Coming up this week on Breaking Badness. Today we discuss: REvil Upheaval, This Apple Tastes Malicious, and our fun new game, two truths and a lie.
Here are a few highlights from each article we discussed:
REvil Upheaval
- I’ll try to put this succinctly, but that’s tricky with geopolitics, isn’t it? Of course I suspect that if anyone is just hearing about the tensions at Ukraine’s eastern border from this podcast, they really need to reevaluate their choices of news sources. Having said that, there have been some interesting developments over the weekend—the one that stood out to me was that Britain made an unusual move, by revealing intelligence that would normally not be made public. The intelligence in question was that Moscow allegedly has a plan to install a pro-Moscow leader in Kyiv. Naturally, the Russians deny this, but it seems oh so plausible. Then just today we saw a story about the trains in Belarus exhibiting some decidedly un-Swiss behavior, and getting delayed and stopped due to an apparent hack of signaling systems. Why do trains in Belarus matter here? Well, seems they’re carrying Russian troops and armor in the direction of – you guessed it – Ukraine. Now of course there’s the question of whether all of this is mainly posturing, or whether there’s really an invasion and takeover afoot here. I assume, probably wrongly but who knows, that Putin knows Biden’s popularity is not high, and that the Democratic party is in peril in 2022. If he can create a political nightmare for the Biden administration and its supporters by putting them in a no-win situation with respect to Ukraine, then that’s likely to hurt them in the midterm elections, and we saw in the last administration a curiously deferential posture toward Russia. The thinking is probably that if the Republicans return to power, then things like sanctions and other tough-stance policies are going to relax. So it’s just a rollicking good mess.
- The basic story is that the FSB arrested key members of the REvil ransomware gang a couple of weeks ago. And in fact I’m putting it more mildly than the stories go – they basically say that REvil was “taken down,” and for those of you not reading this podcast, I put that in quotes. Skeptical much? Yes, amaze, wow, much skeptic. But anyway, on at least a superficial level this looks like a rare instance of US-Russian cooperation. I’ve read some speculation that it is perhaps designed to lessen the impact of the whole Ukraine thing by balancing it with doing us a solid. I don’t buy that.
- You may recall a certain pipeline that was shut down last May. Colonial? Ring a bell? That was REvil. They infected the business side of Colonial’s ops, and while there wasn’t any evidence that the OT (operational technology) side of Colonial was infected, they shut it down out of an abundance of caution, which was a big pain in the butt but generally seen as the right thing to do. Anyway, while I doubt the FSB shed a lot of tears over the problems that caused, it did make this apparent takedown a bigger deal than it might have been if they’d just been doing the usual nice things—you know, taking out hospitals and towns and corporations. But really I think that your question gets at the mystery of this thing and the fundamental answer is that I don’t know what their ACTUAL motivations are, regardless of the public statements and whatnot. Everyone knows that a lot of ransomware gangs are, if not directly overseen by the SVR (sort of Russia’s CIA), then at least there’s a wink and nod relationship. So making this arrest is like busting one of your friends at the behest of your enemy. But hey, who knows, maybe someone high-up in REvil was getting attitude-y toward their handlers?
- According to Reuters “A police and FSB operation searched 25 addresses, detaining 14 people, the FSB said, listing assets it had seized including 426 million roubles, $600,000, 500,000 euros, computer equipment and 20 luxury cars.” They named two of the people arrested, so if any of you know Roman Muromsky and Andrei Bessonov, you’re going to have a harder time sending them care packages these days. At least for a while. But I couldn’t find a lot of evidence in the reporting I’ve read to indicate that Muromsky and Bessonov were specifically leaders or extremely key members of the gang. Muromsky sounds, according to a source who was interviewed by Reuters, like a guy who lives a fairly modest life. I don’t know, maybe he just leaves the Lambos parked in Monte Carlo and maintains a cover as a regular guy in Moscow? And then you have the statement by the FSB that “the criminal organization has ceased to exist.” If there’s one thing we know about these ransomware gangs, it’s that they’re like hydras. Cut off one head, another takes its place pretty quickly. Of course, this might force a rebranding, so that REvil swag you bought might become more valuable in 10 years.
- Infosec professionals seem to have the same kind of skepticism that I described earlier. If there’s one group that really does believe that if something sounds too good to be true, it probably ain’t, it’s infosec. So what we’re expecting really is that pretty soon we’ll see more activity either from REvil itself or from some rebranded thing, or that the detainees were released, or that we just never hear anything again from the FSB but the ransomware goes on, etc. From a defender’s point of view, really not much has changed. I think we’ll have to keep an eye on what happens here, but mainly from the perspective of curiosity, geopolitical interest, and schadenfreude (which could be misplaced) and not as an operational difference-maker. I think basically you’ll just want to be keeping up with @jfslowik’s memes if you want to get the crib notes on this thing.
This Apple Tastes Malicious
- The FingerPrintJS team discovered some interesting behavior in how Safari handles IndexedDB database names. IndexedDB is a low-level API for client-side storage of significant amounts of structured data, including files/blobs. It was introduced to Safari in Yosemite 10.10, back in 2014 and is also supported in Firefox, Chrome and Edge. It gives web apps the ability to store user data and is domain siloed, meaning that foo dot com has no idea what bar dot xyz is up to, IndexedDB wise. This is referred to as a ‘same-origin policy’.
- In Safari 15 on macOS, and in all browsers on iOS and iPadOS 15, the IndexedDB API is violating the same-origin policy. Every time a website interacts with a database, a new (empty) database with the same name is created in all other active frames, tabs, and windows within the same browser session.
- This vulnerability could be exploited when a malicious domain, when visited, can view the folders of any created IndexedDB on other tabs.
- So right away you can start to profile and de-anonymize a victim. Worse, with Google services you are able to discern the unique UserID for a visitor. With that UserID you can pull their avatar picture from Google using their APIs, giving you even more to work with in identifying a website visitor.
- FingerpintJS tested all of the Alexa 1000 and identified more than 30 websites that interact with indexed databases directly on their homepage without any additional user interaction.
- The JSFingerprint team registered safarileaks.com and have a POC demo running there. If you visit with Safari you can see the list of websites they can detect as of now.
- It isn’t possible to protect yourself or your organization from Apple leakage. Well if you are using MacOS you do have the option of using Chrome or Edge or Firefox. If you are on iOS or iPadOS your browser choices are merely an illusion, with Safari’s webkit implementation running the show regardless of what browser app you choose.
- This vulnerability was reported to Apple back on November 28th, 2021. The FingerprintJS team, frustrated by the slow response, made it public January 14th. Apple released an impending fix to their developer channels late last week, so this will be patched for users in the near future.
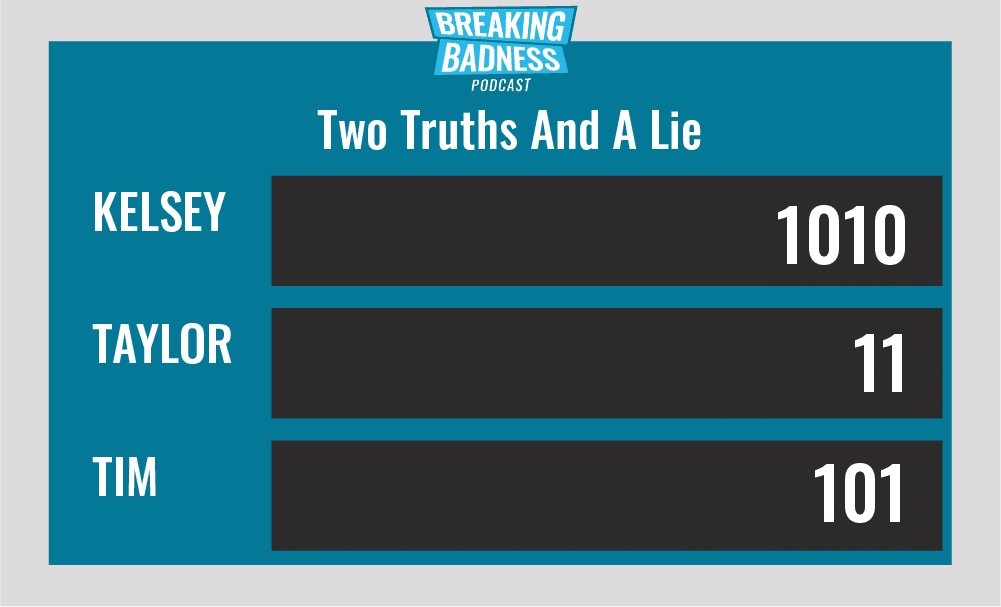
Two Truths and a Lie
Introducing our newest segment on Breaking Badness. We are going to play a game you are all likely familiar with called two truths and a lie, with a fun twist. Each week, one us with come prepared with three article titles, two of which are real, and one is, you guessed it, A LIE.
You’ll have to tune in to find out!
Current Scoreboard
This Week’s Hoodie/Goodie Scale
REvil Upheaval
[Taylor]: 4.5/10 Hoodies
[Tim]: 2/10 Goodies
This Apple Tastes Malicious
[Taylor]: 5/10 Hoodies
[Tim]: 4/10 Hoodies
That’s about all we have for this week, you can find us on Twitter @domaintools, all of the articles mentioned in our podcast will always be included on our podcast recap. Catch us Wednesdays at 9 AM Pacific time when we publish our next podcast and blog.
*A special thanks to John Roderick for our incredible podcast music!




