Coming up this week on Breaking Badness. Today we discuss: Rockin’ Raspberry Robin, Here We Twilio Again, and Two Truths and a Lie.
Here are a few highlights from each article we discussed:
Rockin’ Raspberry Robin
- Microsoft says a threat group tracked as DEV-0950 used Clop ransomware to encrypt the network of a victim previously infected with the Raspberry Robin worm.
- For our listeners and readers, here’s a brief overview of Clop ransomware:
- Clop is a variant of an earlier ransomware family that’s operated by a Russian-speaking group, usually in a ransomware-as-a-service setting where the software is rented to affiliates that do the actual infecting
- It’s generally associated with financially-motivated actors, and gained its name from its behavior - files encrypted by it and held for ransom gain the dot clop file extension
- It’s been used as a final-stage payload after initial compromise, asset and configuration discovery, and in many cases data exfiltration for dual extortion schemes
- It’s pretty darn efficient and according to some analysis, Clop and the gang behind it have single-handedly driven ransom demand amounts upward
- What about Raspberry Robin?
- Raspberry Robin is a first-stage malware that infects systems via physical USB drives and worms from there
- It’s Windows-only and uses Microsoft tools to bypass user account control and other protections to gain and maintain its foothold on a system so it can then drop a different, more advanced payload (like Clop or other ransomware)
- When it was first reported (by Red Canary, earlier this year) Raspberry Robin had established an interesting grasp on systems but didn’t seem to do much else
- Unfortunately, that’s progressed. Microsoft Security has observed Raspberry Robin as a more wide-sweeping operation than it originally appeared, intended to establish initial compromise on systems and at institutions
- So what Microsoft saw in a larger perspective suggests that Raspberry Robin is becoming popular with what are called “initial access brokers” - malicious actors that compromise systems or networks and then sell that access to other bad guys who then push further in, in order to accomplish their own goals (often but not always ransomware deployment)
- How does Clop work with Raspberry Robin?
- So the article we’re looking at here talks about a specific threat group called DEV-0950 and how they’re using it
- Microsoft did a nice deep dive on both behavior analysis and mitigation guidance, and some indicators of compromise to be on the lookout for. DEV-0950 is either using Raspberry Robin as its vector of initial access, or has successfully partnered with an initial access broker fond of Raspberry Robin, so the first stage starts there
- Post-compromise activity involves dropping Cobalt Strike Beacon on systems to provide enhanced functionality and easier lateral movement across a network
- Once the actor has decided they’ve spread far enough, the third stage looks to be a Clop ransomware payload
- It’s frankly an interesting mash-up; it may be that whoever’s putting all this together is only really responsible for the post-compromise, pre-ransomware activity, so they farm out the access by paying an initial access broker, exploit that access, then use an easy-button “Ransomware-as-a-service” solution
- So the actor directly responsible may be living the high life and putting in banker’s hours at most, content with losing a little profit to partners for a bunch of easy scores
- Once those kinds of partnerships get in a groove the efficiency can be breathtaking. Along with the profits
- So the article we’re looking at here talks about a specific threat group called DEV-0950 and how they’re using it
- What do we know about the threat group, DEV-0950?
- They overlap with FIN11 and TA505 threat groups, but that’s not to say they’re all the same, or even necessarily subsets within a larger organized set
- The interconnections between these groups aren’t often super clear. One of the interesting things to note is that they’ve all had more history with email-based attacks like phishing rather than a USB-spread attack like Raspberry Robin; and DEV-0950 and FIN11 in particular have been known to outsource work when it suits their purposes
- What should organizations do to mitigate these attacks?
- Endpoint detection is a no-brainer here, but along with that comes the need to ensure that the responsible team is seeing and responding to the alerts appropriately - we’re all human, we all get fatigued, and wormed behavior like Raspberry Robin can worsen that
- In addition to endpoint detection and ensuring alerting effectiveness, group policies and other methods of preventing USB-based attacks (some places even physically block USB ports in workstations) would be helpful here. Same with policies on running untrusted or unsigned processes or obfuscated scripts
- But of course there’s a usability price to each of those steps - it’s always going to inconvenience someone. And navigating that tension is not simple
Here We Twilio Again
- Cloud communications company Twilio disclosed a new data breach stemming from a June 2022 security incident where the same attackers behind the August hack accessed some customers' information
- In the spirit of Halloween and someone pretending to be something they’re not, we’re gonna talk about voice phishing, one of the scarier tricks out there. And we actually talked about Twilio back in episode 129 in August. Maybe a quick recap of what happened there as we discuss this story?
- This is a story of everything old is new again. This is technically the second attack, but it predates the August attack
- Both attacks use social engineering, but the one we’re discussing today uses voice phishing to convince the person on the other end to give up information or credentials - it could be someone from the IT help desk previously scoped out, but they target a person and play on the idea that everyone wants to help out a coworker if they can. They get access by simply making a phone call
- This is a story of everything old is new again. This is technically the second attack, but it predates the August attack
- How does the June incident compare to August?
- They’re similar attacks with the same goal
- The August attack used SMS phishing - employees were sen convincing text messages to open a fake login portal so bad actors could access their credentials. People are busy and want to act fast, so it was definitely effective
- Twilio is an SMS delivery company - when you set out for a new account and need to confirm your phone number, you receive a message (most likely from a company like Twilio, because it’s easier to outsource this rather than build your own system)
- In August, Singa was targeted - when you try to move your Signal account between devices, you need to do SMS verification
- The adversaries tried to re-register devices to impersonate the real owner of the account
- In June, instead of SMS, the adversaries used voice phishing, which is harder to do convincingly. A month and a half later, they switched to SMS, which is easier to do at scale and chances are, you’ll have a better result.
- They’re similar attacks with the same goal
- What is Twilio doing in terms of mitigations?
- It’s been a rough time for Twilio and the fact that they disclosed a second breach that predates the first isn’t great
- They also noted that in the initial breach, the intruders were in the system 2 days longer than previously said, which is good to admit, but not ideal to hear
- They’ve taken some steps internally, but because it’s employees being targeted, there’s little they can say publicly
- The biggest point to improve is training
- Set expectations that no one will call you for your password no matter what the person on the other end of the call is saying
- The biggest point to improve is training
- Twilio also announced hardware authentication tokens which is an open standard to integrate with web browsers. It can help, but there’s a huge amount of overhead involved - shipping them out, training, etc. It’s a lot of work
- What can employees do on their own for mitigations?
- If you never answer your phone, you can’t get phished
- In all seriousness, depending on who your phone provider is, you can block well-known numbers that are frequently used for phishing
- End user training is really the best option here
- With deep fake voice being commercially successful, you can impersonate the voice of the CEO and if you get a call from that person, what do you do then? Setting the expectation that people are going to call you to ask for things is best
- If you never answer your phone, you can’t get phished
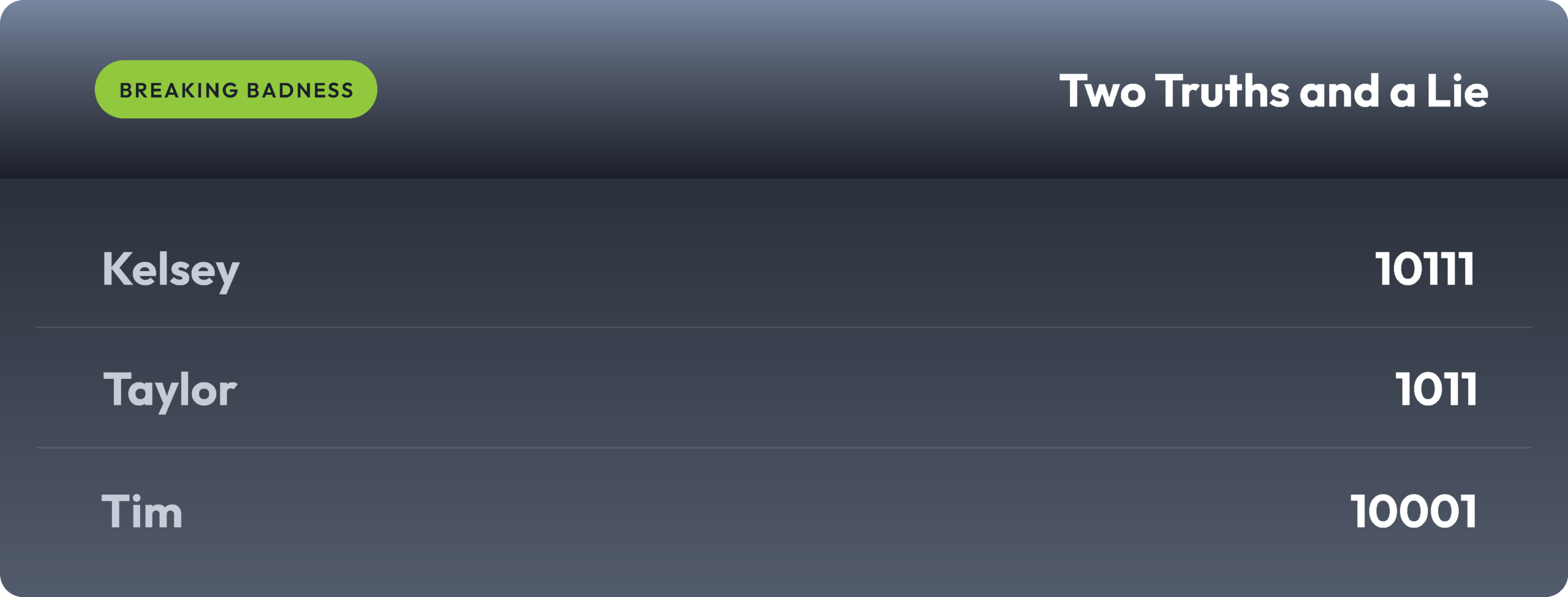
Two Truths and a Lie
Introducing our newest segment on Breaking Badness. We are going to play a game you are all likely familiar with called two truths and a lie, with a fun twist. Each week, one us with come prepared with three article titles, two of which are real, and one is, you guessed it, A LIE.
You'll have to tune in to find out!
Current Scoreboard
This Week’s Hoodie/Goodie Scale
Rockin' Raspberry Robin
[Daniel]: 3.5/10 Hoodies
[Ian]: 5/10 Hoodies
Here We Twilio Again
[Daniel]: 2/10 Hoodies
[Ian]: 2.5/10 Hoodies
That’s about all we have for this week, you can find us on Twitter @domaintools, all of the articles mentioned in our podcast will always be included on our podcast recap. Catch us Wednesdays at 9 AM Pacific time when we publish our next podcast and blog.
*A special thanks to John Roderick for our incredible podcast music!

