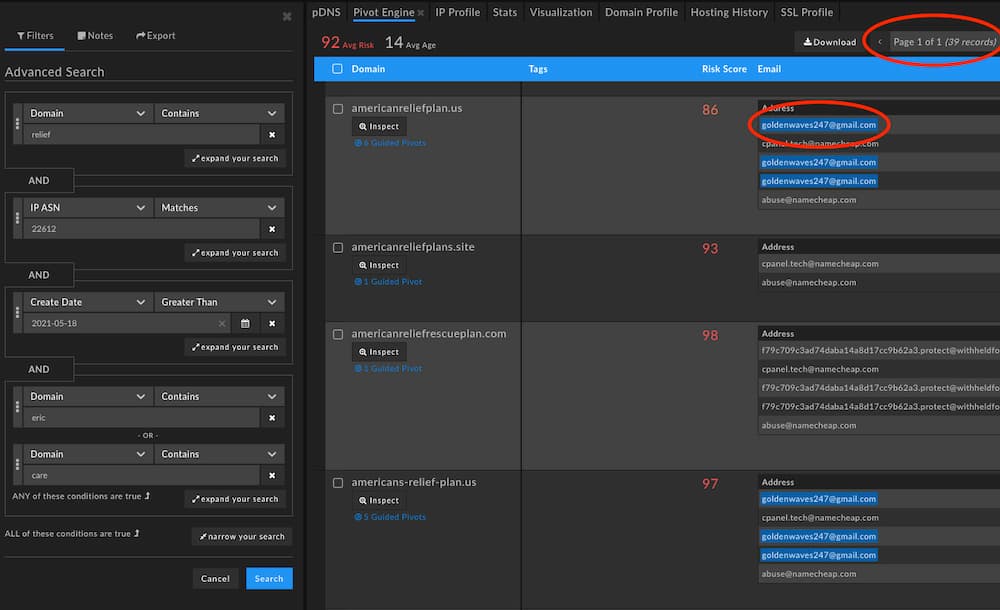
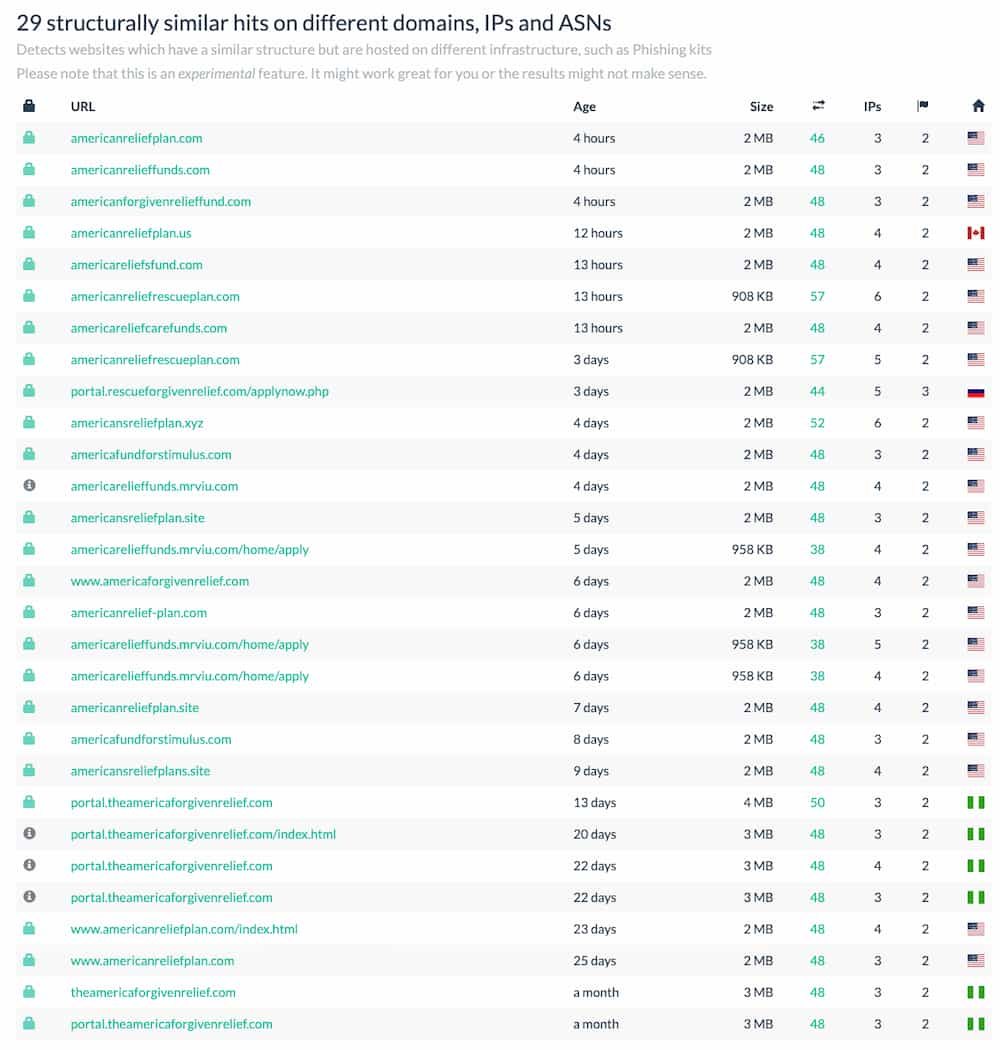
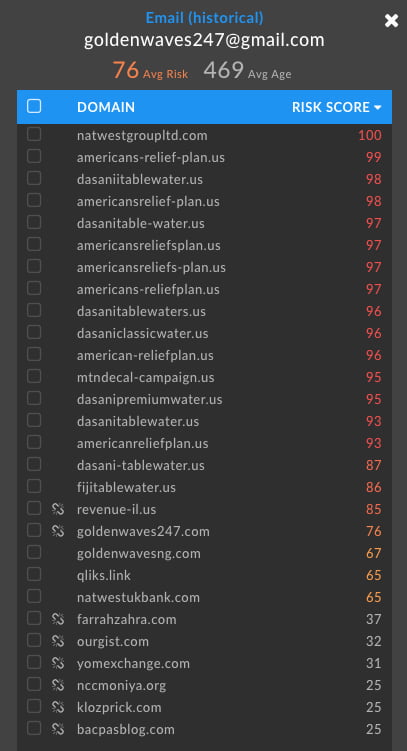
Hunting for this composite in DomainTools Iris Investigate, DomainTools researchers revealed 39 potential domains and an email address associated with a number of them of goldenwaves247@gmail[.]com. To confirm similarities, we used URLScan to search for the list of domains uncovered for any scans done by others that had encountered these domains over the last month. Unsurprisingly, this revealed an additional set of domains with identical structure to the initial phishing page dating back almost exactly a month.
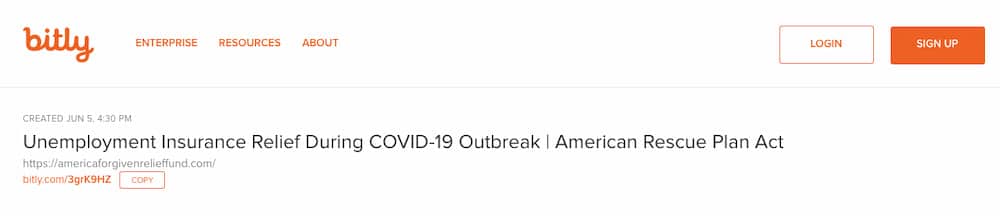
This list of domains then provided another set of important information. For one, DomainTools researchers were able to see that some of these links were being pushed by Bitly link shortening links. With Bitly, appending a “+” to any shortened link provides some data about that link. In this instance, we could see that the shortener was created at 1630 UTC time on June 5th, 2021 with a specific title of “Unemployment Insurance Relief During COVID-19 Outbreak | American Rescue Plan Act” which matches the titles of the other cloned pages.
We can also tell that many of the cloned pages, at the time of their scanning, were not hosted solely on NameCheap’s site hosting services, but were also active on both Garanntor (AS328110) and OVH (AS16276). This allowed the set of items we search for to:
- Registration through NameCheap
- Containing the “relief” substring
- Containing the “eric” as in America substring or the “care” substring
- Registration after the signing of the bill into law on March 11, 2021
- Hosting on NameCheap (AS22612), Garanntor (AS328110), or OVH (AS16276) hosting infrastructure
This then revealed a total of 47 domains matching our criteria including the oldest domain on URLScan page similarities and the oldest domain in our search criteria theamericaforgivenrelief[.]com with a registrant email address of onostboy1@gmail[.]com and an unredacted WHOIS record placing the registrant in Ibadan, Nigeria. Searching on that username then reveals a profile on social media site Eskimi of a web developer with an associated Twitter handle of @onostboy with the name Tosyno based in Ibadan, Nigeria. The city of Ibadan is a small, rural town which makes the registration information stand out as almost always technical contacts for Nigerian domains are located in Lagos, the capital city and technology center. Additional searches reveal the same username participating in sales on cybercrime forums, Steam gaming, and other social media sites.

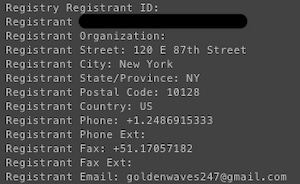
Pivoting on the previous address of goldenwaves247@gmail[.]com that was surfaced reveals a number of domains including Dasani, Fiji, and Mountain Dew brand sites that looks to be recruiting for various promotional programs in exchange for money, a fake UK bank site at natwestukbank[.]com, and finally a site with the domain goldenwavesng[.]com that contained the email in historical WHOIS records before going private in late 2018. This is the site of GoldenWaves Innovations, a technology company based in Ibadan, Nigeria which DomainTools researchers assume with medium confidence to be the legitimate web design firm in front of the identity document harvesting sites.
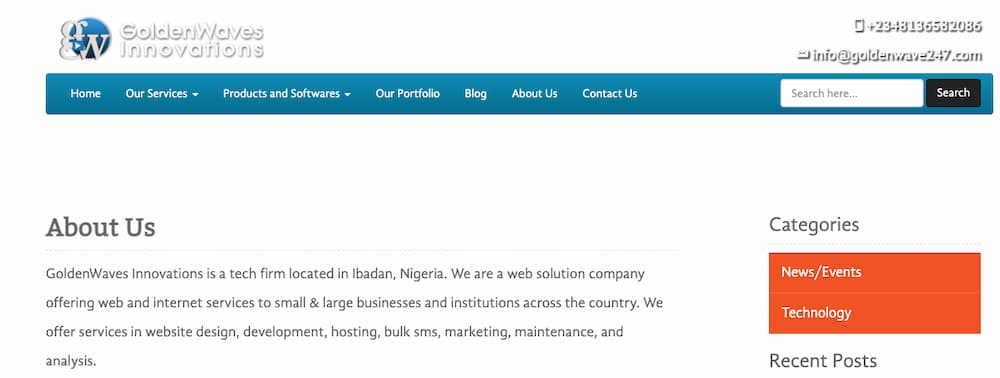
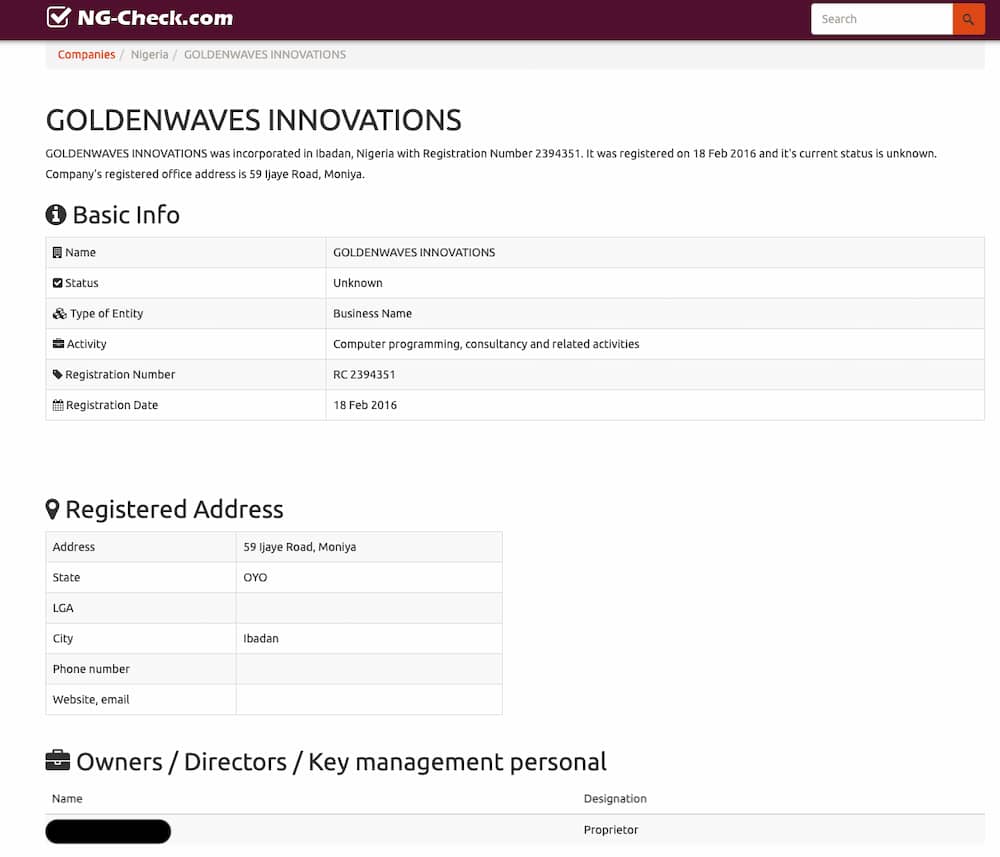
Reading the information on GoldenWaves Innovations’ page we can see that they claim to be registered with the Corporate Affairs Commission (CAC) of the government of Nigeria. Searching for that company name on ng-check[.]com, a site for querying CAC information, we can see that GoldenWaves Innovation indeed has a valid registration along with the name of the company’s CEO which matches the WHOIS details and who claims to be the company’s CEO on LinkedIn. Though the company was registered in February of 2016, their registration is currently inactive.
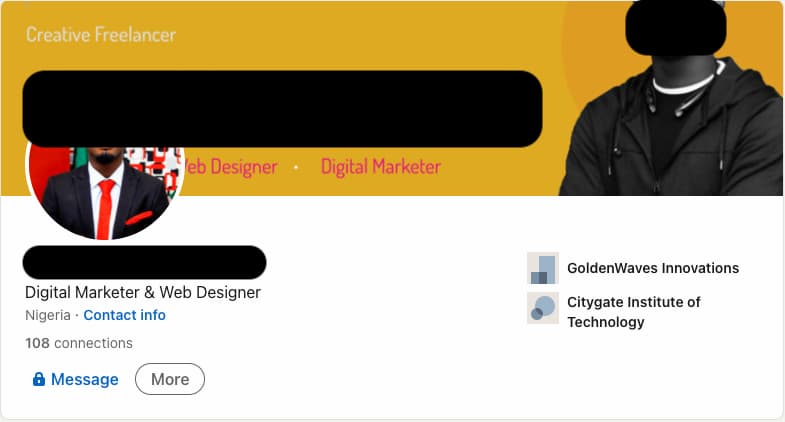
Additionally, the historical WHOIS record unearths an address in New York, New York of 120 E 87th Street. This is an apartment building with condos ranging from $900,000 to $13,000,000 in the heart of Manhattan. While at first that seems strange for a company based in Nigeria, we can see from LinkedIn that one of the company’s developers claims to live in New York City.
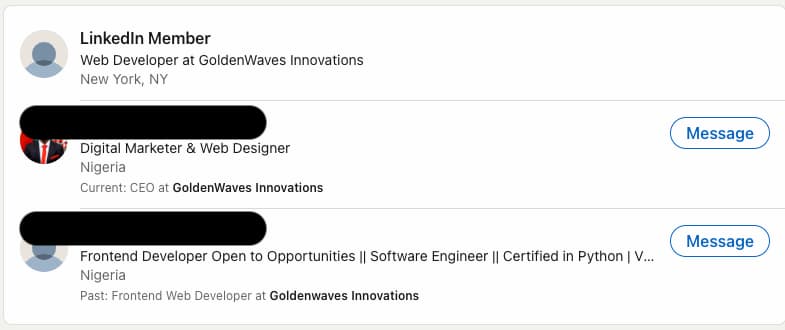
Looking at the CEO’s current contact information on LinkedIn we can see that GoldenWaves Innovations has a new website in goldenwaves[.]com[.]ng which is also tied to the same email address and registration information. This gives DomainTools researchers high confidence that all of these credential harvesting sites are linked to GoldenWaves Innovations in Nigeria. These sites along with any new ones that have cropped up were reported to Google Safe Browsing for blocking.
Takeaways
Credential harvesting campaigns continue to be a fruitful way for attackers to gain legitimate legal documents they can then resell or use for more sophisticated behavior. When looking for federal aid, those in need the most may not always be fully aware of how that aid is being distributed. In the case of the American Rescue Plan Act that money was coming directly from the IRS, but nonetheless unsuspecting victims could be led into uploading their identification documents to one of these sites.
DomainTools researchers would recommend that security teams utilize internal passive DNS monitoring to alert them of new domains aged less than 90 days that are responding with IP addresses on cloud provider ASNs. That is the most efficient way to discover these domains on your own network. As for end users, DomainTools recommends:
- Reporting the site to Google Safe Browsing if you come across one so that it will be blocked as soon as possible on all major browsers.
- Reporting the malicious site up to your security team along with the phishing email that came with it as there may be a campaign targeting your employees.
- Never upload your documents to a website you are not logged into and particularly not a site claiming to be a federal one without a .gov domain name.
Iris Hashes for Hunting
GoldenWaves Innovations Domains and Associated Emails
U2FsdGVkX1+f4H5GPcY4qa4f5nIuj2vjMY/8shjZ/tasRLRe/sgFkQzNfFJ7EGxjoQYYU9PCo3lgkhHJ/+kasE5i+pABVjFEiwQFQU8E8MVmoH7pPU/VD+JrcZaeh9ORBOtMN47ldF8oaaLz1Fp52q3DRvemgWYJdt+E7rc8aNgccpBGpZCVjP2Xm36kBmD7ri0IDeLGL5MiZ5R0L8Pxg4qFZF2vJYgiKa3h4eeUEm4bPxs7tJbgmHIX+HwUr6rjhEeAzcyOL0c847ytLxGiTZJax5OPdrsmace92PhGYV6AoMAfVve8Fw53obsSXhoJ978+aU4NtLkjqeQgbG7q44YfOygSuWaGfceoztmLOezoprSehg8vkFtUKY/Ncntld8zXCXumOxHnxPgTihV5TtLdmtZtwydxT4A8Z8hqOJ5zJAAnyKMPOj7dbiYpfrhd44NMYMFpPhhmYoM96n7Q2kKGJrhGpKx5LglPzWFQd+x+kpYdPc87Y09fH//oXwS3XzDclGxrOReJFBjfZVEvXhEs/40Bz2n+ZSu6Ev4pTxQzL8luMSl0FtsKZPnGwF23TgIvYg8J5nSgtXFtpzYaQVe/o+aOz96o1pYoYdJ/NvAP6W3DXXb4OlwKEOguK0g8Ybz/TLJ4t0NyEvQzRjM3oX2OsJZcq8X8XS3D6YxWDRaUo0tOF9xU21Y5DQ95YW5TjJZCCeU843hIXYx4JhiuMSsfOccvg9w4bcMf1SLh9GhWl8smOMzN+jTauOrUrx83aAP+AtO+QL+jLakVMxty9M0z+fiDGwX2iTtxUtCsRPTuKz2g52oq+gT0VqqQckXx
Relief-themed Domains Matching Registration and Infrastructure Patterns
U2FsdGVkX1+QgEcPUsLxQS18UIt6kBbpnrhOiGN0x4ILTpIO3GBI29j+7/Vx6a/Lw82tvNHQEhbWPQEjCk2pCHkZz/aifZBM5pEmfiI9714onZV6wCqtj2tckgDbbctBsbhvVz1Nn84HviiGJvMcAnnhwD1+eu0M/i+TVwluTWmegtkBGmyHSlEmMncSA5t2ky2H2zUdlp1EuqBDQZ5D5lIdraKCDmSnbylkdoj8yutOL2fO6aQheEQE9D7VMUBFCc5ZqvAwbu1FCGs+tAf8mnq0KCz8NcmF+EMI67AvTa49s1G/gEmKqWzDZaevLcValq6GP3DgumCwAx1qjsMvzo81G7uuQbN4/URGYtpYuS1wCCfLycvCJiQTwdo0j3R+R2lsUs2HuW/LAYrfu/2uWMu6q9PLHrk51VwOtKiQAErYbZjrxC4RT/r3laBzHvstlKenfVs+QNGPYi4svx/UZ2MWbp+3HSeYQlHTXp1DXm5ur36tLZ9IB5uj26ajMtvGFpE0DJArQdUWQu0TYp4rQmgcOHkNi8aNaLMkmpFe8gQpB2K/fRn1UT3/eDwdUscXTJl/FoAyQFrvRrbM+8zL1uXDehFxmM0ylG8jHK7dh0SKbVzcExoKwlyC51VNl0Ss5vbeYKIW6EPqPmHAa6OOg1AefDqXkwP29YKXToqCvKo3zu4osOVa2JLQxAhh7JfNDPEtF9dPMtjJaddegv4BXOSjlGUoFg4/KqmsLZ/J7p+BTWbiwO3NBBPFbx9zmTbU2Nd9uMqnK2BI4Zd15ElUmZXHwZKnMa2gX4+h+M7GtZmdOf6QYcAFYML2bkzD2PCD


