DomainTools 101: Hunting Grizzlies with DomainTools Iris
When we hunt, we’re usually starting with some kind of indicator that something bad has happened. These are often referred to as IOCs or Indicators of Compromise. When we get a good report like this one from Homeland Security, we can use it to help us find out more about a threat actor and their infrastructure, domains, etc. than have been disclosed in the report. In this blog, I’m going to use some of these IOCs to show how we go beyond the data in the report. I’m going to leave it up to you to decide how much further you want to go with your investigation and make your own conclusions on how these connections help, as each investigation will be slightly different.
At DomainTools we have a new tool in our arsenal that give us some additional context using what is known as passive DNS. I want to give some examples of what passive DNS is, and show how adding it to Iris can help find additional answers that you might not have seen.
First, a quick primer on passive DNS (or pDNS). Passive DNS or Passive DNS replication is a technique invented by Florian Weimer in 2004 where inter-server DNS messages are captured by sensors and forwarded to a collection point for analysis. I like to think of it as a whole bunch of recording devices that are scattered all over the internet listening for very specific traffic, namely DNS traffic and are tracking what is asked for and the response. This can be very helpful for a number of reasons. Firstly, domains can move from one IP address to another and so that response will change. The second is that sometimes all we have to start an investigation is an IP address, and knowing what has been hosted on an IP is very important in your investigation. Finally, it’s often helpful to hunt for specific terms or wildcards in the domain name and also the subdomains. For instance, I previously wrote about a threat where threat actors were using Kohls in a subdomain which we would now be able to discover using passive DNS.
Back to hunting for the Grizzlies, in the AR-17-20045 report there are a couple of IP addresses that are mentioned on page 58, and some domains on page 57 which show as 1of63, and 2of63 in the Malware Initial Findings Report (MIFR) – 10105049-Update 2 section of the report. We will be looking at both of these pages to see if we can uncover any additional details about the domains and IP addresses in the report. For this example, I’m going to start with the first IP address mentioned: 204.12.12[.]40. Ultimately I would take each IP address and do a full investigation around it and the correlate my results looking to find both central points of convergence, like an email address, and also loosely connected outliers that I can use to make other connections.
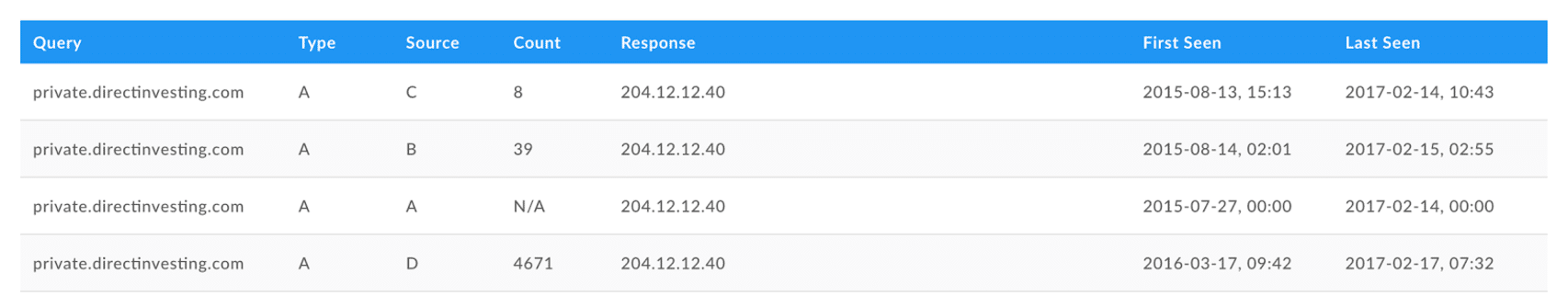
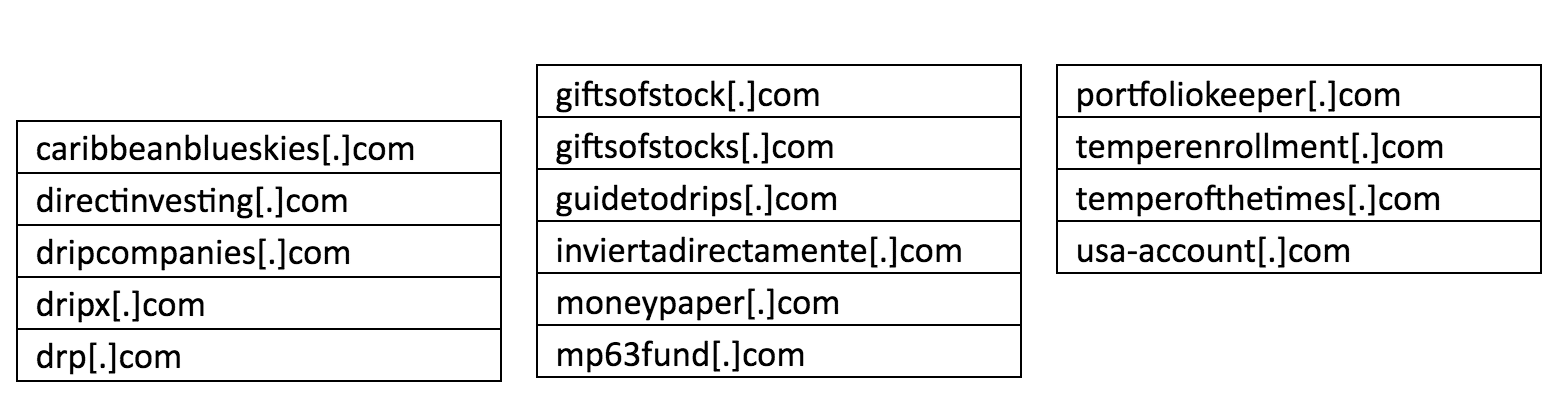
I see that all 4 sources of pDNS return the same results — private.directinvesting[.]com which is one of the domains mentioned in the report. I want to see if I can uncover any additional details about this threat actor and his Tactics, Techniques, and Procedures. A quick pivot on the registrant email shows me this list of 15 domains:
The next IP address in the report, 209.236.67[.]159, unveils 39 domains directly in the Pivot Engine in Iris, which mostly look to be registered by three actors:
- Craig Audley with 31 domains
- Martin Knipe with 3 domains
- Joachim Nuyttens with 1 domain
If I take the results above and send them to the Pivot Engine, I get a considerably greater results set of 119 domains. One of the domains tied to Craig Audley has a Risk Score of 100, and is a known malware site. Definitely someone I would want to track and watch the 124 domains owned directly by him.
Using the next IP address of 146.185.161[.]126 returns results in passive DNS, but no results in Pivot Engine. If I take the pDNS results and look at the domains returned, I get these 3 results
- lazerpenguin[.]com
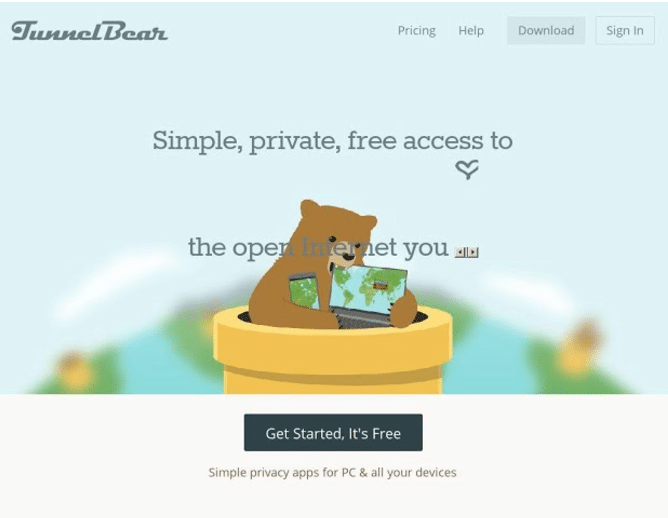
- tunnelbear-ios[.]com
- reduc[.]ru
By doing a pDNS pivot on the domain tunnelbear-ios[.]com (see screenshot), I see that it was also hosted on IP address 50.56.72[.]201. Next, I did a pDNS search on that IP address and I uncovered tunnelbear[.]com, which is currently privacy protected, but I can see in Whois History that it was once registered to “Ryan Dochuk, Green Platforms”. This is a site that provides privacy vpn services to customers. These type of VPN sites are used by threat actors to hide their real location, which is why when hunting we utilize other useful clues, like compile times for malware, default language, etc. to help us learn the true origin of the attack.
In conclusion, you can see that by adding sources of passive DNS data, you can get to new answers that allow you to paint a more complete picture of threat actors and their connected infrastructure.
Happy Hunting!

