Coming up this week on Breaking Badness. Today we discuss: Tesla Catches a Brake in Ransomware Attack
, Mazed and Confused: SunCrypt joins the Maze ransomware cartel, and our fun new game, two truths and a lie.
Here are a few highlights from each article we discussed:
Tesla Catches a Brake in Ransomware Attack
- Basically a Russian hacker group tried to bribe a Tesla employee, through one of his old friends, to install malware on the corporate network that would then be used to run some ransomware and extort money from Tesla. The employee ended up alerting his employer instead who called the FBI and they further surveilled the two, gathered more information on other attacks, and eventually arrested the briber in Los Angeles while they were trying to flee the country. A lot of interesting dialog came out of it in surveillance though that really shows just how brazen these ransomware gangs have gotten.
- In terms of communication, the Tesla employee and defendants had initially met at a bar in Reno, but after that communicated on WhatsApp. They were basically going to pay the employee $500,000 to install the ransomware, then they also offered to DDoS Tesla’s servers during the initial install to provide a distraction and that they would craft the malware to look like it was from an employee that the employee had beef with—if they wanted.
- It the employee would have complied, the fallout would have likely been millions in cash they would have to pay out. The ethos around Tesla—and all of Musk’s companies—is that they move fast and teams have low friction. Coming from the operations world I know that usually equates in the IT world to not a lot of network segmentation and quite a bit of shadow IT as teams just spin up whatever they need. Of course this is me just extrapolating here, but that’s never a good design when you’ve got ransomware involved.
- The defendant in this case spoke about having done this at several other companies in the past and there are mentions of different discussions they have over WhatsApp with their co-conspirators. All very brazen really.
- Insider threats are a huge problem, right? In fact probably the largest threat vector. Stuxnet was introduced by a rogue employee for instance. I don’t have the numbers, but I would guess this is pretty common especially with all of the recent big name payouts to ransomware groups. As long as the money keeps rolling in the gangs will keep doing their work.
- I’m a big fan of canary documents and tokens littered about, but even that just stops a certain kind. For something like this I think you need to let your employees know that the reward for reporting this is generous enough that they wouldn’t want to risk it. I really hope Musk pays out that employee otherwise the next offer they may not be so keen to comply.
Mazed and Confused: SunCrypt joins the Maze ransomware cartel
- The threat group behind the Maze ransomware was one of the first groups to come up with the double-extortion method against victims. To have some leverage over these organizations, the ransomware attackers steal data from the infiltrated system while they deploy their ransomware. They then threaten to publish the data if the victim decides not to pay. Depending on the kind of data, this can be a rather compelling reason to give in.
- This is now slowly becoming one of the most popular ransomware attack templates out there. We’ve seen other notorious ransomware such as REVil, Clop and DoppelPaymer use this method too.
- The Maze ransomware group, simply put, could not keep up the volume of operations they’re dealing with. Managing ransomware operations, especially when you’re successful, can be tremendous. With that being said, reporters at BleepingComputer had an inside contact with a representative of SunCrypt who divulged about the need for more help from the Maze group.
- It sounds like, more specifically, SunCrypt will help provide hacked networks to hand over to Maze for profit sharing opportunities.
- In the sample of SunCrypt, we’re seeing a PowerShell here for the initial loader for the SunCrypt ransomware, despite some improvements with malicious PowerShell detection by Microsoft.
- In terms of implications of the shared IP address, to be frank, this is another example of bulletproof hosting turning a blind eye. Maze has been using this single public IP address for a long time now.
- SunCrypt, so far, appears to be pretty straightforward from a ransomware perspective. PowerShell initial loader, uses a Tor site for the payment info and encrypts user data. They, much like Maze, follow double extortion as well. Nothing particularly new with SunCrypt.
- As of this writing, there are 5 known victims listed on SunCrypts public leak site.
- From a technical perspective, this is nothing new. From a threat group perspective, I’m much more concerned when you have two groups that join forces.
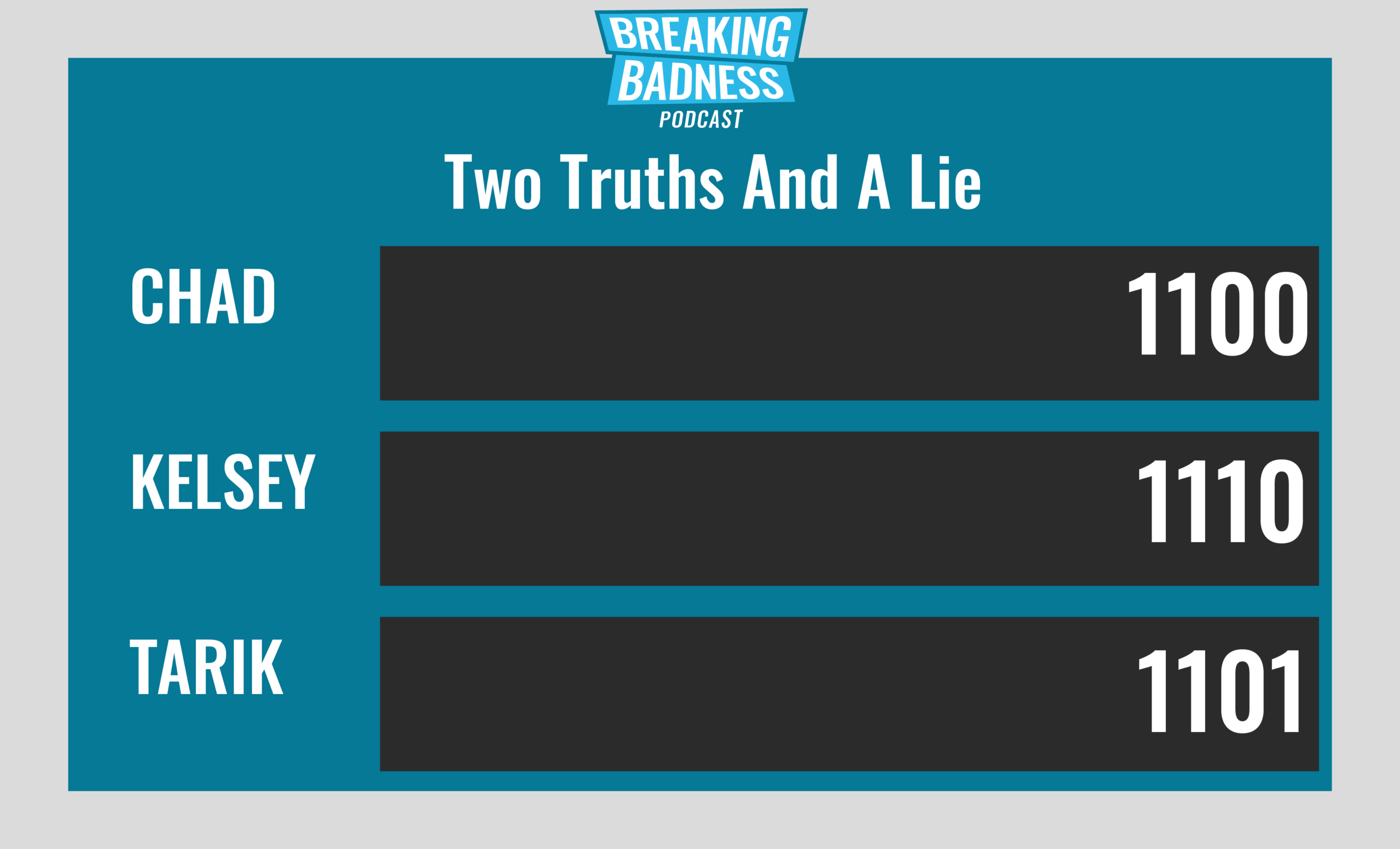
Two Truths and a Lie
Introducing our newest segment on Breaking Badness. We are going to play a game you are all likely familiar with called two truths and a lie, with a fun twist. Each week, one us with come prepared with three article titles, two of which are real, and one is, you guessed it, A LIE.
You’ll have to tune in to find out!
Current Scoreboard
This Week’s Hoodie/Goodie Scale
Tesla Catches a Brake in Ransomware Attack
[Chad]: 9/10 Hoodies
[Tarik]: 9/10 Hoodies
Mazed and Confused
[Chad]: 9/10 Hoodies
[Tarik]: 8/10 Hoodies
That’s about all we have for this week, you can find us on Twitter @domaintools, all of the articles mentioned in our podcast will always be included on our podcast recap. Catch us Wednesdays at 9 AM Pacific time when we publish our next podcast and blog.
*A special thanks to John Roderick for our incredible podcast music!




