Reopen Domains: Shut the Front Dorr
Update: We noticed that while working on this piece Brian Krebs posted an excellent article on the same. What can we say, but great minds think alike? Since we dug into different pieces we have decided to post as well.
If you would prefer to listen to The DomainTools Research team discuss their analysis, it is featured in our recent episode of Breaking Badness, which is included at the bottom of this post.
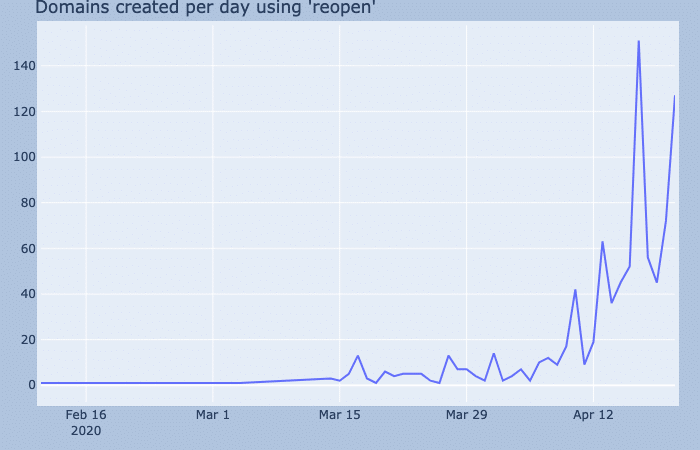
Late on Sunday night we came across a fantastic reddit comment by a user named Dr_Midnight that detailed how they suspected that a number of the state-based reopenmn[.]com or reopenmd[.]com domains were all registered on GoDaddy at the same time and within seconds of each other. This led them to suspect that the reopen America protests were not a grassroots campaign, but actually a coordinated astroturfing—or fake grassroots—effort. Being that infrastructure intelligence is our speciality, we decided to dig a bit further into what we could find for that day.
Hunting
Initially we performed a query for every domain registered on that day that started with “reopen”. Looking at the output sorted by time you can see the obvious patterns mentioned by the user on reddit as well as additional domains to what they found. We have marked the batches in alternating colors when they belong to a registration time within a few short moments of one another. There is a separator between those registered on April 8th that were mentioned in the reddit thread and those registered in larger batches on April 17th.
| Domain | Registration Time |
|---|---|
| reopenaustralia.com | 2020-04-08T13:08:17+00:00 |
| reopenohio.com | 2020-04-08T14:36:33+00:00 |
| reopenpa.com | 2020-04-08T14:37:29+00:00 |
| reopenmn.com | 2020-04-08T14:39:17+00:00 |
| reopeniowa.com | 2020-04-08T19:40:56+00:00 |
| reopenwyoming.com | 2020-04-08T19:43:57+00:00 |
| reopenmissouri.com | 2020-04-08T19:46:05+00:00 |
| reopenamericabusiness.com | 2020-04-17T00:01:02+00:00 |
| reopencanow.com | 2020-04-17T00:54:53+00:00 |
| reopenamericanbusinesses.com | 2020-04-17T01:38:36+00:00 |
| reopenalaska.com | 2020-04-17T03:25:52+00:00 |
| reopenarkansas.com | 2020-04-17T03:25:52+00:00 |
| reopendelaware.com | 2020-04-17T03:25:52+00:00 |
| reopengeorgia.com | 2020-04-17T03:25:52+00:00 |
| reopenconnecticut.com | 2020-04-17T03:25:54+00:00 |
| reopenhawaii.com | 2020-04-17T03:25:54+00:00 |
| reopenidaho.com | 2020-04-17T03:25:54+00:00 |
| reopenillinois.com | 2020-04-17T03:25:54+00:00 |
| reopencolorado.com | 2020-04-17T03:25:55+00:00 |
| reopenindiana.com | 2020-04-17T03:32:58+00:00 |
| reopenlouisiana.com | 2020-04-17T03:32:59+00:00 |
| reopenmaine.com | 2020-04-17T03:33:01+00:00 |
| reopenmassachusetts.com | 2020-04-17T03:33:01+00:00 |
| reopenmontana.com | 2020-04-17T03:33:01+00:00 |
| reopennebraska.com | 2020-04-17T03:38:28+00:00 |
| reopennewhampshire.com | 2020-04-17T03:38:28+00:00 |
| reopennewmexico.com | 2020-04-17T03:38:28+00:00 |
| reopennorthcarolina.com | 2020-04-17T03:38:28+00:00 |
| reopenpennsylvania.com | 2020-04-17T03:38:28+00:00 |
| reopennorthdakota.com | 2020-04-17T03:38:29+00:00 |
| reopenoregon.com | 2020-04-17T03:38:29+00:00 |
| reopenrhodeisland.com | 2020-04-17T03:46:10+00:00 |
| reopensouthcarolina.com | 2020-04-17T03:46:10+00:00 |
| reopenutah.com | 2020-04-17T03:46:10+00:00 |
| reopensouthdakota.com | 2020-04-17T03:46:11+00:00 |
| reopenwestvirginia.com | 2020-04-17T03:46:11+00:00 |
| reopenwisconsin.com | 2020-04-17T03:46:11+00:00 |
| reopentennessee.com | 2020-04-17T03:46:12+00:00 |
| reopenvermont.com | 2020-04-17T03:46:12+00:00 |
| reopenvirginia.com | 2020-04-17T03:46:12+00:00 |
| reopenwashington.com | 2020-04-17T03:46:12+00:00 |
| reopenunitedstates.com | 2020-04-17T03:52:24+00:00 |
| reopenconn.com | 2020-04-17T04:09:39+00:00 |
| reopenma.com | 2020-04-17T04:09:39+00:00 |
| reopenmass.com | 2020-04-17T04:09:39+00:00 |
| reopencal.com | 2020-04-17T04:09:40+00:00 |
| reopencalif.com | 2020-04-17T04:15:15+00:00 |
| reopenala.com | 2020-04-17T04:15:16+00:00 |
| reopenariz.com | 2020-04-17T04:15:17+00:00 |
| reopenark.com | 2020-04-17T04:15:17+00:00 |
| reopencolo.com | 2020-04-17T04:15:17+00:00 |
| reopendc.com | 2020-04-17T04:15:17+00:00 |
| reopendel.com | 2020-04-17T04:15:18+00:00 |
| reopenfla.com | 2020-04-17T04:15:18+00:00 |
| reopenga.com | 2020-04-17T04:19:12+00:00 |
| reopenill.com | 2020-04-17T04:19:12+00:00 |
| reopenkans.com | 2020-04-17T04:19:12+00:00 |
| reopenky.com | 2020-04-17T04:19:12+00:00 |
| reopenind.com | 2020-04-17T04:19:13+00:00 |
| reopenla.com | 2020-04-17T04:19:16+00:00 |
| reopenmd.com | 2020-04-17T04:19:16+00:00 |
| reopenx.com | 2020-04-17T04:29:06+00:00 |
| reopenmiss.com | 2020-04-17T04:43:36+00:00 |
| reopenmo.com | 2020-04-17T04:43:36+00:00 |
| reopennmex.com | 2020-04-17T04:43:37+00:00 |
| reopenoreg.com | 2020-04-17T04:43:41+00:00 |
| reopenmont.com | 2020-04-17T04:43:42+00:00 |
| reopenndak.com | 2020-04-17T04:43:42+00:00 |
| reopenneb.com | 2020-04-17T04:43:42+00:00 |
| reopennev.com | 2020-04-17T04:43:42+00:00 |
| reopenokla.com | 2020-04-17T04:43:42+00:00 |
| reopenore.com | 2020-04-17T04:43:42+00:00 |
| reopenri.com | 2020-04-17T04:43:42+00:00 |
| reopensdk.com | 2020-04-17T04:43:46+00:00 |
| reopentenn.com | 2020-04-17T04:43:46+00:00 |
| reopentex.com | 2020-04-17T04:43:46+00:00 |
| reopenva.com | 2020-04-17T04:43:46+00:00 |
| reopenvt.com | 2020-04-17T04:43:46+00:00 |
| reopenwash.com | 2020-04-17T04:43:47+00:00 |
| reopenwis.com | 2020-04-17T04:43:47+00:00 |
| reopenwva.com | 2020-04-17T04:43:47+00:00 |
| reopenwisc.com | 2020-04-17T04:43:50+00:00 |
| reopenwyo.com | 2020-04-17T04:43:50+00:00 |
| reopenmich.com | 2020-04-17T04:47:35+00:00 |
| reopeningschools.com | 2020-04-17T06:23:30+00:00 |
| reopeningbars.com | 2020-04-17T06:34:29+00:00 |
| reopeningbaseball.com | 2020-04-17T06:34:29+00:00 |
| reopeningbasketball.com | 2020-04-17T06:34:29+00:00 |
| reopeningcasinos.com | 2020-04-17T06:34:29+00:00 |
| reopeningdaycares.com | 2020-04-17T06:34:29+00:00 |
| reopeningfootball.com | 2020-04-17T06:34:29+00:00 |
| reopeningrestaurants.com | 2020-04-17T06:34:29+00:00 |
| reopeningsports.com | 2020-04-17T06:34:29+00:00 |
| reopeningstadiums.com | 2020-04-17T06:34:29+00:00 |
| reopeningtheaters.com | 2020-04-17T06:38:54+00:00 |
| reopensd.com | 2020-04-17T12:30:02+00:00 |
| reopenamericanbusines.com | 2020-04-17T12:32:16+00:00 |
| reopensmericanbusiness.com | 2020-04-17T12:32:34+00:00 |
| reopenamericanbuisness.com | 2020-04-17T12:32:48+00:00 |
| reopenia.com | 2020-04-17T13:53:22+00:00 |
| reopenal.com | 2020-04-17T13:53:23+00:00 |
| reopenar.com | 2020-04-17T13:53:23+00:00 |
| reopenaz.com | 2020-04-17T13:53:23+00:00 |
| reopenin.com | 2020-04-17T13:53:23+00:00 |
| reopennm.com | 2020-04-17T13:53:24+00:00 |
| reopenwv.com | 2020-04-17T13:53:24+00:00 |
| reopenhi.com | 2020-04-17T13:53:25+00:00 |
| reopenil.com | 2020-04-17T13:53:25+00:00 |
| reopenms.com | 2020-04-17T13:53:25+00:00 |
| reopenmt.com | 2020-04-17T13:53:25+00:00 |
| reopentn.com | 2020-04-17T13:53:25+00:00 |
| reopenwy.com | 2020-04-17T13:53:25+00:00 |
| reopenco.com | 2020-04-17T13:53:29+00:00 |
| reopende.com | 2020-04-17T13:53:29+00:00 |
| reopennd.com | 2020-04-17T13:53:29+00:00 |
| reopenne.com | 2020-04-17T13:53:29+00:00 |
| reopenoh.com | 2020-04-17T13:53:29+00:00 |
| reopenor.com | 2020-04-17T13:53:29+00:00 |
| reopenut.com | 2020-04-17T13:53:29+00:00 |
| reopenak.com | 2020-04-17T13:53:30+00:00 |
| reopenks.com | 2020-04-17T13:53:30+00:00 |
| reopenme.com | 2020-04-17T13:53:30+00:00 |
| reopeninghuntsville.com | 2020-04-17T13:59:26+00:00 |
| reopenamerican.com | 2020-04-17T14:34:06+00:00 |
| reopenamericanbussiness.com | 2020-04-17T14:34:08+00:00 |
| reopenamericanbusness.com | 2020-04-17T14:46:49+00:00 |
| reopenamericanbisiness.com | 2020-04-17T14:46:51+00:00 |
| reopenamercanbusiness.com | 2020-04-17T14:46:53+00:00 |
| reopenamericnabusiness.com | 2020-04-17T14:46:55+00:00 |
| reopenamercianbusiness.com | 2020-04-17T14:46:57+00:00 |
| reopenncnow.com | 2020-04-17T16:39:55+00:00 |
| reopenamerika.com | 2020-04-17T17:06:00+00:00 |
| reopeningofamerica.com | 2020-04-17T17:48:26+00:00 |
| reopen-usa.com | 2020-04-17T19:02:25+00:00 |
| reopentxnow.com | 2020-04-17T21:59:27+00:00 |
The two largest batches here outside of the initial domains from April 8th seem to be the four gram (ex. reopennmex) and the two gram (ex. reopenmt) versions of these domains. While that is telling that these were registered in batch we wanted to find further evidence so decided to write a script that would go and pull additional data we could use from each of the suspicious pages as other reddit users had mentioned that the pages mentioned groups behind them like Minnesota Gun Rights group for reopenmn[.]com.
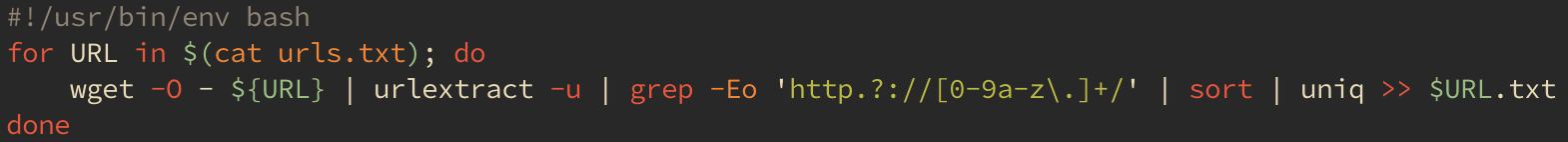
This script simply pulls the main page, extracts the unique URLs, strips them to just their apex domain, sorts them alphabetically, then saves them to a file named after the URL. Afterward we can concatenate all of these together and we have an additional list of suspicious domains to throw into our Iris Investigation Platform to look for similarities.
Findings
These domains fell into a few different groups with varying lengths of rabbit holes to go down so we are going to look at them divided in that way. For starters we do want to say that this does not appear to be some coordinated, large, state-run campaign, but rather a smaller group and then some active registrations. We will explain more of that in detail as we go on.
Batch #1: American Firearms Coalition and the Dorr Brothers
Upon pulling all of these pages and looking through the URLs contained we noticed a pattern that each was a redirect to a state-based firearms coalition group. Each had an action page where they post various political actions like the one calling to end the quarantine and reopen America. The various groups seemed loosely affiliated and seem to be run by different people in each state, but tie back to a Mr. Aaron Dorr. As we looked further we would find that this is a more of a small group’s astroturfing effort.
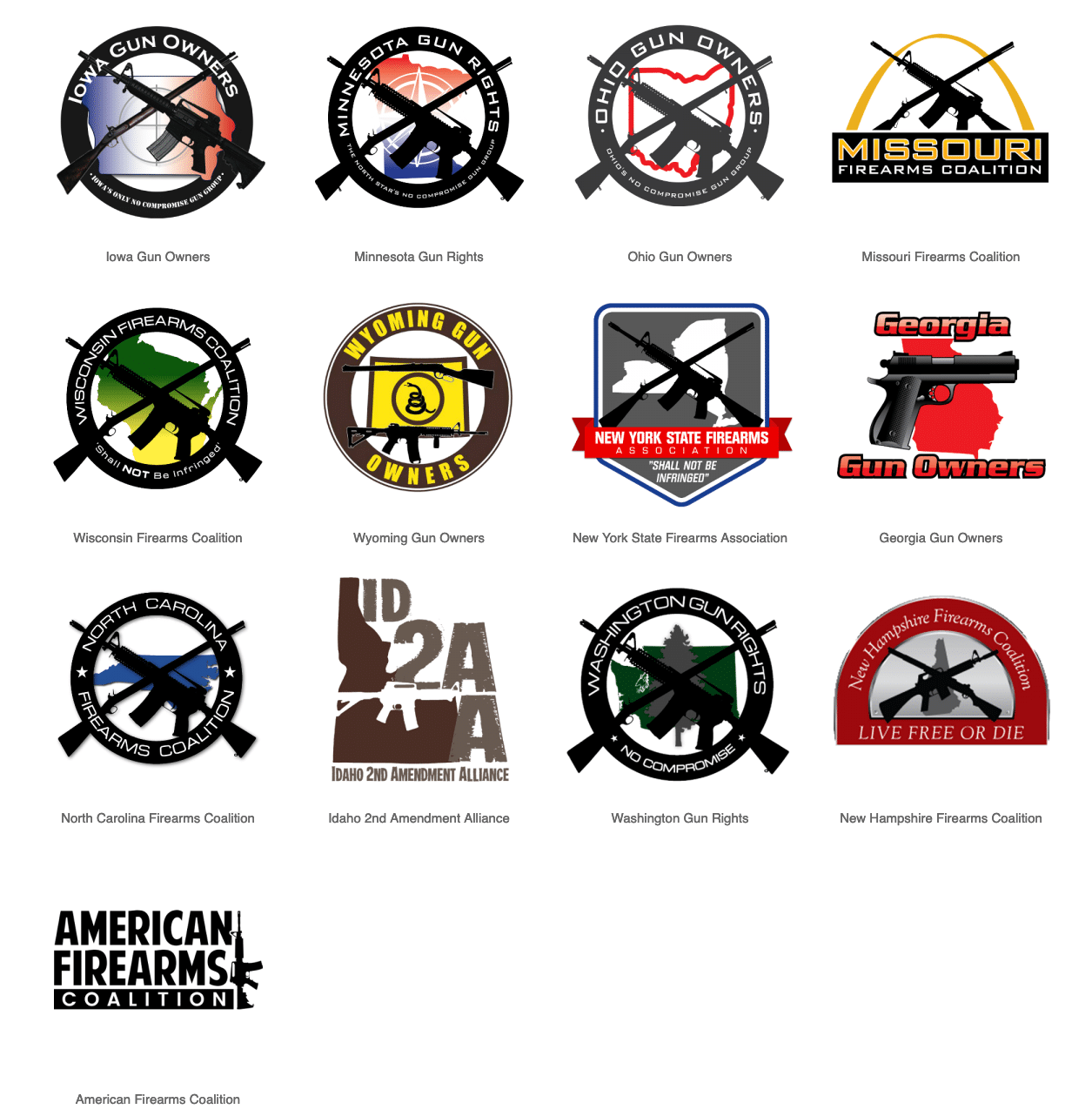
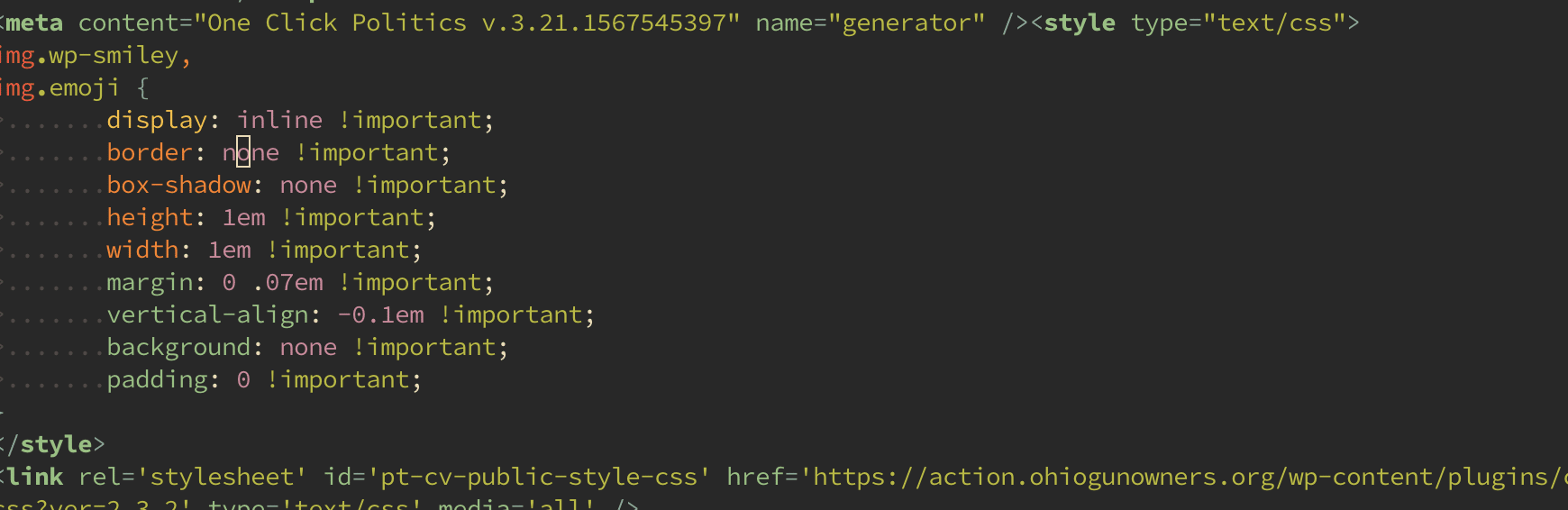
All of these firearm’s coalition sites use One Click Politics, an online advocacy site that enables quick set up of campaigns, as seen by the stylesheet links on their pages. This has allowed for a single person to manage the content on a number of the pages, run email campaigns and collect donations for their groups.
All of the pages also use WordPress and are set up in a similar manner with much the same language, many times entirely identical language outside some swapping of state name or local legislator’s names. At this point we could say that this is an advocacy group that creates templates for people and is likely managed by a single person. We decided to look up all of the phone numbers and addresses provided as contact points on these sites and found the Iowa Gun Owners number belonging to a registered lobbyist for the state of Iowa, Aaron Dorr.
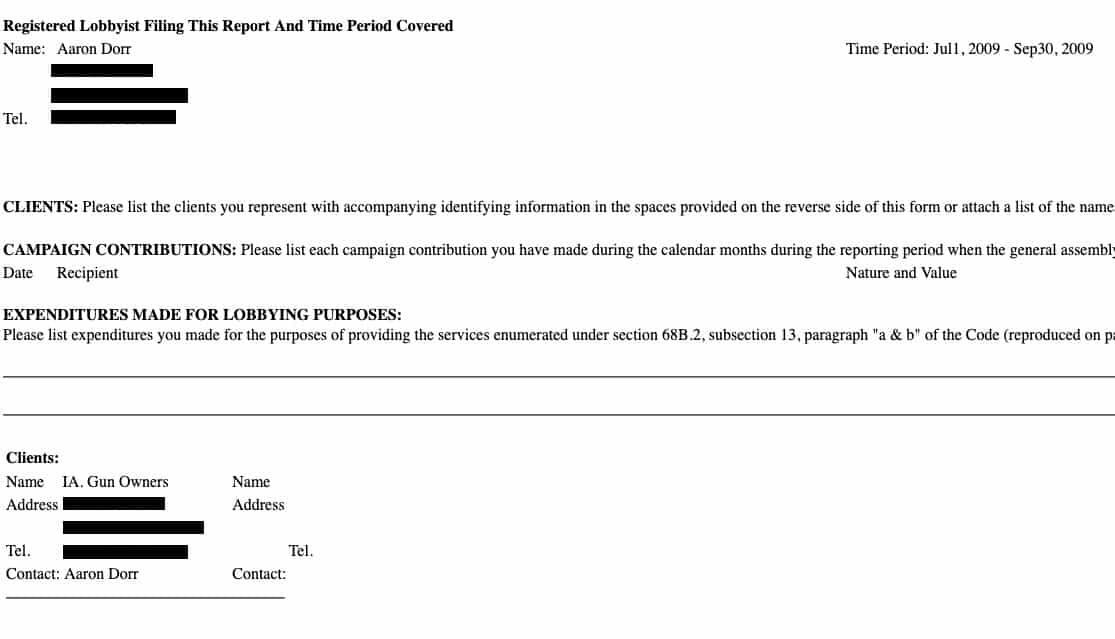
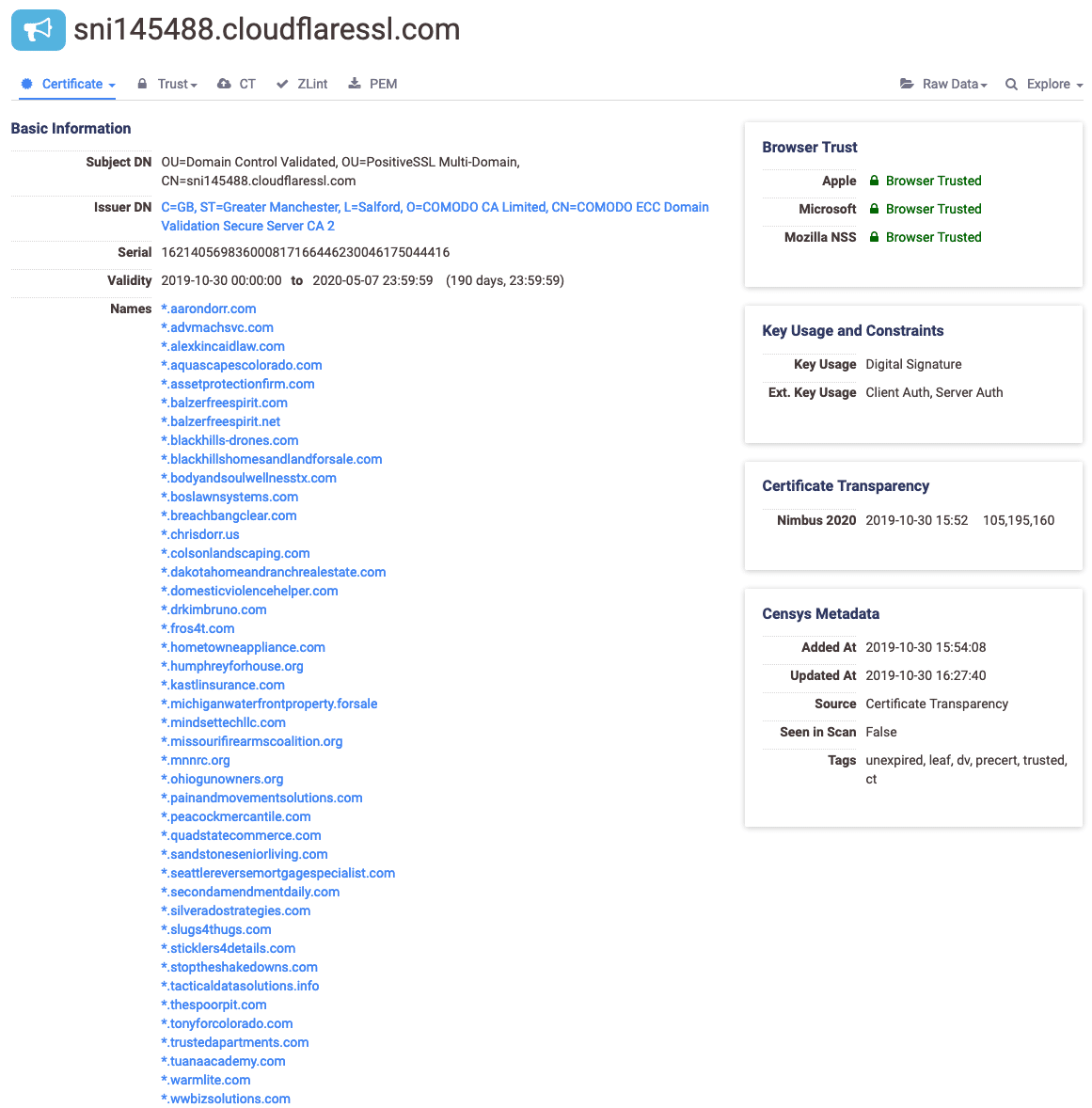
Looking further into the historical SSL certificates used for each of these domains we found Mr. Dorr’s personal domain as well as several other domains associated with other firearm’s coalitions in other states. This raised the likelihood for us that Mr. Dorr was the one running these campaigns.
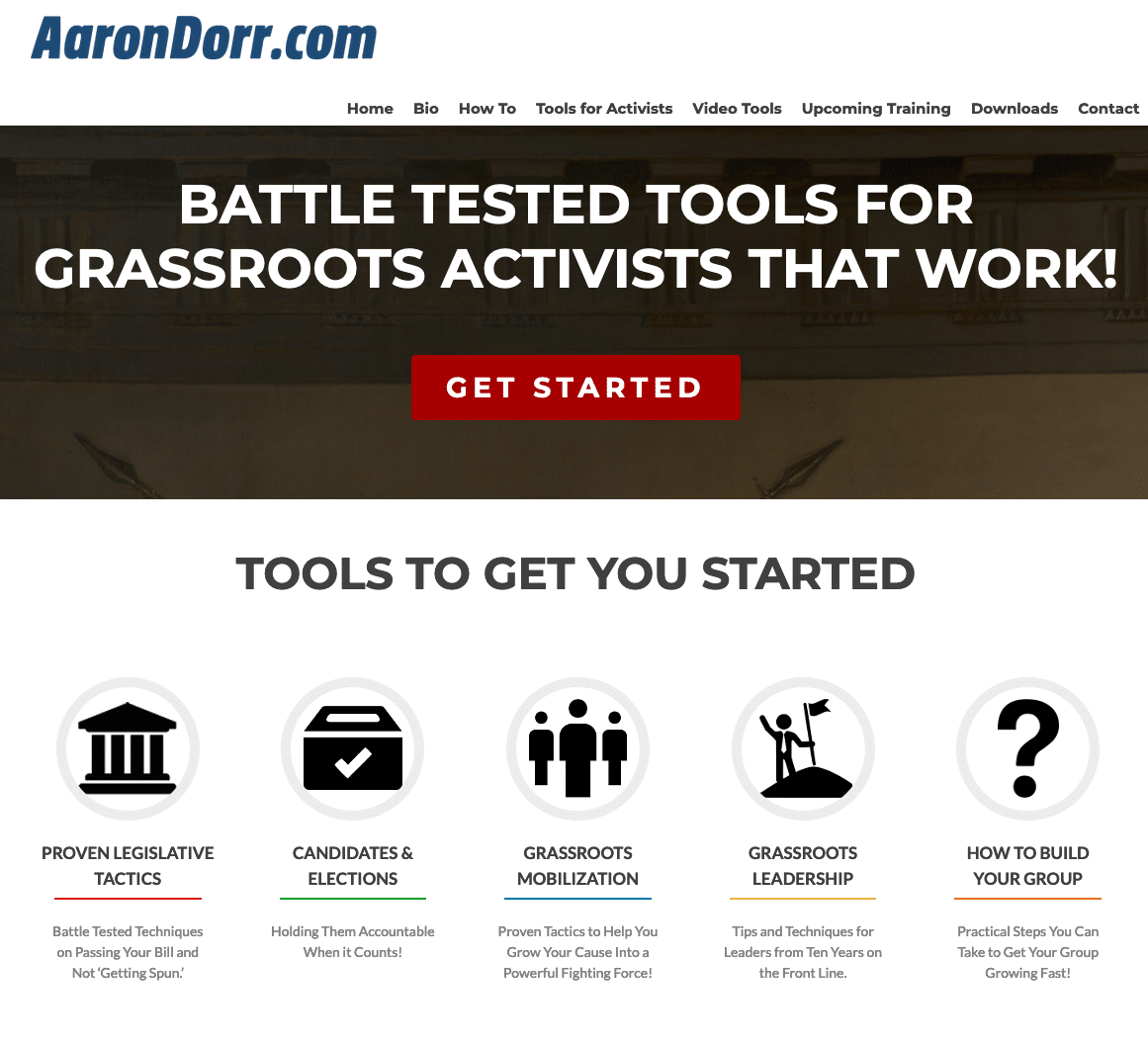
Mr. Dorr does a type of advocacy consulting business where he teaches people to run advocacy groups. You will notice the similarity of the sites from their homepage, similar content and that Mr. Dorr is often listed as the author of the articles published, confirming what we surmised before.
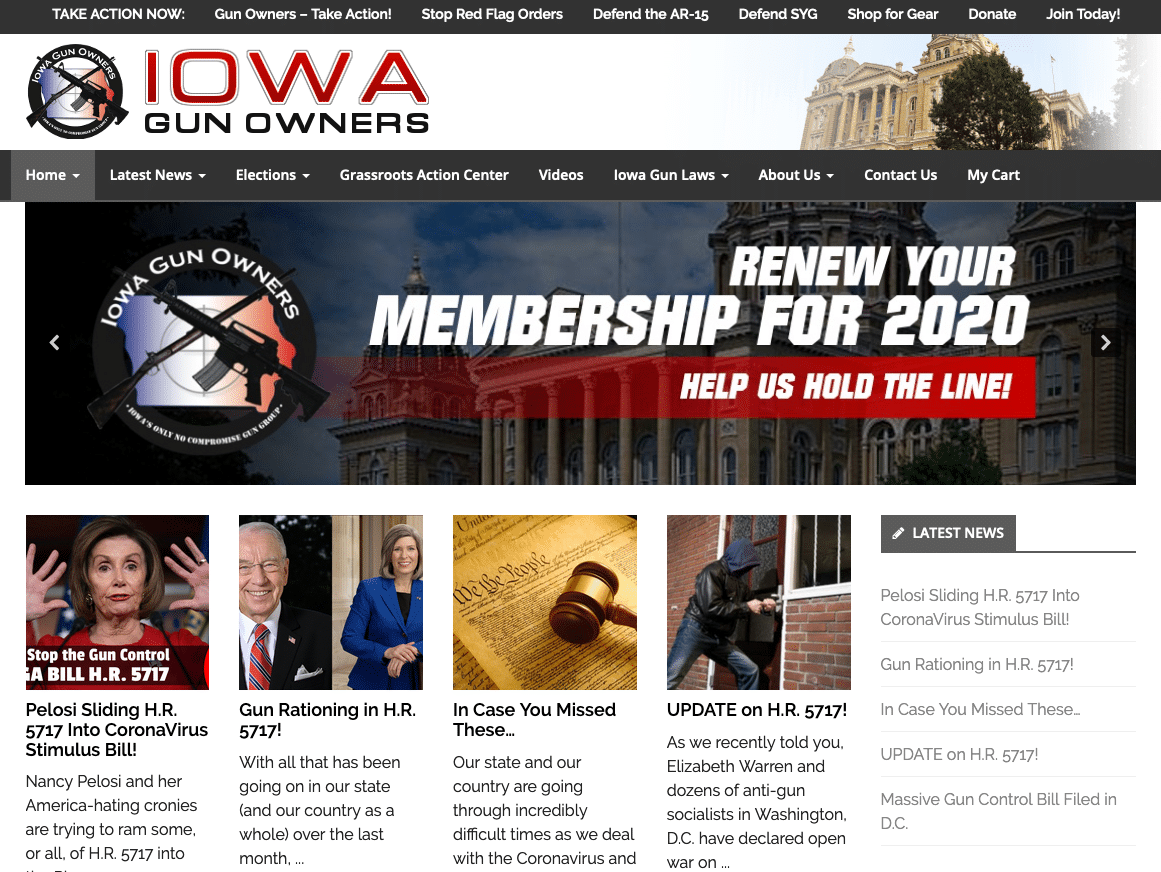

Digging even further on Mr. Dorr it appears that there are already several groups rallying against the firearms coalitions he has built as can be seen with the Facebook page below. These groups are started by other gun owner advocacy groups that find Mr. Dorr’s inflammatory language to raise money through donations when people fear their gun rights are being taken away.

From this we can conclude that these websites are likely all somehow backed or supported entirely by Mr. Dorr. This led us to wonder what else might be under their purview and if we could directly tie through infrastructure these gun coalition domains to one another with even more concrete ties beyond similar page structure, registration and article content.
We decided to start with the iowagunowners[.]org domain exclusively as it is the oldest domain having been registered in 2007. From there you can find several email addresses along with Mr. Aaron Dorr’s name in historical records:
gunrightsadvocate@hotmail[.]com director@iowagunowners[.]com
If we perform a historical search on those email addresses we get back 15 domains in total. From there we can pivot on the Iowa Gun Owners registrant organization which brings us to 18 domains.
aarondorr.com aarondorr.org igofoundation.com igofoundation.org igopac.com igopac.org iowagunowners.com iowagunowners.org iowapersonhood.com iowapersonhood.info iowapersonhood.net iowapersonhood.org oplaa.net oplaa.org slugs4thugs.com thedorrfiles.info thedorrfiles.net thedorrfiles.org
While many of these sit unused, those which are not have been pointed at CloudFlare for their DNS hosting just like the other coalition domains. One of these is igofoundation[.]org which points to the IP address 93[.]179[.]121[.]7 which is on the Russia-based AS of 49352, but looks to currently not be serving any content. Another is slugs4thugs[.]com which name aside redirects to secondamendmentdaily[.]com which is another Dorr run domain serving up firearms-related inflammatory opinion pieces. Lastly, the recently registered Dorr Files domains appear to be working on something new.
Finally we looked at the SPF record for the iowagunowners[.]org domain which showed that they were using BlueHornet, an Enterprise email marketing campaign service. This tied along with all of the NS configuration to CloudFlare, tying these all very confidently back to Mr. Aaron Dorr’s work. In addition we noticed that the donate button on each of the firearms coalition sites links to Anedot, a donation site for churches, charities and non-profit organizations. Almost all configurations for these sites are identical. We can say that these initial domains and the campaign behind them are definitely a small group run astroturfing effort and that the Dorrs’ plan to continue operating these nation-wide campaigns. All in all if you are curious at following these campaigns inside of our Iris Investigate Platform we suggest using the hash provided below as a start for monitoring and further investigations.
U2FsdGVkX1/QlyxrnY042oap85/rOp9KoJuwKWC7s1M2li/YfTWd2kdlO0AZlZSf7o9E4Soj9lbbPdP0UKpuNRp5tSgHFnLIkgveA6TTkwe8ia7yoRFsQeGF1o/5hBgLSuAAbpy7Xuz6+OisIeSHmapJM5t6lCNJuUTZz9cMct8K3BWY80ZLVC+2NKhSJnYgz/d+jlBbthX548/VvJDyrQGR+z4jGMcHUHlEA51KsuerpNAqb45fjxDdcOka0yTMX/v4P9BeH70kdUrFn7jvlaQLWi/siyTrPRtV1zevaCFkeXzzQ9MvQngDTc7zF5UQngr65ZbS4QmsSw6Bg8IQP1FVK2py/Ay3CYbg4+cp/AlLdG//9R32oN9HsoEcMGoqTWdLWCXdACNDtnKMIbmVDutPEbtVjW+3HL3f+jDUD7A4/gKx9pxu+Thkhm4PUcRRaLsd2Vor2YS1x7386wzxJJVr5asif/WvKSwmovPZAYPIvseXmLZs0lj6ddnz4afsBVbHH7gOEt0dGjwxave3tsjzzZmsFQvsP+25kR73PA/2TYZ6dNZnDXw9aSbUU2ihdFNP1xy7zJSUzD0Vp5JF4dNqL6HmohR7y2jHPCf64ANT80qk8xMnZlq5oxTae2+4jDF9O5zrCxcwAQBzmiTzpBZdc+5bEcpQbOM66S9tPqnnpuFoIM1X4AZa1oGzmA2qWAMhE/eFvFTFRB1RGoGIxqC6gtVlUOIpjiXmRBGeQskv3xTUjmIevJuRlUMZl3HrLBrlfjEc38yePWU6nrvgqxyCGqqtRN44OggiFQz/W+XRwglGzvfjPbkyjWnwxqlencYJ9di3loUEBeJ4Regf70FHXg3j8ACZQUtmtF9xE3SzpX+yW6Q1H4f/hh/ZNX2liEKhL7EGFS6eFlRKRpZsJ8haWsXElMXSn4OJbDdN/tP6zjRm45FKc+PLp3GH5U6UwruT44HSHCaCw3GGfbaU1TaF+kWoKZmJk2GQTgry1X+VVB98W8FJh+Ns4yeSzdBjB4ECeLyirJ0zXSZZUnt/Rs/6zMNibIBNHfk4Dlx4VJwm3TJXTXR79cffFoGJvgsk2KqYw9H7FCchOV+jNvqo61j4D+6h5qcTX5AaSqPRFUYu14VshwPrqihIemGWc0bv5rPsv/NK6MSku9OjSIpOXL9fyi4oWi3SO0Q8HAuVttvOxAA7WJfV2NS6X0hRdcRQ1IEtwmVlO1M1AX3/7472H1HwWrnP+hgf0MPTm7KRcDpVIThj9T9SV60sYpOSZteazrkq+FgKGmoikAHS1SjC1Q==
Batch #2: The Loose Links
The second batch of domains were registered in bulk. One can clearly be attributed to the Mr. Aaron Dorr from above (reopentxnow[.]com) as it leads to the American Firearms Coalition we discussed before. The others are disparate and from various groups with 128 domains in total.
Reopen American Business Hong Kong Grouping
The Reopen American Business Hong Kong grouping, including:
reopenamercanbusiness[.]com reopenamercianbusiness[.]com reopenamerican[.]com reopenamericanbusness[.]com reopenamericnabusiness[.]com reopenamericanbisiness[.]com reopenamericanbussiness[.]com
Are all domains that were registered in Chengdu, Sichuan, China on the registrar West263 based in Hong Kong and contain some kind of grammatical error or misspelling. These all point to Bodis which is an advertising services company that monetizes domains. Their network has also previously been associated with the Dark Hotel malware. These currently go to a campaign page and assume that this is just a way to gather user information and possibly monetize these domains through the Bodis advertising agency, but will keep an eye on them in case they turn malicious.
Reopen American Business Linode Grouping
The Reopen American Business Linode grouping, including:
reopenamericabusiness[.]com reopenamericanbusiness[.]com reopenamericanbusines[.]com reopenamericanbusinesses[.]com reopensmericanbusiness[.]com
These domains were all registered with NameKing and point to a Linode server where the domains are currently parked. We will keep an eye on these domains for any further changes as they have the potential to be malicious according to our risk score machine learning algorithm which rates them above the threshold for dangerous domains.
Reopen State Names On GoDaddy Grouping
The largest grouping are 98 domains registered on GoDaddy in bulk in clusters at roughly seconds apart using the Domains By Proxy service. These domains fit the Aaron Dorr pattern, but currently serve no content. Initially we thought that these must be staging domains for more of Mr. Dorr’s firearms coalition pages, but later found an article by the Florida Times-Union stating that Michael Murphy purchased these domains to keep others from buying them.
reopenak[.]com reopenal[.]com reopenala[.]com reopenalaska[.]com reopenar[.]com reopenariz[.]com reopenark[.]com reopenarkansas[.]com reopenaz[.]com reopencal[.]com reopencalif[.]com reopencanow[.]com reopenco[.]com reopencolo[.]com reopencolorado[.]com reopenconn[.]com reopenconnecticut[.]com reopendc[.]com reopendel[.]com reopendelaware[.]com reopenfla[.]com reopenga[.]com reopengeorgia[.]com reopenhawaii[.]com reopenhi[.]com reopenia[.]com reopenidaho[.]com reopenil[.]com reopenill[.]com reopenillinois[.]com reopenin[.]com reopenindiana[.]com reopeninghuntsville[.]com reopeningofamerica[.]com reopenkans[.]com reopenky[.]com reopenla[.]com reopenlouisiana[.]com reopenma[.]com reopenmaine[.]com reopenmass[.]com reopenmassachusetts[.]com reopenmd[.]com reopenmontana[.]com reopenms[.]com reopenmt[.]com reopenncnow[.]com reopennd[.]com reopennebraska[.]com reopennewmexico[.]com reopennm[.]com reopennorthcarolina[.]com reopennorthdakota[.]com reopenor[.]com reopenoregon[.]com reopenpennsylvania[.]com reopenrhodeisland[.]com reopensouthcarolina[.]com reopensouthdakota[.]com reopentennessee[.]com reopentn[.]com reopentxnow[.]com reopenunitedstates[.]com reopenut[.]com reopenutah[.]com reopenva[.]com reopenvirginia[.]com reopenvt[.]com reopenwashington[.]com reopenwestvirginia[.]com reopenwisconsin[.]com reopende[.]com reopenks[.]com reopenme[.]com reopenmich[.]com reopenmo[.]com reopenmont[.]com reopenndak[.]com reopenne[.]com reopenneb[.]com reopennev[.]com reopennewhampshire[.]com reopennmex[.]com reopenoh[.]com reopenokla[.]com reopenore[.]com reopenoreg[.]com reopenri[.]com reopensdk[.]com reopentenn[.]com reopentex[.]com reopenvermont[.]com reopenwash[.]com reopenwis[.]com reopenwisc[.]com reopenwv[.]com reopenwva[.]com reopenwy[.]com reopenwyo[.]com
Reopen Everything Grouping
This grouping had the characteristic of being registered via Domainchop[.]com and containing names of specific things to reopen such as sporting venues or schools. They all point to pages on AWS and have their nameservers pointed at AfterNIC. These are all set up as domains for sale and are likely a domainer hoping to capitalize on the reopen trend. The 11 domains include:
reopeningbars[.]com reopeningbaseball[.]com reopeningbasketball[.]com reopeningcasinos[.]com reopeningdaycares[.]com reopeningfootball[.]com reopeningrestaurants[.]com reopeningschools[.]com reopeningsports[.]com reopeningstadiums[.]com reopeningtheaters[.]com
Miscellaneous
This final grouping are the remainder domains that include:
reopen-usa[.]com reopenamerika[.]com reopenx[.]com
They have no relation from what we can find. The first appears to be another petition page while the other two are dark.
Conclusion
We hope that through following along here you can find new techniques for verifying and expanding on the information and disinformation that you find floating around on social media. With DomainTools Iris Investigate Platform you can quickly pivot out to discover the history and ties between pages that make investigations like this possible and even further monitoring for changes in your discoveries.
As “reopen” domain registrations continue to grow in popularity and protests crop up around the United States we are continuing to monitor changes in this space. As of April 23rd we have now seen over 500 new domains registered since the initial reopen domains from the Dorr brothers. Facebook groups spun up by the Dorr brothers use these groups to direct traffic to these domains. We are now seeing other groups piggyback off of this popularity resulting in the number of registered domains growing daily. We expect this trend to continue through the current wave of protests with new terms such as “liberate” and others cropping up in social media.