Cybersecurity Defense Competitions: Inspiring the Next Generation

On April 7th, I had the pleasure of participating in the 3rd annual Department of Energy (DOE) Cyber Defense Competition hosted jointly at Argonne National Laboratory (ANL), Pacific Northwest National Laboratory (PNNL) and Oak Ridge National Laboratory (ORNL). This is the first year the competition has been hosted across three labs in three time zones, but all went off without a hitch. Full disclosure, I am a former employee of ANL and worked on the team that designed the first two competitions, so as you can imagine, it was exciting to return as a volunteer and see what the DOE came up with to challenge this year’s students.
The DOE Cyber Defense Competition, or CDC, was designed as a competitive event for college students to see the challenges inherent in defending infrastructure that has more than just a traditional information technology footprint. As we pointed out in a recent blog post, infrastructure that includes cyber physical devices such as industrial control systems (ICS) or supervisory control and data acquisition (SCADA) devices can be difficult to secure without domain expertise. The competition is specifically designed to drive this reality home by giving students infrastructure that included both normal IT systems and an ICS or SCADA type device.
Technology
The competition and technology have evolved a fair amount in recent years. Two years ago, participants used a Raspberry Pi with a light attached to it that spoke the modbus protocol to a web interface. Last year, it was much more involved, with a water pumping system build from CPU cooling materials and using a real human machine interface (HMI) frontend. This year, the competition had a natural gas focus, and the mini-ICS system included a drill that was controlled by a much more realistic HMI than in previous years.
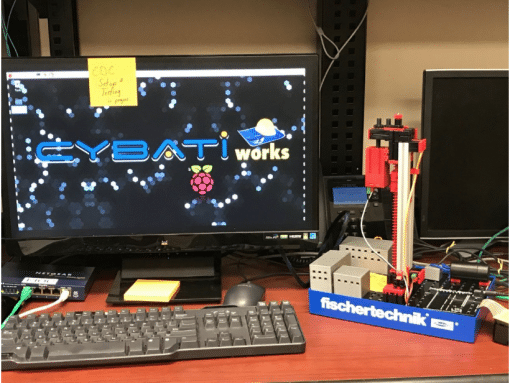
This year’s natural gas ICS simulation.
Participants and Teams
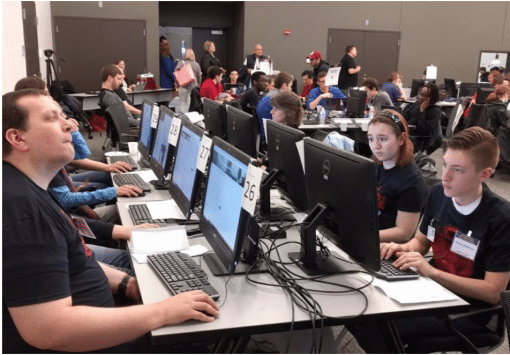
Each year, the DOE invites teams of college students from around the country to participate in the CDC. This year, they hosted 25 teams hosted across 3 national laboratories. Each team is between 4-6 students and has a faculty advisor from their school. The teams are given remote access to the infrastructure they’ll be expected to defend 30 days before the competition actually starts. The infrastructure they’re given has a number of vulnerabilities baked in and the teams are expected to attempt to mitigate those vulnerabilities within certain parameters that mimic business requirements one would expect to see in a real world environment. Students are generally told to act as if they are a cyber team starting at a company that has been well established, but never had a dedicated security team. This means they should expect their systems to not only have vulnerabilities but in some cases, to be pre-infected. On the day before the competition, students are allowed to come to the site and have physical access to their systems for 8 hours for one final opportunity to prepare for the competition.

Blue teams at work defending their systems.
The competition actually has several “teams,” though only the blue teams are actually competing against each other.
- The White team acts as admins of the competition and the scorekeepers
- The Blue teams are made up of college students who are competing, attempting to defend their systems
- The Red team is composed of military, government, and private sector volunteers who attack and attempt to exploit blue team’s systems
- The Green team is made up of non-technical volunteers who act as users or customers, evaluating the usability of blue team’s systems
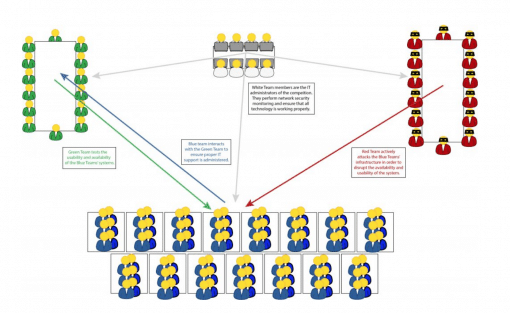
This year, as a volunteer, I was asked to help lead the red team. Red team members are encouraged not to think of themselves as competitors, but instead to think of themselves as facilitating the competition between the Blue teams. The Red team doesn’t get to “win,” and there is some danger that if they attack and compromise systems too badly, too early in the day, it will make the competition less fun for everyone. The Red team used realistic attacks and exploits including system and application level exploits like cross site scripting, sql injection, password brute forcing, man in the middle, etc, but also employed tactics like social engineering and phishing attacks. The Red team only *seriously* compromised 21 out of 25 teams, but we were able to affect the operations of *all* of the team’s ICS via fuzzing of the modbus protocol. This is one of the ways that we attempted to convey the message that the tactics needed to defend ICS devices need to be different than those of traditional IT systems.

Here’s me participating with Red team activities… clearly need more coffee.
Rules and Regulations
Another thing that makes the DOE CDC competition unique is that teams are required to support users interacting with their systems. The Green team consists of non-technical volunteers who are brought in to use systems that have been hardened, or in some cases, totally redesigned by the Blue teams. Blue teams are required to create documentation for Green teams to make use of and are graded hourly by green teams. Usability scores directly impact the team’s overall score in the final standing. The competition designers wanted to inspire students with as realistic of a scenario as possible, and it’s much easier to secure a system if no one ever has to use it.
Green team members grading the usability of blue team’s systems.
Results
Overall the competition was a resounding success. Everyone learned something, including the red team and white teams. More than anything, the competition is about inspiring young people and informing them about the real challenges defenders face, and to show them that effective cybersecurity requires creativity and innovative problem solving…it’s not just about learning techniques and tools. As a DomainTools employee, it’s important to be reminded of this as we’re designing systems that help our customers investigate threats. Also, it’s great to work for a company that encourages employees to engage with the security community and participate in training the next generation of information security analysts, engineers, and defenders!

