Coming up this week on Breaking Badness. Today we discuss: Poisoning the DNS Well, Keep It On The DLL, and our fun new game, two truths and a lie.
Here are a few highlights from each article we discussed:
Poisoning the DNS Well
- A flaw in all versions of the popular C standard libraries uClibc and uClibc-ng can allow for DNS poisoning attacks against target devices
- DNS poisoning, for those who may be unaware, occurs when your adversary tricks your DNS client to accept improper responses and sends folks to a malicious server instead of the proper one you’re looking for
- The flaw was discovered by Nozomi Networks Labs (tracked under CVE-2022-30295) when they discovered a predictable pattern of transaction IDs (which included DNS requests)
- It’s a problem because if something is predictable, then it can be spoofed
- We’re unsure of the exact number of affected devices at this time, but an estimate would be that it’s in the millions. There are certainly devices out there that no longer use these standard libraries, but there are still many that do, and this vulnerability could be baked into those devices
- DNS is so ripe for attackers for a few reasons:
- One is because it’s open and encrypted for the most part
- The other part is because it’s incredibly powerful and it gets around other security controls
- DNS is used in many different scenarios, so if you’re able to control DNS, you can control what people interact with in the outside world
- In terms of mitigations, there are none so far and it’s been detailed that for safety purposes, it will not be revealed which IoT devices were tested
Keep It On The DLL
- Hackers commonly exploit vulnerabilities in corporate networks to gain access, but a researcher has turned the table by finding exploits in the most common ransomware and malware being distributed today
- A security researcher named hyp3rlinx found that samples of code common to operations such as Conti, REvil, LockBit, and AvosLocker, as well as a more recent up-and-comer called Black Basta, were vulnerable to DLL hijacking
- For those who may not be aware, DLL stands for ‘dynamic link library’
- DLLs are some of the fundamental building blocks of modern Microsoft code (among others)
- It has benefits both in terms of efficiency and flexibility
- DLLs provide the standard benefits of shared libraries (DLL being a specific flavor of shared libraries), such as modularity
- Modularity allows changes to be made to code and data in a single self-contained DLL shared by several applications without any change to the applications themselves
- DLL hijacking exploits the way applications search for and load in memory the DLL files they need
- If the software has insufficient checks to ensure that this can’t happen, it can load a DLL from a path outside its directory, elevating privileges or executing unwanted code
- You can imagine the havoc that could wreak in Windows; well, it wreaks havoc with these vulnerable ransomwares as well
- This researcher implemented DLL hijacking by replacing a required DLL file with an infected version and placing it within the search parameters of an application, so the infected file will be called upon when the application loads, activating its operations
- What we saw from this researcher was a demo video (on YouTube) where they replace a file called netapp32.dll with their own version of it
- Then they run Conti. What you see is that Conti runs, but doesn’t execute correctly, and some TXT files that it’s supposed to encrypt don’t get encrypted
- Then just for the sake of completeness, the researcher deletes the manipulated netapp32 DLL, and reruns Conti. This time, the encryption happens the way it’s designed to
- This solution is not a silver bullet to stop these organizations. It’s a matter of time before these ransomwares are patched. In the near term, this could be helpful to teams as a preventative measure
- This is process of finding vulnerabilities in malcode and exploiting them seems to be hyp3rlinx’s stock in trade
- They have a site called malvuln.com where they document these findings, and there are a bunch of them there
- Now, there’s of course a downside here too, which is that much like how malcode authors “QA” their latest versions against detection by submitting them to VirusTotal, this is another benevolent service that will undoubtedly be exploited by threat actors by patching the vulns that hyp3rlinx has documented
- It may be speculation, but this researcher’s work may help pave the way for discovery of vulnerabilities that may be harder for the malcode authors to patch
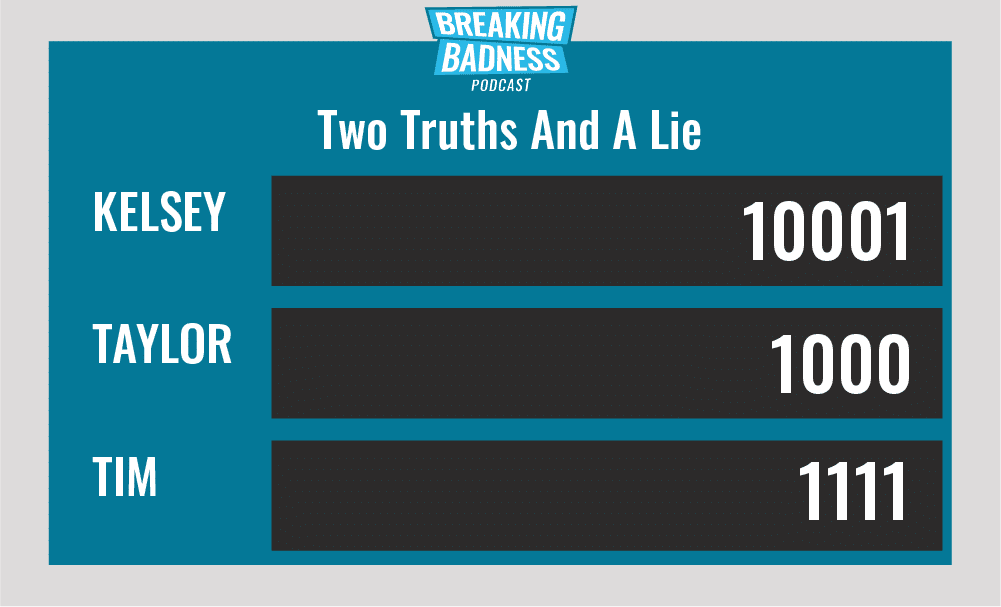
Two Truths and a Lie
Introducing our newest segment on Breaking Badness. We are going to play a game you are all likely familiar with called two truths and a lie, with a fun twist. Each week, one us with come prepared with three article titles, two of which are real, and one is, you guessed it, A LIE.
You’ll have to tune in to find out!
Current Scoreboard
This Week’s Hoodie/Goodie Scale
Poisoning the DNS Well
[Taylor]: 4/10 Hoodies
[Tim]: 4.5/10 Hoodies
Keep It On The DLL
[Taylor]: 2/10 Goodies
[Tim]: 3/10 Goodies
That’s about all we have for this week, you can find us on Twitter @domaintools, all of the articles mentioned in our podcast will always be included on our podcast recap. Catch us Wednesdays at 9 AM Pacific time when we publish our next podcast and blog.
*A special thanks to John Roderick for our incredible podcast music!




