Coming up this week on Breaking Badness. Today we discuss: FBI Walks On Web Shells, US Limits Bear Necessities, and our fun new game, two truths and a lie.
Here are a few highlights from each article we discussed:
FBI Walks On Web Shells
- Basically there was a big Microsoft Exchange vulnerability that was being actively exploited by groups that were dropping the ChinaChopper webshell which allows attackers remote access. Microsoft Exchange, remember is Microsoft’s big email server so this is a huge issue. It has to be connected to the Internet to function and had an RCE that allowed attackers with some clever work to take over the machine. The shell they dropped was for access later so they were mass exploiting exchange servers all around the web. On top of that other attackers began using the exploited machines that were left so it was turning into a real problem as you can imagine.
- The Justice Department got authorization to go in and remove the webshells on machines where the owners had been unable to remove the webshells that were left. This was an awesome bit of coordination. We’ve seen things like this in the past from rogue hackers who went and patched IoT routers and what not illegally, but this is one of only a few instances where it’s been official government business to do the removal.
- Lots of adversaries were exploiting this and attackers attacking other attackers. It was starting to turn into a mess.
- The DoJ press release was a notice that with the FBI’s help they were cleaning the Microsoft Exchange servers of these webshells. They also had a nice little jab at people who had not yet patched and left up the hundreds of webshells for attackers to use.
- To do so, they copied and removed the webshells. Pretty simple stuff all around. They did not patch the servers so they’re sitting out there ready to be exploited again unfortunately.
- I think it was a good move, but I wish they would have rogue patched the systems as well. Otherwise now this was just an announcement for attackers to go ahead and run their tooling again to takeover these machines. The copying of the webshells and their configuration should provide a lot of evidence for them to do some attribution though.
US Limits Bear Necessities
- The EO begins by citing Russian “efforts to undermine the conduct of free and fair democratic elections and democratic institutions in the United States and its allies and partners; engage in and facilitate malicious cyber activities against the United States and its allies and partners; foster and use transnational corruption to influence foreign governments; pursue extraterritorial activities targeting dissidents or journalists; undermine security in countries and regions important to United States national security; and violate well-established principles of international law, including respect for the territorial integrity of states.”
- It then goes on to impose a series of sanctions, including:
- Ceasing any involvement with various financial funds administered by Russia’s central bank, national wealth fund, and ministry of finance, and also expands authority to expand sovereign debt sanctions.
- It also designated six specific corporations it claims provide support to Russian intelligence.
- It sanctioned 32 more individuals and entities that it tied to political operations designed to disrupt the presidential election and spread disinformation
- Add to the pile 8 more individuals and entities tied to Russian actions in the Crimea
- 10 diplomatic personnel are booted
- It formally called out the SVR as the agency behind the SolarWinds breach; the EO mentioned a joint security advisory from the NSA, CISA, and FBI about SVR targeting of the US and its allies, talking about which vulnerabilities the SVR is exploiting to access victim networks, and some mitigation steps that are recommended
- Finally, the EO announced a new course for policymakers worldwide on the policy and technical aspects of publicly attributing cyber incidents, and the expansion of who is participating in an upcoming cybersecurity exercise called CYBER FLAG-21-1.
- Quite a laundry list, eh?
- It’s been relatively rare for the US government to make such clear statements—for reasons we’ve talked about here and in our writings over the years, attribution is hard, and because the diplomatic stakes are high, the government doesn’t want to cast blame out loud without having extremely high confidence in the attribution.
- This group was stood up at the very end of the last administration, and it’s a joint effort by CISA, FBI, ODNI, and the NSA. It was in January that they made their statements of attribution of the SolarWinds event, (attributing it to Russia), though at that time we were still early in the discovery curve and their statement was a little more vague than what you saw in this EO.
- The Biden administration is citing its IC, rather than trashing them, as had been in vogue for a few years prior to now. So really the agreement is because it is the IC whose confidence in the SVR attribution is high.
- Now, other parts of the EO that are not cyber-related have to do with the Russian bounties on US soldiers. There are no specific sanctions as of right now—at least nothing they’re saying publicly—related to that because confidence there is not as high as it is with the cyber events.
- Ultimately, as far as anyone can tell, there’s a certain level of mutually assured destruction in the cyber realm just like in the nuclear one, and I don’t think we’re going to see anything overwhelming. Many folks have pointed out that SolarWinds was an espionage activity. Espionage is accepted, and while no one likes being spied on, all sides have to acknowledge that it’s a thing. That’s a reason that a lot of folks who are experts on cybercraft hesitated to call SolarWinds an “attack,” calling it an intrusion or incursion instead. But it’ll be interesting to see how things develop, for sure.
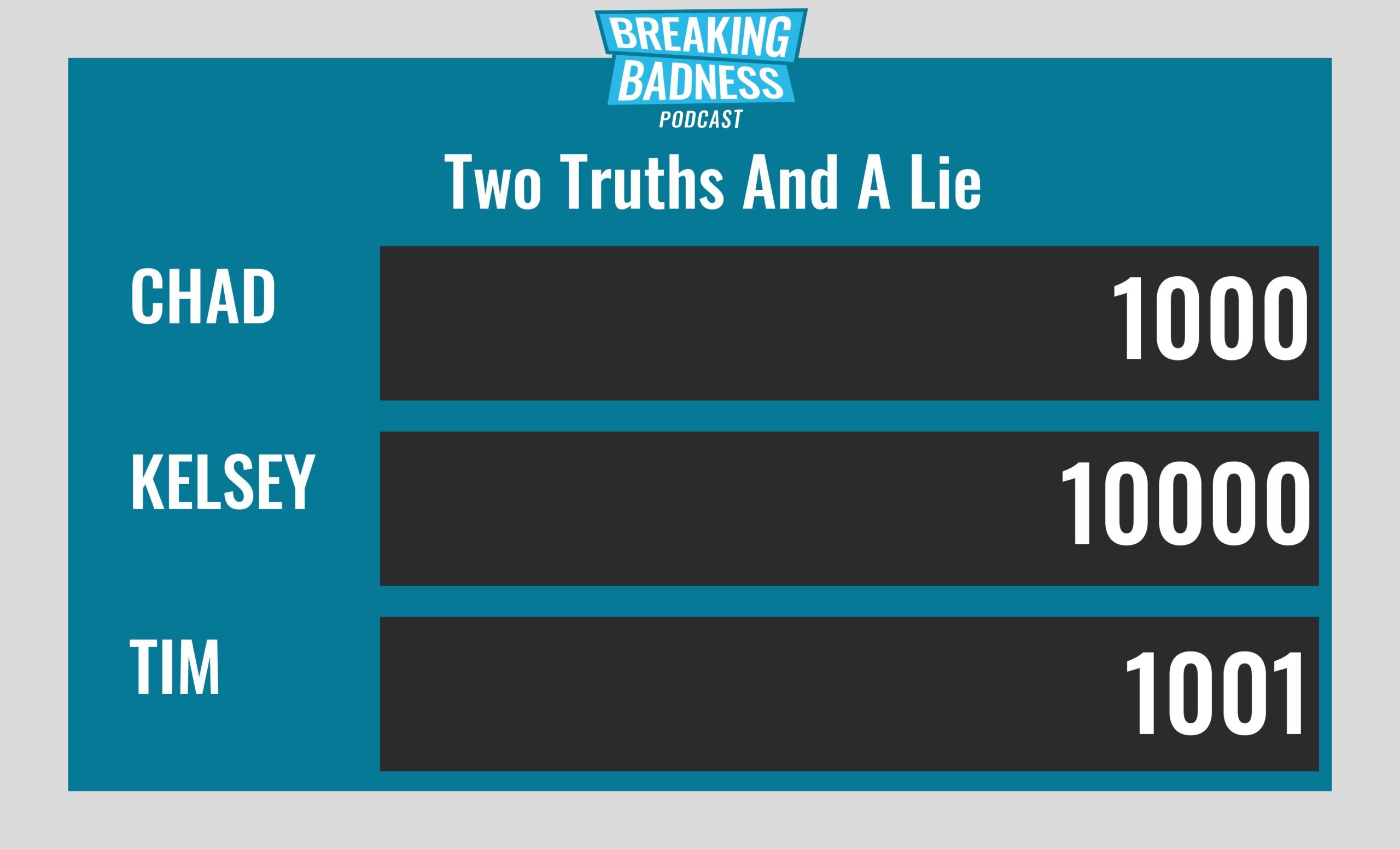
Two Truths and a Lie
Introducing our newest segment on Breaking Badness. We are going to play a game you are all likely familiar with called two truths and a lie, with a fun twist. Each week, one us with come prepared with three article titles, two of which are real, and one is, you guessed it, A LIE.
You'll have to tune in to find out!
Current Scoreboard
This Week’s Hoodie/Goodie Scale
FBI Walks On Web Shells[Chad]: 0 "Oodies"[Tim]: 6/10 Hoodies/Goodies
US Limits Bear Necessities[Chad]: 0 "Oodies"[Tim]: 2/10 Goodies
That’s about all we have for this week, you can find us on Twitter @domaintools, all of the articles mentioned in our podcast will always be included on our podcast recap. Catch us Wednesdays at 9 AM Pacific time when we publish our next podcast and blog.*A special thanks to John Roderick for our incredible podcast music!

