Coming up this week on Breaking Badness. Today we discuss: No Domain No Gain, Let’s Talk Wild Turkey About Ransomware, and our fun new game, two truths and a lie.
Here are a few highlights from each article we discussed:
No Domain No Gain
- We imposed some sanctions on Iran, which cover a wide range of activities. The IRGC, which you’ll often hear referred to as the Revolutionary Guard, is a branch of Iran’s military, and one of the areas they are involved in is information warfare, or disinformation campaigns. As part of that, they put up any number of fake news outlets that posed as real ones. (As an aside, can I just mention that one of the major indicators of how screwed up this timeline is, is the fact that you now have to distinguish between real fake news and fake fake news?). At any rate, four of these domains were specifically targeting American audiences, and the remainder were for other regions. And by the way, these aren’t the only domains that have been seized in a similar way recently. The US snagged 92 others a little while back.
- I’ll admit that I hadn’t heard of the IEEPA (or at least don’t remember hearing of it) before reading this story. It goes back to Jimmy Carter. It authorizes the president to declare the existence of an “extraordinary and unusual threat” to the national security, foreign policy, or economy of the United States” that originates “in whole or substantial part outside the United States.” And what’s key here is that it authorizes the US government to seize assets tied to the cited threat. Hence we took these domains.
- This falls under the Justice Department, with involvement by the FBI, The Special Prosecutions Section and Asset Forfeiture Unit of the US Attorney’s Office for Northern California, and the Counterespionage Section of the DoJ’s National Security Division. Key to this seizure is the fact that the domains were registered with US based registrars, and in Top Level Domains (or TLDs) that are run by US-based registries. This is part of what allowed this to be prosecuted in the way it was. Key to the action was also cooperation by Google, Facebook, and Twitter.
- In terms of what we know about the 27 domains in this statement. That’s where the “real fake news” angle comes in. The four that were targeting the US, “rpfront,com,” “ahtribune,com,” “awdnews,com,” and “criticalstudies,org,” were promoting pro-Iranian messaging to American audiences, trying to influence changes in policy. A lot of the affidavit is redacted, so it’s not easy to tell what all of the other 23 domains were for, but it’s safe to say that they were all posing as news outlets, trying to influence various target audiences.
- The Foreign Agents Registration Act. This has been in the news a bit over the last few years, since various members of the outgoing administration had not registered themselves as acting on behalf of foreign governments as the Act requires. Basically it says that when you’re acting in the interests of a foreign power, you have to declare that. The registrants of these domains, using US registrars etc, didn’t do that. (Not surprisingly!)
- The US probably will keep on going after adversary online infrastructure. They’ve been getting more aggressive recently and I don’t think that will let up at all under the new administration. If anything I wouldn’t be surprised if the pace picks up further.
- This feels like a big win, not just specifically because of these particular domains—they’re a drop in the bucket. What makes it a win is that more aggressive stance. Disinformation is the new Cold War, so it’s pretty critical that we take firm action against it. I hope we see more and more of these actions.
Let’s Talk Wild Turkey About Ransomware
- Ryuk has of course been huge in the news with their near domination of ⅓ of all ransomware attacks right now—they’ve been hitting every industry with the most notable being hospitals of late. They are extremely effective and quick. On top of that we’ve got city and county governments being hit. It’s everywhere and with double-extortion from groups like Avaddon the payouts are getting more assured for these groups.
- So this was an infection of RagnarLocker according to the note—a group that had a big attack back in April when Ryuk was about to go dark for a bit. RagnarLocker is one of the double extortion groups and runs a public leak site. The attackers are demanding $15 million.
- Funny enough RagnarLocker posted on their public leak site the company’s contract with Matthew McConnaughey for a Wild Turkey spot. You could tell it was proof because McConnaughey’s signature on the bottom was just: all right, all right, all right. This attack, needless to say, has left us Dazed & Confused.
- Campari released a statement that they would not be paying the ransom and instead, five days later, were still working on bringing their systems back online. I applaud them for this as company’s should always take the steps to not encourage further ransomware attacks by paying the ransom and use this as an opportunity to rebuild their network right as we saw with Maersk and others after the NetPetya attacks—a much larger company, a much more damaging incident.
- I suspect that the RagnarLocker group will drop their files out in the open if they don’t pay. I really hope the EU has some provisions for circumventing GDPR fines for these companies though since you will be breached and these actors will dump your data. If the fines roll in we have a situation where the EU is then forcing funding of ransomware groups.
- I absolutely expect the number of attacks will increase. Especially as we roll into winter and with more lockdowns coming. Cybercrime in general is about to be on the rise again.
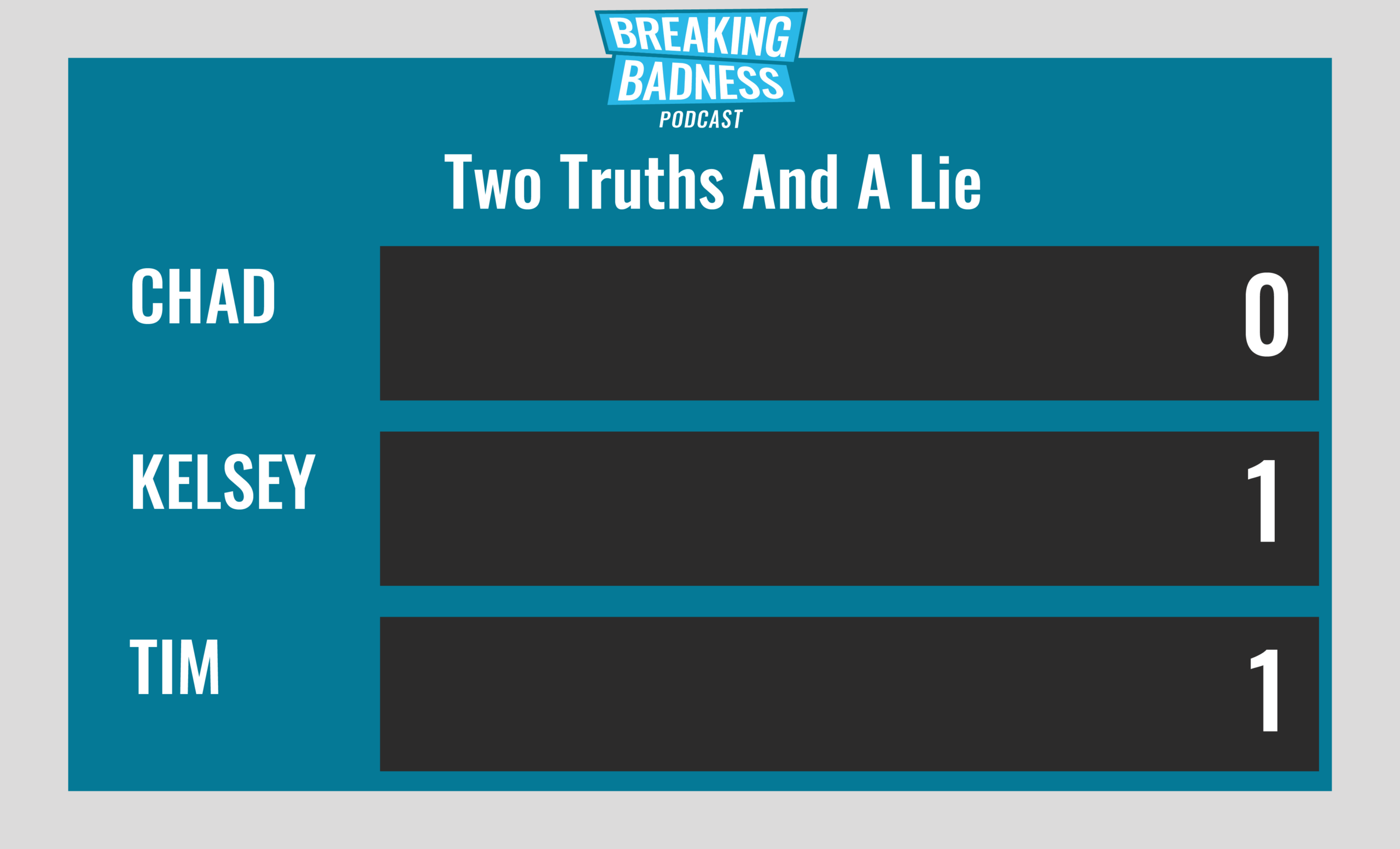
Two Truths and a Lie
Introducing our newest segment on Breaking Badness. We are going to play a game you are all likely familiar with called two truths and a lie, with a fun twist. Each week, one us with come prepared with three article titles, two of which are real, and one is, you guessed it, A LIE.
You’ll have to tune in to find out!
Current Scoreboard
This Week’s Hoodie/Goodie Scale
No Domain No Gain
[Chad]: 6/10 Goodies
[Tim]: 5/10 Goodies
Let’s Talk Wild Turkey About Ransomware
[Chad]: 8.33/10 Hoodies
[Tim]: 8/10 Hoodies
That’s about all we have for this week, you can find us on Twitter @domaintools, all of the articles mentioned in our podcast will always be included on our podcast recap. Catch us Wednesdays at 9 AM Pacific time when we publish our next podcast and blog.
*A special thanks to John Roderick for our incredible podcast music!




