Introducing DomainTools PhishEye

NOTE: Iris Detect has supplanted PhishEye, with dramatically expanded capabilities. Please explore Detect for your brand protection, anti-fraud, and spoof infrastructure analysis needs.
It has been a momentous few days, with the familiar landscape suddenly looking very different. I’m referring, of course, to the cyber threat landscape and the debut of DomainTools PhishEye, a potent new tool in the fight against look-alike domains that mimic legitimate online resources in the effort to lure victims into clicking things they shouldn’t.
A central premise of the work we’re doing at DomainTools is that organizations are looking to move from a reactive stance to a proactive one. As things stand today, all too often, the first alert that organizations get about a phishing attempt or campaign is the phishing email itself. That’s definitely not the alerting system you want. PhishEye is designed to help the organization get ahead of phishing attempts, moving from a reactive posture to a preventive one. By identifying domains that are crafted to imitate legitimate domains as soon as they come into existence, PhishEye helps the security team create custom blocklists based specifically on the keywords that matter the most to them–typically their company name or brand names, or those of other companies in their ecosystem, such as suppliers, subsidiaries, partners, and the like.
How it works
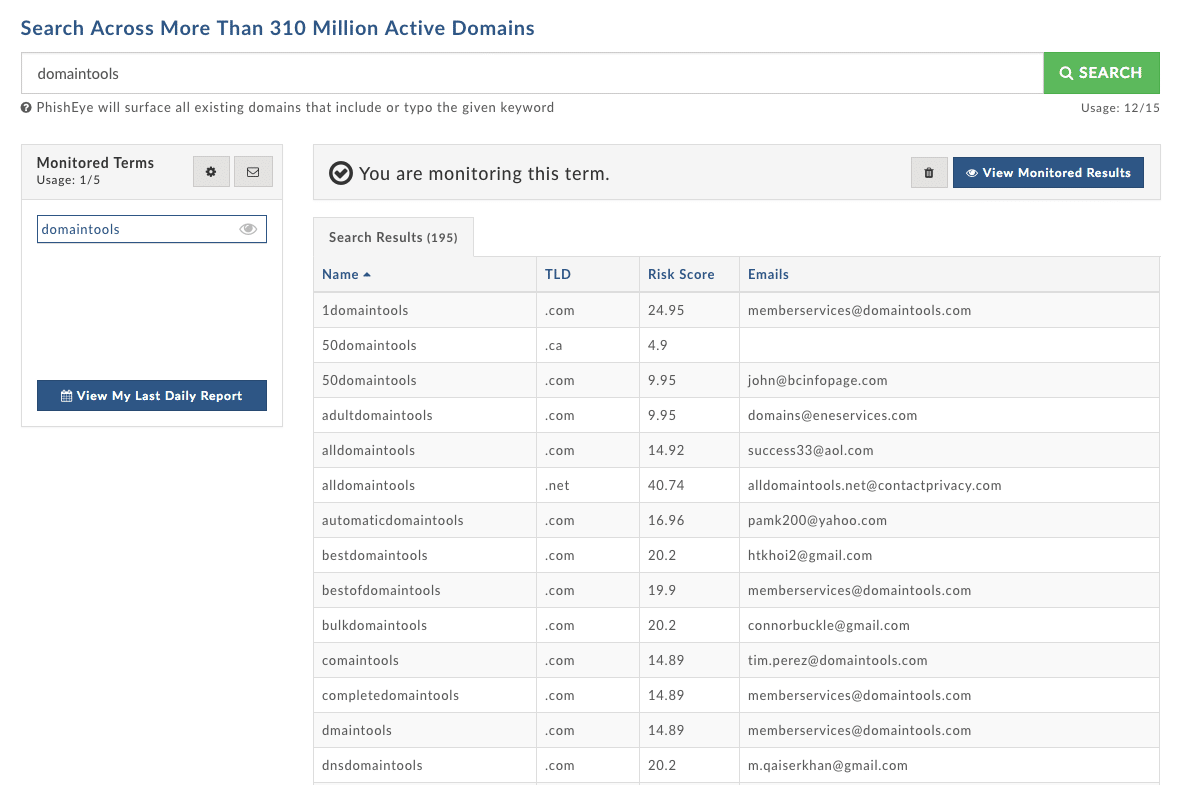
Phishing depends on domains, so if you can identify and block the domains in question, you disrupt the attack. PhishEye takes keywords that you supply, and generates a list of possible variants of that keyword. These variants include typos (such as domaint00ls, and many other ‘species’ of morphed spelling) and substring inclusions (such as domaintoolsaccount). Then PhishEye searches our database of around 315 million current domains to identify offending domains that exist. Finally, and perhaps most importantly, you can set up alerts so that you get notified when PhishEye discovers new matching domains. You can take these names and create custom blocklists to deny the phishing traffic, whether that comes in the form of the “from” domain in the phish, or a malicious link, or both.
Phishing affects everyone, but the risk from spear phishing is especially acute for businesses. (Individuals get phished on their private email accounts, too, but those phishes are often “419” scams and the like—widespread, opportunistic attacks hoping to prey on ignorance or distraction). We encourage you to have a look at PhishEye; we believe it will be a valuable tool in your efforts to help keep the cyber landscape as safe as possible. To learn more about PhishEye, watch the recorded webinar. Let us know what you think: [email protected] or on Twitter: @DomainTools.

