DomainTools 101: Preparing for Black Frauday Friday

NOTE: Iris Detect has supplanted PhishEye, with dramatically expanded capabilities. Please explore Detect for your brand protection, anti-fraud, and spoof infrastructure analysis needs.
I’d like to go over a few things that you should know before going online to shop on Black Friday, or Cyber Monday.
There are lots of criminals who are at this very moment registering domains and developing websites with a rather nefarious intention; to steal your money. This isn’t just something criminals do the week before launching attacks, they are already creating the necessary infrastructure to infiltrate your computer and wallet months in advance.
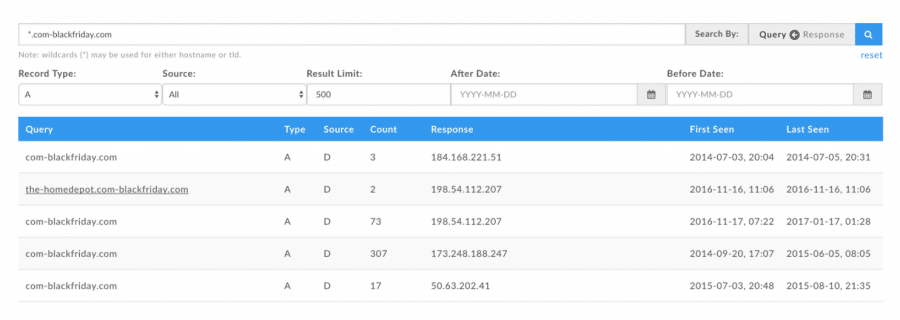
The first thing cyber criminals need to do is set up a domain. They will likely select a particular company with a good reputation, and then search to see what domain names might be available to spoof a brand name or event name, like com-blackfriday[.]com. This domain was re-registered on November 16, 2016, just after the 2016 holiday season. This is a common strategy that helps keep them remain under the radar as long as possible. This strategy minimizes the probability that the domain will get flagged as being a young (under 30 days old) domain. Com-blackfriday[.]com also has the potential to spoof nearly any legitimate company just by using a legitimate company name in the subdomain, (the part of the name that is left of the root domain).
In order to identify whether or not the owner of com-blackfriday[.]com stood up any malicious subdomains that included well-known brand names, I dug into DomainTools’ Iris Passive DNS Data. This uncovered another malicious subdomain: the-homedepot.com-blackfriday[.]com.
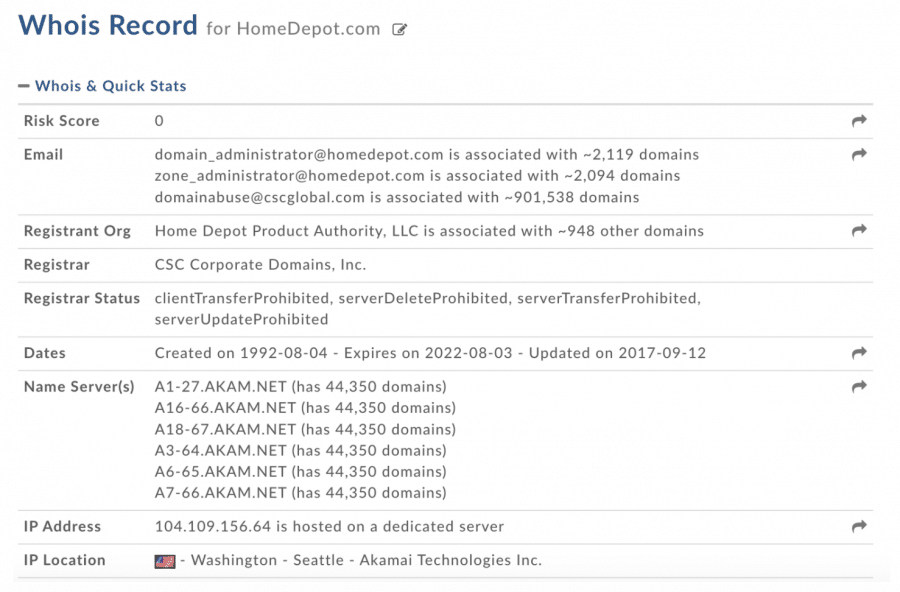
You may be wondering “how can I protect myself against these types of attacks this holiday season?” I recommend that before forking over your credit card to an online retailer, take a moment to look at the Whois record for the domain (which is usually found in promotional emails, or on social media ads). As an example of how to use Whois to protect yourself against holiday phishing scams, let’s run through a scenario involving a phishing email featuring the domain name: the-homedepot.com-blackfriday[.]com. In this situation, I would begin by looking at the Whois record for homedepot.com (the real site).
Next, the imposter com-blackfriday[.]com;
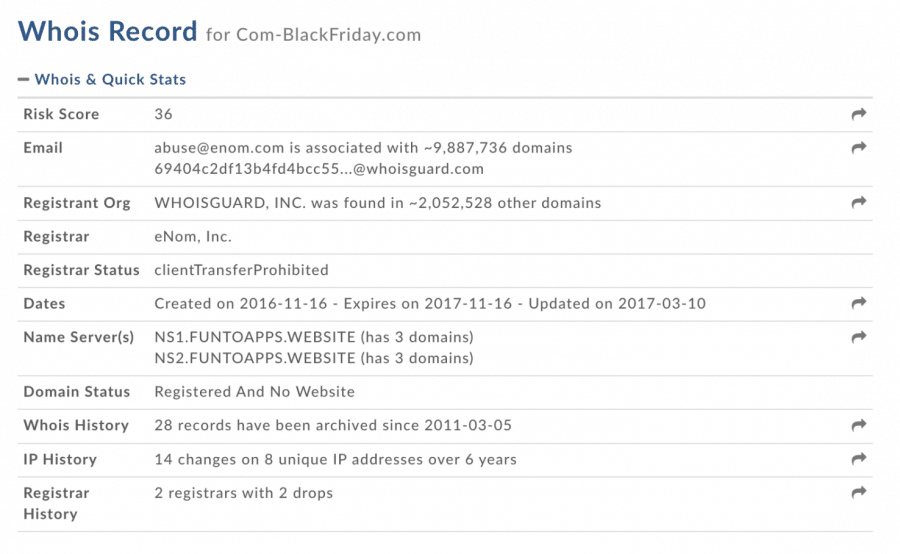
There are plenty of key differences in these domains, let’s start with the Risk Score. The Risk Score is assigned by DomainTools and shows how closely related a domain is to known bad domains or domains appearing on industry blocklists. A score of 100 means that a domain is already considered bad, and has been added to an industry blocklist. Anything less than 100 is our predictive score, and demonstrates how likely it is for that domain to end up on an industry blocklist. Homedepot.com which has a risk score of 0, was registered by Home Depot and has been around since 1992. Com-BlackFriday[.]com has a risk score of 36, but has been registered and dropped several times and currently doesn’t have a website. This domain was registered behind privacy, which is another red flag. These are just two examples of data points that do not match between the real and fake domain.
To give you an idea about how actively they are planning, I set up a monitor with DomainTools PhishEye, for the term “blackfriday” and here are some of the interesting results;
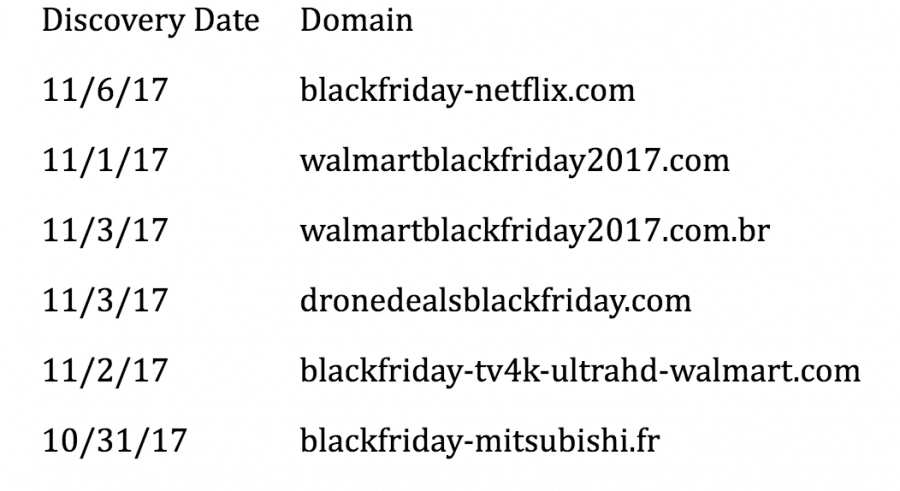
These are just some of the domains that contained names of companies and products you might recognize. Since I started monitoring on Oct 31, there have been 317 “blackfriday” domains registered.
There are countless examples of cyber criminals using these strategies to successfully phish consumers this holiday season. However, if you are willing to take just a moment to do some research, you can save yourself quite a bit of pain.
Safe shopping!

