Coming up this week on Breaking Badness. Today we discuss: Hertz Don’t It?, Decoy Oy Yoy Yoy, and our fun new game, two truths and a lie.
Here are a few highlights from each article we discussed:
Hertz Don’t It?
- Hertzbleed is a new family of side-channel attacks: frequency side channels
- These attacks enable attackers to extract cryptographic keys from remote servers that were previously believed to be secure
- In this research paper, it’s demonstrated how an attacker can use a chosen-ciphertext attack against Supersingular Isogeny Key Encapsulation (SIKE) to perform key extraction via remote timing
- It’s not defined as a bug, but as a feature of modern processors
- What are side-channel attacks?
- These are attacks performed without actually hacking the system
- When you run an operation, you create a specific, physical signature
- This function ramps up the power your Central Processing Unit (CPU) is using
- These signatures are critical to side channel attackers as they attempt to understand what information was processed
- This is not the first attack of its kind
- For over 2 decades, side channel attacks have been used, though Hertzbleed has additional capabilities not yet seen before
- This includes remote deployment (which makes it easier to deploy than previous side-channel attacks)
- Hertzbleed also runs on “constant time” mechanisms which is code designed to eliminate the length of time a process takes to complete
- For over 2 decades, side channel attacks have been used, though Hertzbleed has additional capabilities not yet seen before
- Who does this affect?
- Cryptographic engineers more so than ordinary users
- All Intel processors are susceptible to Hertzbleed along with many AMD chips
- Even if you don’t use affected processors, thousands of servers do
- It’s also a slower attack, said to take “hours to days” to steal small amounts of data
- Currently, there’s no known attack that’s using Hertzbleed, though researchers say practical usage of this attack would have significant security implications
Decoy Oy Yoy Yoy
- Two Chinese hacking groups conducting cyber espionage and stealing intellectual property from Japanese and western companies are deploying ransomware as a decoy to cover up their malicious activities
- Ransomware is likely used because it’s exciting and newsworthy and defenders (rightly so) tend to “freak out” when there are signs or proof of inflection
- It’s not quite clear how fast this tactic is spreading or evolving, but we saw similar antics in the 2018 Banco de Chile Wiper Attack
- This most current attack was discovered by Secureworks studying two groups: Bronze Riverside” (APT41) and “Bronze Starlight” (APT10)
- These groups were both using the HUI Loader to deploy Remote Access Trojans (RATs), PlugX, Cobalt Strike, and QuasarRAT
- The HUI Loader is a custom DLL loader whose name is derived from a string in the loader
- The malware is loaded by legitimate programs that are vulnerable to DLL search order hijacking
- This HUI Loader decrypts and loads a third file containing an encrypted payload that is also deployed to the compromised host
- In March 2022, “Bronze Starlight” leveraged Cobalt Strike to deploy ransomware strains such as LockFile, AtomSilo, Rook, Night Sky, and Pandora
- In these attacks, a new version of HUI Loader was used (which is capable of hooking Windows API calls and disable Event Tracing for Windows (ETW) and Antimalware Scan Interface(AMSI) functions
- Infrastructure is once again the Achilles heel! The configuration of Cobalt Strike beacons in three distinct attacks using AtomSilo, Night Sky, and Pandora revealed a shared C2 address
- Additionally, the same source was used for uploading HUI Loader samples on Virus Total this year
- Part of the tipoff was activity that didn’t pass the sniff test: the activity and victimology of LockFile, AtomSilo, Rook, Night Sky, and Pandora are unusual compared to financially motivated ransomware operations, targeting a small number of victims over a brief period and then abandoning the project altogether (so this was a clue, behaviorally speaking)
- These groups were both using the HUI Loader to deploy Remote Access Trojans (RATs), PlugX, Cobalt Strike, and QuasarRAT
- The targets for these attacks are Western and Japanese companies as the principal targets
- The mitigation for these attacks is where some advanced IR tabletop as well as threat model exercises can pay off: defenders have to be aware that a given attack may not be the only thing going on at that time
- Teams may be overloaded and unable to ask the question, “is there more than one thing happening here?” but unfortunately we do have to keep vigilant for this kind of double-whammy
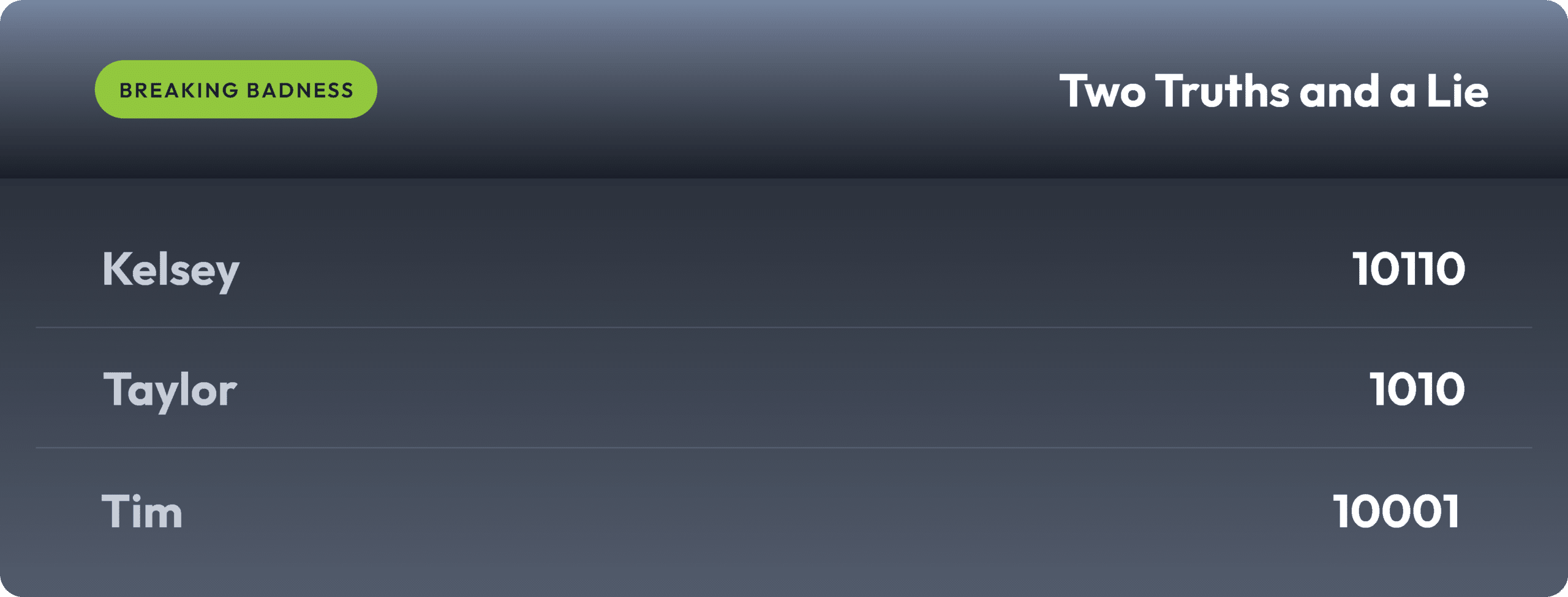
Two Truths and a Lie
Introducing our newest segment on Breaking Badness. We are going to play a game you are all likely familiar with called two truths and a lie, with a fun twist. Each week, one us with come prepared with three article titles, two of which are real, and one is, you guessed it, A LIE.
You’ll have to tune in to find out!
Current Scoreboard
This Week’s Hoodie/Goodie Scale
Hertz Don’t It?
[Taylor]: 4.75/10 Hoodies
[Daniel]: 8/10 Hoodies
Decoy Oy Yoy Yoy
[Taylor]: 6.5/10 Hoodies
[Daniel]: 8/10 Hoodies
That’s about all we have for this week, you can find us on Twitter @domaintools, all of the articles mentioned in our podcast will always be included on our podcast recap. Catch us Wednesdays at 9 AM Pacific time when we publish our next podcast and blog.
*A special thanks to John Roderick for our incredible podcast music!




