DomainTools 101: I Love to Fish

I love to fish, just saying. I enjoy being able to find a nice stream or lake and from my station above the surface, I imagine what it’s like under the water and where the fish may be hiding. I’m not sure they’re aware that there’s danger above the water, but I can only guess it’s instinctual.
When I have found a place that I think holds the fish I’m looking for then it’s time to plan my attack. I decide what kind of lure or bait is most likely to get the fish out of its safe place. My favorite lures are spinners, as they are really nothing like anything that the fish should be interested in: they’re hard and metallic, but they do elicit some specific responses from the fish. Now, I’m no fish psychologist, but I do have a great imagination, and I imagine that they look like something they would like to eat, and so they flash out and strike at it, and then I have them. I think it drives a couple of key instincts: one is that the lure is something they want and another is that it looks like it’s quickly getting away from them.
//imgs.xkcd.com/comics/phishing_license.png
I don’t think that a cybercriminal is much different in planning their phishing attack. They have to do reconnaissance from outside of the network. Once they have decided who to attack, then it’s on to the planning stage: who are they going to try to impersonate and what are they trying to achieve. Many times, the threat actor is someone inside of your own company or from one of your key vendors. This type of targeted phishing is typically referred to as spear phishing, as they have a very focused directive. They often learn everything they can about the target, looking at social media, organizational structure, trade articles about new business deals, etc.
Next comes the physical setup of the attack. The actor needs some critical infrastructure. A primary part of this infrastructure is a domain name that looks similar enough to be able to fool a user into clicking on a link that will either allow their computer to be compromised or change critical details like a banking routing number. The actor also needs a place to host the server(s) that are going to be used to run the attack, etc.
Let’s look more closely at the domain name and the role it plays. This is the keystone of the attack and without it everything else would fail. This is why at DomainTools we have spent the last year doing research and creating reportsrelated to how phishing domains are constructed, and developing a new tool to help you shore up your defenses and get ahead of the phishers.
PhishEye is the name of the new product, and it was designed to help you find all of the existing domains that might be currently registered to impersonate you or your brand, and also allow you to monitor those terms and brands that are key to your business. These company and product names might not just be yours, they could be part of your extended corporate ecosystem to include vendors, affiliates, subsidiaries, etc. At PhishEye’s core is a set of algorithms that hunt through our database of over 315 million actively registered domain names for your branded terms, and a very large set of other near misses. These include things like character swaps (1/l, g/q, w/vv, rn/m, etc), fat finger swaps, and look-alike characters (tt/π).
When you set up PhishEye, you start with a term or brand that you suspect might be an abuse target. PhishEye does a lookup of all of the domains that are currently registered that meet any of the variations the algorithm generates. For my example, I started with ‘icloud;’ this returned a result set of 4160 currently registered domains that we found that either had ‘icloud’ in the domain name, or some form of it, like these two:
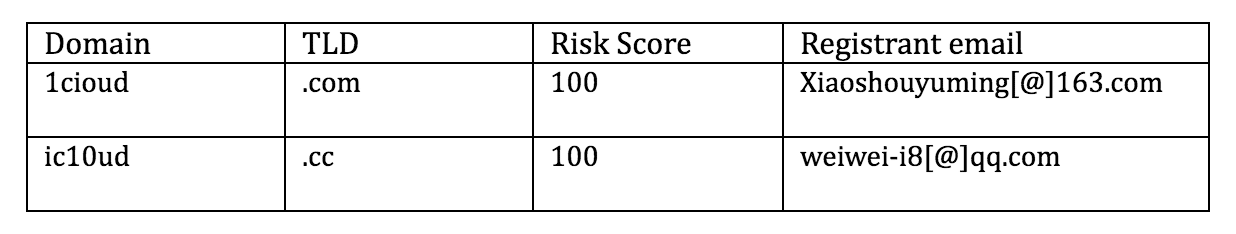
I then just click on a button to start monitoring these, and they are added to my list for alerting. The “Risk Score” is calculated by the DomainTools Reputation Engine.
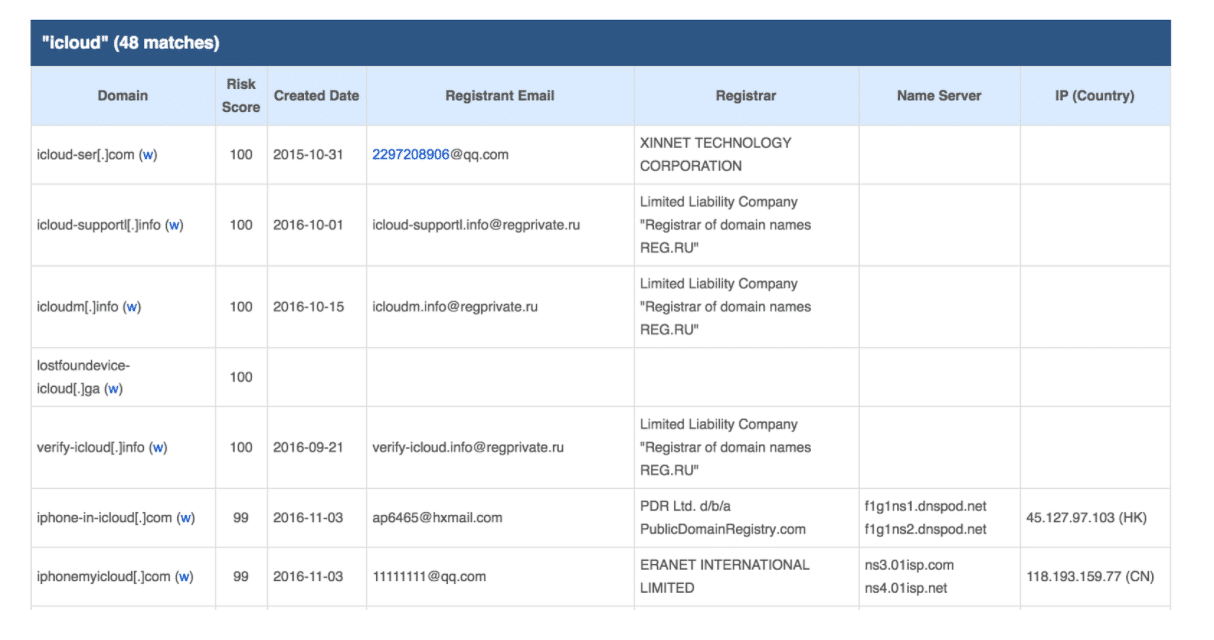
Just like that, I’m done with setting up my first term. After that, I’ll get an email daily with the results of any newly registered domains that meet the search criteria. Here is a clip from my email:
The goal here at DomainTools is to build products that not only allow you to find and track the cyber criminals that are attacking you but to also give you the ability get ahead and stay ahead of them by tracking the infrastructure they are using. When you are alerted to domains being registered every day, then you can begin to move from reactive to proactive.
I like to think about PhishEye as an early warning system. Picture it like this: if a fish in the water could have a early warning system that a fisher was in the area, and that it should take extra caution, knowing that things that swim by are most likely lures and not something you want to eat. That kind of vigilance is what PhishEye was purpose-built to provide.
It’s never ideal when you’re alerted about a phishing campaign by the arrival of the phish itself. “Phinding” those domains that are trying to phish you ahead of time is much better than getting the emergency call at 3 AM!
*For an updated look at phishy domains, see my post about Cyber Monday.

