DomainTools 101: Rent an IP, Own a Domain

The other day I was on a mission to locate a contact of mine that lived nearby. I had an address, but no phone, or email address. So I got the GPS out, programmed in the address, and away I went.
Arriving at the location, I turned into the driveway, and it was an apartment complex. Hmm, no apartment number…this is not as simple as I’d imagined it would be. So I quickly knocked on a couple of doors and of course no one knew him. Back to square one.
I was thinking about this, and how it applied to how we look for badness on the Internet. We have all been trained that the Internet runs on IP addresses and that DNS is used to translate domain names to IP addresses. So why isn’t an IP address enough?
Try to imagine a delivery service that has a rule that won’t let it deliver packages to known criminal addresses. As a driver for that service, I have an address that gets flagged by our malicious address tracking service as being a known criminal address. The software that we use to set up our deliveries gets that feed, and now blocks my ability to deliver packages there. That all sounds really good and safe, except for one thing, that address is a high rise apartment building with over 500 legitimate residents that have done nothing to run afoul of the law. But now I’m not able to deliver their packages because our software is blocking my ability to do so.
So let’s see how we can apply this to the current state of the internet. Criminals are well aware of how they can hide their domains on a service that hosts lots of other good domains, and how effective it is to be able to hide amongst those non-malicious domains.
The quick answer as to why domain names are critical in hunting for malicious actors is HTTP 1.1. Before 1.1, an IP address was enough as there was a direct one-to-one relationship. Since HTTP 1.1, you can host multiple domains on a single IP address, and so much like my trip to the apartment complex without an apartment number, you need to have the domain to properly identify the domain that you’re looking for. Just like me not having an apt number to refine my search, not having a domain name means you are likely to hit the same dead end.
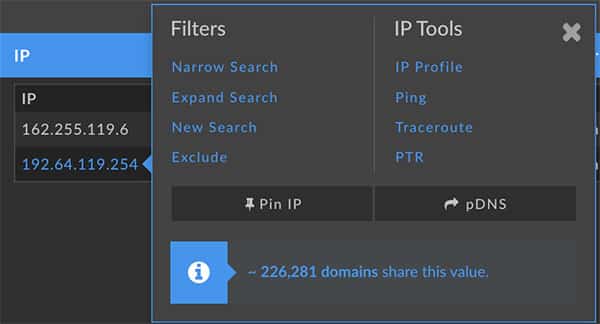
As you can see from the image below on a single IP address there are around 226,000 domains hosted.
Starting with HTTP 1.1, one server at one IP address can be multi-homed, i.e. the home of several Web domains. For example, “www.host1.com” and “www.host2.com” can live on the same server.
Several domains living on the same server is like several people sharing one phone: a caller knows who they’re calling for, but whoever answers the phone doesn’t. Thus, every HTTP request must specify which host name (and possibly port) the request is intended for, with the Host: header.
Many times I’ll see a post that says that IP address x.x.x.x is hosting an Exploit Kit, or has been compromised, and so I do a quick reverse IP lookup to find the domain name and see that there are 5, or 500 domains hosted on that IP. Therefore, I have to ask the author of the post which domain is the bad one.
The second reason is that the threat actors we’re searching for own the domain, but are renting the IP address that is hosting the site. “Rented IPs” can be changed when needed, for instance when they begin to notice that they aren’t getting the traffic they need, so they will move their domain to a different hosting provider, or to a different IP address at the same hosting provider. With DomainTools Iris Investigate, I can look up where they are currently hosted, and where they have been hosted previously. This is one of the ways the threat actors are looking to stay ahead of us, but with Iris Investigate we can begin to get ahead of them.
I know we’d all like to just be able to block at the IP level, as it is simple and quick, but with so many domains hosted at sites that can host hundreds, or thousand of domains, or that are behind a reverse proxy server like CloudFlare, we really need the domains to do a good search.
Our goal at the end of the day is to be able to get ahead of the threat actors by finding and monitoring all of their connected infrastructure.

