Coming up this week on Breaking Badness. Today we discuss: Find Your Breach, Intel Insider Threat: Intel x86 Root of Trust, and our fun new game, two truths and a lie.
Here are a few highlights from each article we discussed:
Find Your Breach
- TrickBot is a really nasty piece of malware that specifically targets personal banking accounts.
- TrickBot, also, is much more high impact than just your personal banking accounts that get targeted upon infection. We’ve seen TrickBot samples in the wild that drop Empire or Metasploit payloads, or even Ryuk ransomware. So, TrickBot is pretty broad in capabilities and it’s impact.
- An unknown threat group (at this time), was detected dispersing malicious Word documents containing TrickBot across a large e-mail spam campaign sent across millions of email accounts. There was a large success rate, apparently, up to 10% of organizations in Italy were affected by this specific attack.
- These specific threat actors are taking advantage of the panic and concern around the COVID-19 infections, specifically in Italy. As you know, Italy has one of the highest infection rates in the world and the government has issued a large quarantine in place.
- In order to get the victim to open the document, the email contains language that explains how to protect yourself against Coronavirus exposure, with a signature of “Dr. Penelope Marchetti (World Health Organization - Italy)” to attempt to make the claim even more valid.
- Here is the flow of this particular attack
- Word document sent via e-mail containing macro code
- VBA macro code drops two files: JSE (Encoded Javascript Script) and BAT (Windows Batch) & beacons back to C&C
- VBA code then executes the BAT file, which executes the obfuscated JSE file
- The Javascript dropper then beacons back to the C&C and drops an encrypted TrickBot binary
- The Javascript then decrypts and executes the TrickBot binary
- From there, TrickBot waits for commands sent by the C&C. You can expect either RAT-like or ransomware payloads/commands to be executed from here on the victim.
- When TrickBot has been successfully installed, not only is your organization affected by an attacker with a foothold on your network, but your organizations employee’s personal information is also at risk with TrickBot since we’ve seen TrickBot act as a personal information harvester as well as a RAT.
- You’ve got to go with the recommendations that CERT put out. Only trust government and research institution’s websites, don’t click on anything in your email that’s health related. Really all of the always basic phishing stuff -- be aware that people are trying to capitalize on fear here.
- I can’t emphasize enough how important it is to invest in a quality, behavioral based antivirus program, like Windows Defender with Cloud Protect enabled. Which is free. If you have the time and resources, also invest into deploying AppLocker into your Windows environment for even more security.
Intel Insider Threat: Intel x86 Root of Trust
- This vulnerability is what underpins a lot of the security technology that runs things on the Internet. For instance DRM or Digital Rights Management, the encryption technology that underpins how media companies maintain copyright on videos is affected. That’s a core technology to Netflix and elsewhere. Basically anything involving security—UEFI secure boot, the booting system which verifies your computer's firmware, the TPM chip for instance relies on this boot ROM so we’ve got password protection and disk encryption vulnerable here as well.
- This vulnerability is in the boot read-only memory, commonly called ROM, of the Intel Converged Security and Management Engine. The best way to think of it is that there is another subprocessor in your computer that is entirely protected from the rest of the system and that extra subprocessor handles all of these protected security functions. The ROM handles reading of chipset keys for verifying all firmware and such. It’s the walled fortress here that keeps everything secure right? The ability to modify that boot ROM and control reading of the security keys and the verification of all firmware then breaks security on the entirety of the rest of the system since you can then load untrusted code. Since this is a hardware bug it is unfixable without getting a new motherboard and it breaks the chain of trust for the entire machine. Basically it means nothing is secure on your system. The only upside here being that exploitation of the vulnerability—according to the researchers—requires either local or physical access so nothing remote. They’ve also already submitted some PoCs and patches, but believe that there are other attack vectors.
- The folks from Positive Technologies actually had the best quote on this. “We discovered this mistake by simply reading the documentation, as unimpressive as that may sound.” As far as I have heard it’s not being exploited in the wild. This is just another one of those big chipset bugs though that is a big deal, will be fixed, but takes a lot of sophistication to exploit.
- Oh this impacts anyone with an Intel chipset outside of Gen 10 chipsets which don’t have the vulnerability. Basically everyone not running AMD or ARM hardware is affected.
- I’m not sure if Intel can update the boot ROM without you getting new hardware. We’ll have to wait and see on recommendations from Intel once more comes out. I think this will be a big deal, but it will be up there with other huge hardware bugs of this sort like Meltdown, Spectre and the sort. I think the most practical use for this and what will likely happen is that it will be used to attack DRM. Or maybe I just remember DeCSS and how epic that was to the hacking community.
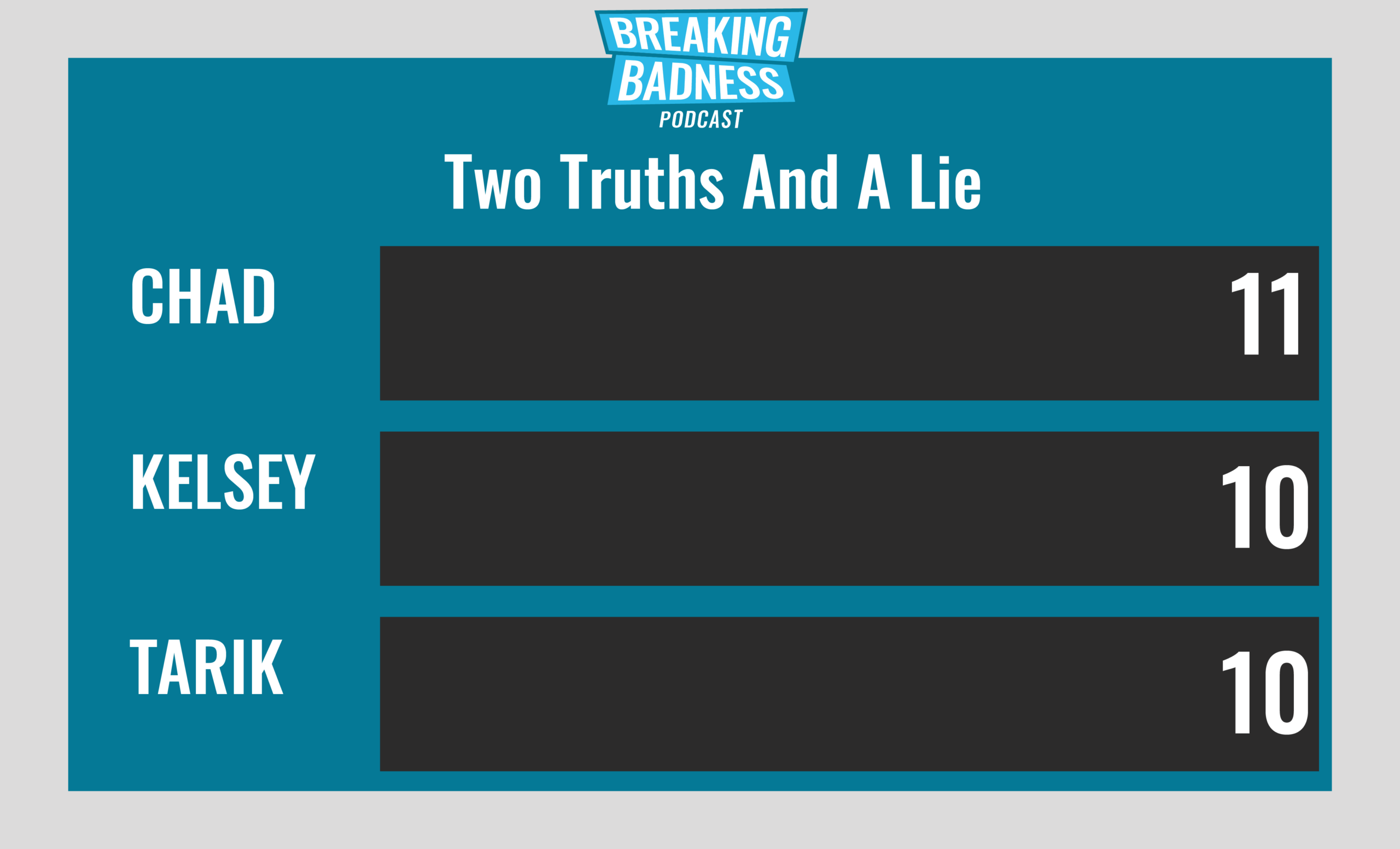
Two Truths and a Lie
Introducing our newest segment on Breaking Badness. We are going to play a game you are all likely familiar with called two truths and a lie, with a fun twist. Each week, one us with come prepared with three article titles, two of which are real, and one is, you guessed it, A LIE.
You'll have to tune in to find out!
Current Scoreboard
This Week’s Hoodie/Goodie Scale
Find Your Breach[Chad]: 7/10 Hoodies[Tarik]: 6/10 Hoodies
Intel Insider Threat: Intel x86 Root of Trust[Chad]: 9/10 Hoodies[Tarik]: 9/10 Hoodies
That’s about all we have for this week, you can find us on Twitter @domaintools, all of the articles mentioned in our podcast will always be included on our podcast recap. Catch us Wednesdays at 9 AM Pacific time when we publish our next podcast and blog.*A special thanks to John Roderick for our incredible podcast music!

