The DomainTools Report: 2015 Special Edition

You may recall that earlier this year DomainTools published a report examining concentrations of malicious activity along a multitude of dimensions to identify “hotspots” across the internet. We decided to expand our search for this DomainTools Report supplement- this time seeking concentrations of malicious activity within Bulk Domain Registration Agents (BDRAs) or Bulk Domain Resellers in the creation of malicious domains. We examined patterns and behaviors of BDRAs, and we took a close look at a breach involving one. This information will also be presented in our webinar with Dark Reading on December 10th at 10 AM PST/ 1 PM EST.
Patterns and Behaviors of Bulk Domain Registration Agents
Bulk Domain Registration Agents exhibit a pattern of behavior:
- They register a large volume of domains (this report defines the threshold as 1,000 domains)
- They register the domains with one set of identifying data, then after a short time change the registration details, en masse, to different values
- They repeat this cycle
Example of Bulk Domain Registration Agents
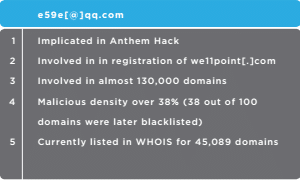
This supplement came to fruition when news of the Anthem Healthcare breach broke in early 2015. A key email domain in the attack, we11point[.]com spoofed legitimate infrastructure in order to capture employee credentials (Wellpoint as Anthem’s previous name). This domain was found to be registered by a BDRA, identified by its email address on the domain’s initial Whois record. We decided to investigate this and other similar agents to determine whether there was an identifiable pattern linked to large-scale malicious activity, or if this was an isolated event. Our team discovered that an email address (e59e[@]qq.com), which was implicated in the Anthem hack.
DomainTools Findings
The data featured in this report is a result of queries that mined the DomainTools database to identify BDRAs, yielding 122 legitimate results. We then compared these BDRAs against industry blocklist sources.
Our hypothesis was that some BDRAs might show patterns of recurring malicious activity. Looking across the pool as a whole we found:
- A malicious density as high as 72% (approximately 7 out of 10 domains registered by the BDRA were later added to industry blocklists)
- A surprisingly low density of malicious activity (suggesting that some BDRAs really aren’t closely connected to serious harm)
- 56 of 122 have malicious density exceeding 10%
- Aggregate malicious density across all BDRAs is 13.6%
For some perspective, the average malicious density across all currently extant domains is around 2-5% (depending on which industry blocklists are referenced).
Read More
If you are interested in diving deeper in our research, the full report also includes a deep look into BDRAs by count, density of malicious domains and by volume and density. For more information and further analysis- Download the DomainTools Report: 2015 Special Edition.

