You’re Gonna Need a Bigger Pane of Glass


Introducing the New Iris Investigate API
One of the most common refrains we hear from our customers is their pursuit of what they call “a single pane of glass.”
They envision a SOC where everyone operates in the same user interface, backed by a system that collects all the data they need to act, streamlines their workflow, and preserves the results of their analysis for future correlation and ongoing process improvement.
It’s a noble goal, and one that DomainTools fully supports, with an extensive set of enterprise-grade APIs for nearly all our datasets. Our customers have leveraged these APIs at scale to add context to network logs, enrich SIEM alerts, automate workflows, and visually merge our data with theirs, all with outstanding results.
Many of our technology partners have strengthened their case to be that single pane by adding insightful capabilities to their products powered by DomainTools APIs and enabled by our domain profile and historical data. And of course, we’ve built a large and ever-growing set of apps and plugins, like our Splunk & QRadar apps, our contributions to MISP, transforms for Maltego, and playbooks in Phantom, just to name a few.
Of course, effective threat analysis and alert triage isn’t always about data; often, you need specialized tools to help navigate that data, structure the analysis, and act on the results. It requires considerable effort (and cost) to build those capabilities into the system you’ve selected as your single pane of glass. Leaders must then make the difficult decision of whether to send team members into a specialized product to continue their work, or to do without those capabilities.
And let’s be honest: DomainTools Iris Investigate doesn’t make this decision easy, because Iris Investigate enables a capability for your team that goes way beyond a static display of domain profile and DNS data.
We call it “mapping connected infrastructure” – our customers call it “finding bad guy domains on our network we didn’t know existed” or “blocking every domain this attacker has ever registered.” However you label it, pivoting through the networks, name servers, SSL certificates, and tracking codes that link one domain to dozens or hundreds more gives powerful outcomes.
That, combined with visualization, historical data, and adjacent passive DNS data, plus some incredible stuff we’ve got on the roadmap for 2018, and you have a lot of very good reasons to use Iris Investigate.
Until recently, all that data and pivoting functionality was available only in the Iris Investigate user interface, but that changes today.
Introducing the Iris Investigate API, easily the most comprehensive, most capable API endpoint we’ve ever built.
Here’s why we’re so excited about it:
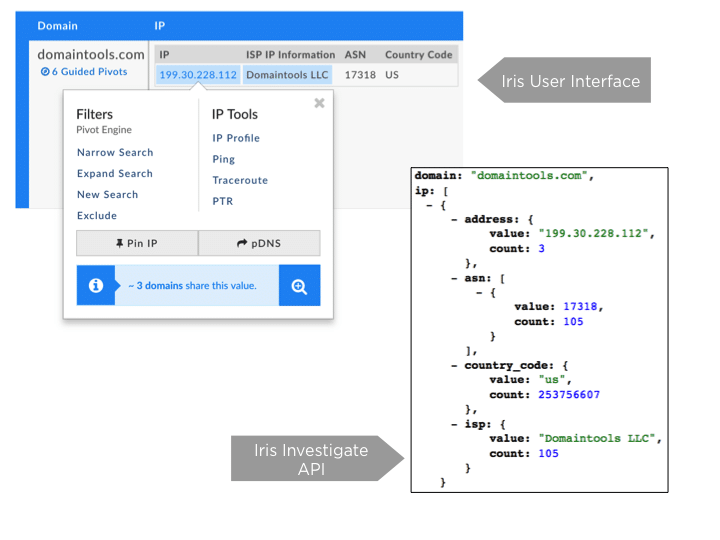
- Here’s a great example: often, knowing a mail host or web server is shared with just a few other domains is itself a useful insight, but it’s easy to miss. Not with Iris Investigate, and now, not with anything you build on top of the Iris Investigate API.Once you find those pivot points, the same Iris Investigate API will put on its superhero cape and find domains that share any of a dozen different fields. Whois attributes? Uh, yeah, we are DomainTools, after all. SSL certificate email address or common name? Done. Shared web host, name server, mail server, Google Adsense code, redirect target?! Zip, bam, pow on all fronts! Basically, if you can pivot on something in the Iris Investigate user interfaces Pivot Engine, you can do the same in the Iris Investigate API – and soon, also in that mess of code you’ve been hiding from your SOC manager.And when you consider you can limit API queries to only recently created domains, and then run that query each day, you now have an ever-vigilant superhero who can find any of that stuff in the future. Point that Python at your proxy’s block list and you won’t have snakes on your plane, or your network. Kapow!
- But wait, there’s more – you can drop an Iris Investigate search hash directly on the Iris Investigate API, with no other search parameters needed, and you’ll end up with the same result set an analyst saw after they arrived at the criteria that best enumerated a set of domains. That last one is something I’m especially happy about, because it enables a scenario where the Iris Investigate user interface co-exists with solutions built on the Iris Investigate API. Consider this: Your front-line defenders (what many teams label “tier 1”) see an alert that is already enriched with heaps of data from the Iris Investigate API. They escalate it into a ticketing system where an automated workflow looks at the Guided Pivot counts and runs Iris Investigate queries on the most promising fields. Your next-level analysts and IR teams quickly take action to block or remediate, informed by data from DomainTools Iris Investigate and elsewhere.
Finally, the threat intel, malware and hunt teams go deep, leveraging the Iris Investigate UI to help them find intersection points between published intel and newly-discovered actor infrastructure. They export the Iris Investigate search hash and paste it into a tool you’ve built to block the Iris Investigate results today, and monitor for new domains in the future. That story isn’t just a vision: it can be a reality for teams that leverage Iris Investigate and are willing to think creatively about places where using the Iris Investigate user interface makes sense, and where the data and pivot searches can be sufficient on their own. In fact, it was so important for us to enable that hybrid usage pattern that we merged query allocations in the Iris Investigate user interface and the Iris Investigate API. That means it doesn’t matter which mechanism you choose to use Iris Investigate – you have the same shared pool of queries to pull from.
We’re also offering this incredible API with every new offering of Iris Investigate, at no additional charge, so there’s really no reason not to get cracking and built something incredible with it. Existing Iris customers who are interested in the Iris Investigate API are encouraged to reach out to their DomainTools Account Manager to find out how to start using it.
But you’d better hurry: we’re also hard at work adding support for the Iris Investigate API into all our integrations, so we may arrive inside your favorite security product before your code does. Stay tuned for more details, and if we get there first, be sure to try out what we’ve built and give us feedback on how we can make it even better.
Thanks for reading this! Reach out anytime if you’d like a free trial – we’d love to show you what Iris Investigate is capable of. For more information on the Iris Enrich and Investigate APIs, join Director of Product Management, Tim Helming, and myself on August 21st at 10 AM PT/ 1 PM ET to learn how teams can leverage the Iris API together with the Iris Investigative Platform to create incredibly effective analyst workflows.

