DomainTools 101: Blocking and Tackling Bad Domains

In my last post we covered some ways to look deeper into a report and find other connected domains that are part of the actors infrastructure. Let’s to continue to dive deeper and learn more.
Reverse IP Pivot
In our last post we uncovered an IP address that was being used to host the domain brentsmedia[.]com (85.17.65[.]197). We can expand on that IP address to learn what else is being hosted on that IP address. In this example, this process identifies another domain hosted on this IP: digitalmediapedia[.]com.
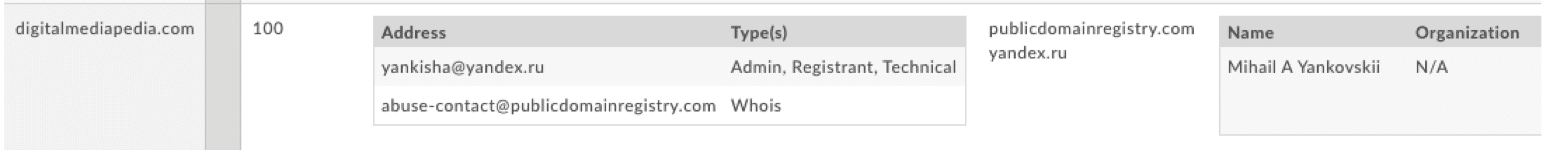
We have the ability to look at the IPs of the other domains- but in this example, there is a valuable piece of information that I’d like to touch on called the Risk Score (which I mentioned briefly in my last post).
Risk Score/Reputation Engine
At DomainTools we are actively assigning a risk score to domains as we discover them. This risk score can be described as a “proximity to badness” score. For instance, we are currently purchasing several blocklists from well known vendors and leveraging that data to help our customers know how closely related a site is to known blocklisted domains. These scores are bundled into our products, and the underlying technology is called the DomainTools Reputation Engine.
Blocking and Tackling
Now that I have this great investigation and some bad domains that I’ve uncovered, what should I do with that information? I would start with blocking those domains by adding the discovered domains to your blocking point, either in DNS, or at your firewall. Tackling is the natural next step in your process. “Tackling” means taking what I have learned and scouring my logs to make sure that none of the other domains we have identified have been on my network. I realize that in this example you probably haven’t seen any of these domains on your network. This is where your internal sources like domains flagged by your SIEM tools, your proxy, and DNS logs come in handy. These resources are critical to find potential threats in your network and to proactively block threat actors.
Monitoring
It turns out threat actors tend to follow patterns in their methodology- which means that identifying these patterns and architecture empowers security professionals to be proactive in blocking badness. DomainTools offers monitors for registrants, name servers, and IP addresses, and others. This will give you the head start you need to learn about newly registered domains, domains that were pointed to or away from a name server, or IP address.
Conclusion
We were able to find a threat actor that was using someone else’s name and brand even though they had gone out of business, and closed shop. They picked up an expired domain, and used that particular branding to begin pushing out malware via a malvertising campaign. We also uncovered additional domains owned by the same threat actor, and other resources tied to the same infrastructure.
I find it very helpful when I get a report from the security professionals and plug data into Iris to dig even deeper. This enables me to learn more about the threat actors, their resources, and whatever else can I learn about them so that I can get ahead of them and begin blocking and tackling them from getting on my network.

