Elevate Your Risk Perception With Early Detection Using Domain Monitors
I have a confession.
I set up domain monitors for fun.
No, really! My job responsibilities are all internal. I’m here to improve the security posture, awareness, and surface area of the company. This doesn’t involve tracking anything that’s not a threat to us, writing blog posts, or anything else! But once DomainTools brought me on and gave me a shiny new set of tools to use, I dove right in to see what I could accomplish.
Iris Investigate and Iris Detect turned out to not just be useful, but also fun for me. So I began setting up monitors upon monitors and tracking them week over week to watch suspicious sites rise up, and even identify coordinated malicious campaigns by taking just a few minutes a day.
Which is how I stumbled across 0ktapus months before it came to light – though I didn’t know at the time quite what I was looking at.
The 0ktapus’s Garden
For the sake of simplicity let’s start off where any good story does: smack dab in the middle. On August 25 2022, Group-IB published a blogpost about a coordinated campaign they were currently investigating. One month prior, on July 26, a Group-IB client requested their assistance after a phishing attack. Investigators identified not just one campaign but a coordinated, concerted effort to obtain Okta credentials and 2-factor authentication codes for a number of targeted organizations.
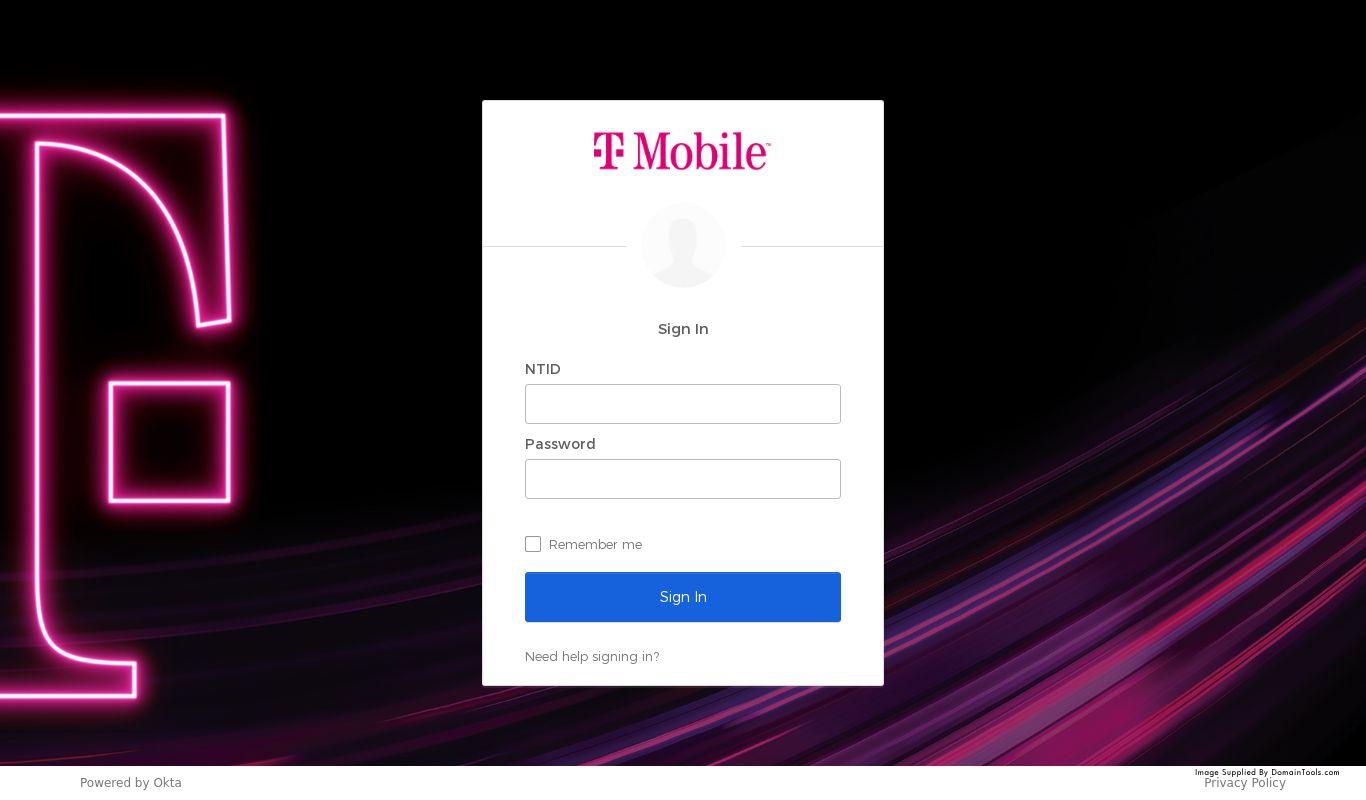
0ktapus utilized domains impersonating the Okta authentication page of these companies to distribute phishing kits and lure employees to spartan, but vaguely legitimate-looking landing pages where their credentials would be harvested. Additionally, the landing page attempted to force a download of the AnyDesk remote administration tool as well as a proper phishing kit. Post-compromise exploitation led to data being exfiltrated to a Telegram channel found in the code.
Target breakdown shows heavy skew toward the software industry, telecom companies, and business services, with a scattered long tail of other (likely opportunistic) hits. Targets were overwhelmingly but not exclusively headquartered in the United States – 114 organizations, versus the next closest country, India, with four.
At last glance, Group-IB had very clearly and strongly identified a subject of interest involved in these campaigns but kept their identity confidential to enable law enforcement to investigate and act further.
The Realities of Limited Risk Perception
My first significant career was as a police dispatcher crewing the 911 desk, business phones, and radio system of a small town police department. One of the many things I learned in that job was an understanding of the blinders that people walk around with every day, their inability to perceive the environment around them and their own limited context within it. As an example, let me share one of my favorite calls, from the moments after a rare small New England earthquake.
Me: 911, this line is recorded, what is your emergency?
Caller: I think there was just an earthquake!
Me: Yes, the US geological service recorded a small earthquake in the area. Is anyone injured? Any damage?
Caller: No, I just wanted to make sure you knew. Was it… was it all over town?
Reader, it was at that point that I chose to remain mute and let that question reverberate in the silence between us. It took longer than I’d like, but the caller soon realized the problem with their question: our town of three thousand people did not have its own tectonic plate, and something like an earthquake did indeed affect the world beyond our borders.
Along with many other calls, that incident informed me about how most people operate in the world day-to-day, and the limited perception they employ as they go about their business. This lesson intersects with security in a big way through the lens of risk perception – which is probably a topic for another post wholly on its own, but suffice to say that risk perception for most people only includes profile elements immediately relevant to them. Anything beyond the prioritization mapping they’ve erected internally doesn’t rate much consideration, and this is how people get into trouble. This problem comes home to roost when employees of a targeted organization don’t have a deep grasp of what services the company uses and what authentic interaction with those services should look like. We can only keep so much in mind at any given point, and our brains weigh heavily on the scale in favor of personal priorities. Security usually isn’t one.
Another set of teachable moments from that job involves criminal activity in civilian contexts. Our jurisdiction included multiple beautiful and well-maintained nature trails that brought in hikers from across the state. Each year as the weather brightened, post-winter thawed out folks would park in remote areas for a pleasant walk in the woods only to come back to their car several hours later and find their windows smashed and items stolen. Risk perception similar to the above factors in here – why you’d leave a purse, an expensive phone, or a whole back seat of camera gear unattended never failed to confuse me – but a valuable lesson emerged in that criminals prefer the periphery. There are exceptions to this, of course; being in a busy area allows for a certain amount of anonymity. But on the whole, physical criminal operations prefer to operate in peripheries for the same reason that cybercriminals do: less visibility, less vulnerability, and easier exfiltration.
Why are Phishing Attacks so Successful?
Now we come to where practice and principles collide:
- Most people engage in overly-limited risk perception, unable to process much outside their immediate environment and personal priorities. This applies to both physical and virtual worlds.
- Criminals prefer to strike in the periphery rather than at a supernode or core in both physical and virtual worlds; a motor vehicle break-in at a quiet hiking area shares some characteristics with an HVAC vendor or employee personal asset compromise that pivots to the main target: they employ networks, pathing, and infrastructure patterns.
The juxtaposition of those two principles means that our subjects here are also intertwined: namely, why phishing attacks are so successful, and why domain monitoring is so successful in early detection of phishing attacks. All of the above informs my approach: if I want to see who’s targeting an organization, I want to look at what passive DNS and newly observed or newly active domains reveal about services the organization uses. The SaaS (software as a service) infrastructure is the periphery.
So, is someone lurking around the SaaS infrastructure of my org like a drifter with a rock, ready to break a window? Well, much like the surveillance we can do on the real-world periphery, domain monitoring allows us to keep an eye on our SaaS periphery as well.
Registration of Suspicious Okta Domains
Identity and authentication platform Okta had a tough year. A subcontractor breach gave them all the headlines that no company wants, and bungled communications lost them quite a bit of trust. Their popularity also makes them a big target on the playing field, and so I’ve had relevant domain monitors setup since March 2022.
In May and June these monitors began paying off in a big way. A flurry of sites began to pop up with “okta” and/or SSO in them. That’s not always indicative of suspicious activity, but three things stuck out:
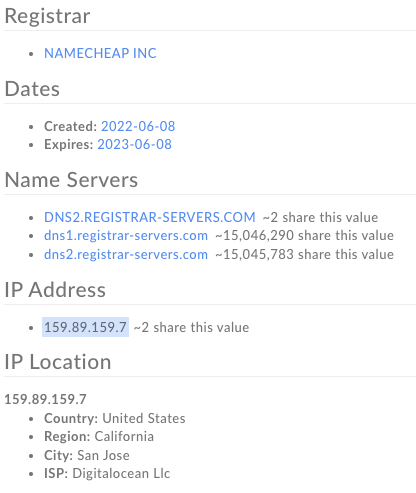
- The pages all fit a particular domain profile (registered with Namecheap or CSC, hosted on Linode or DigitalOcean) and in each case substantially diverged from the profile of the primary domain. This often included deviations in registrar, host IP and ASN, nameserver, and mailserver. It’s a tell, but not conclusive – normally you’d expect infrastructure and process to align in certain ways.
- Some of the domains involved in this coordinated activity contained purposeful misspellings that allowed them to visually impersonate the primary domain. Again, not conclusive – these organizations could be pre-emptively registering homoglyph domains so bad actors can’t use them.
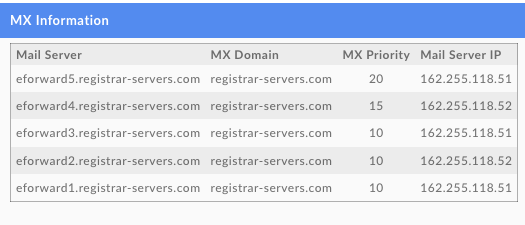
- Most if not all of these domains included an MX record, meaning they were actively routing email and in a different manner than the primary domain.
These three elements together made the collection of domains highly suspicious. In addition, they possessed high risk scores in Iris Detect.
One of the first examples that immediately raised the hair on the back of our necks was okta-tmobiie[.]net. Note the second “i” – suggestive of an intent to capitalize it in practice so the domain appears as okta-tmobiIe[.]net to humans in order to fool them.
The primary domain in this case is t-mobile[.]com – registered through Deutsche Telekom and hosted by Incapsula, as a quick check in the domain profile section of Iris Investigate shows:
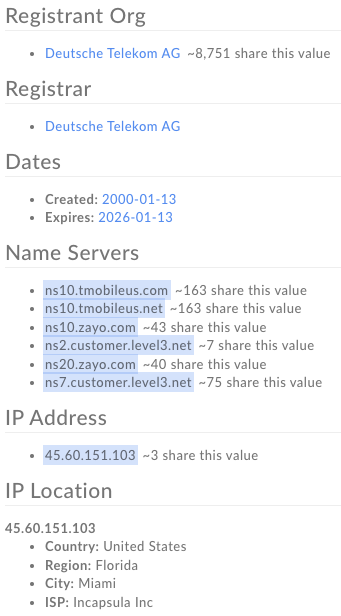
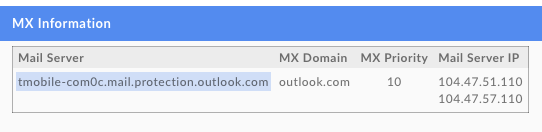
In addition, we can see that the mailserver of the primary domain utilizes Outlook:
When we evaluate okta-tmobiie[.]net, we see a substantially different profile:
DomainTools screenshotting captured images of a common portal element that also helped identify the coordinated pages:
Here’s where tunnel vision enters in a new way: my own. Having originally seen the handful of T-Mobile domains, my assumption that this attack was limited to T-Mobile winnowed my perceptions down. Instead of identifying the more wide sweeping campaign in progress, I instead identified and pursued a subset focused only on the telecom company.
Examples:
t-mobile-okta[.]us
okta-oath[.]com
t-mobile-okta[.]com
okta-tmobile[.]org
Okta-tmo[.]org
Straggler domains fitting a similar profile existed, but my focus on T-Mobile led me to view them as ancillary extensions of a more coordinated campaign focused on one target. A wider search of my monitors yielded results such as binance-okta[.]com, coin-base-okta[.]com, hubspot-okta[.]com and mailchimp-okta[.]com, organizations I monitor due to earlier cryptocurrency-related compromises. But the wider campaign also included keywords like “vpn” and “sso” that vastly increased the scope. By going to the exfiltration location (the aforementioned Telegram channel), Group-IB was able to identify dozens more target organizations.
One important point to note is this, though: the first domain that led me down this path was created 06-08-22, DomainTools crawlers found and screenshot it the same day, and Iris Detect fed it into my domain monitors the same day. It simply took until the next time I checked my external monitors, 06-12-22, to find the whole sordid business waiting for me and begin connecting dots.
The Value of Brand Monitoring in Security Operations
A dedicated SOC team checking monitors daily both around your organization’s brands and keywords, but also around your SaaS periphery, would’ve caught it the day it appeared and been able to take preventative measures both internally and externally.
“Okta” as a keyword domain monitor continues to lay bare the dangers of the internet, SaaS models, and our approach to identity and authentication. But the right infrastructure monitoring out on that wider internet can easily deliver near- or real-time warnings that someone’s lurking out in the darkness, preparing to pounce.


