Coming up this week on Breaking Badness. Today we discuss: Telling Cellebrite From Wrong, Keep Your Finger on the Pulse of RCEs, and our fun new game, two truths and a lie.
Here are a few highlights from each article we discussed:
Telling Cellebrite From Wrong
- To better understand this we’d probably have to talk about the cypherpunks and cryptoanarchists. There is a group that was much more prominent in older hacker culture that believed encryption was a tool for keeping oppressive governments in check and that essentially encrypting everything would be the best way to ensure our privacy couldn’t be taken from us. Moxie Marinspike, CTO of Signal, was involved in these groups. So he comes from that background and ethos. Older hacker culture isn’t as government friendly as it is today. It used to be a lot more punks and that natural tension then with government entities was there. These encrypted communications channels are attempts to keep that going.
- Cellebrite claimed they had hacked Signal when in fact they need physical access to your device and just siphon data out of memory. They have this product that people plug into phones and it siphons all the data off including signal texts. Signal doesn’t exist to encrypt at rest though it’s for secure communication. If you have access to any physical device then the keys for any application are running in memory and it should be trivial to get the data off of it. Digital forensics 101 is “catch the guy with the phone unlocked and the laptop unlocked”. Anyways, Cellebrite is linked with tons of authoritarian regimes and journalist persecution.
- There is no vulnerability really. They just added support for the file format used by signal when stored on disk. So basically they just added support for parsing a phone backup. Which really hero software is just a front end to the android and Apple backup software anyways. Their vulnerability was basically just how something works.
- Moxie and the Signal team said as such that this wasn’t a vulnerability but how phones worked. Which is true. It was a little more scathing though since Signal and team are naturally at odds with a company that supports people using their tools for murder and potentially war crimes in oppressive environments.
- Basically—and if you’re listening and haven’t read the blog post you really should, as I won’t do it justice—moxie said he found a Cellebrite device that he miraculously fell off a truck. And that after some fuzzing found that when it parses files you can run arbitrary code on the cellebrite device because of how poor their security is. So he was able to craft files that whenever read will destroy data integrity of the Cellebrite backups.
- This could mean that apps knowing this vulnerability could craft specific files that could destroy these backup tools. It also calls into question tons of court rulings that rely on them right? All of those court rulings where Cellebrite was used to siphon off data can now be called into question. It’s a big deal and super interesting to see where this goes. Moxie jokingly said they’d include the files in Signal, but he is aware of the legal trouble that would cause his foundation and broader mission so I doubt it.
Keep Your Finger on the Pulse of RCEs
- Ivanti Research as well as Mandiant found that a critical vulnerability was being exploited to give malicious actors administrator-level access to these VPN devices. If you can get into a VPN endpoint, then you are inside a protected environment, which is obviously a Bad Thing.
- Let me talk for a second about VPN appliances, because VPNs have become so ubiquitous (not just for remote work, but because so many people use them for privacy and other purposes). These appliances are hardware or virtual machines that sit at the edge of an organization’s protected environment and support connections from authorized and authenticated users into that environment. The user typically has a client application (although sometimes they just run in the browser) that they use to log in to the VPN appliance. Once the connection is accepted, they have an encrypted connection called a “tunnel” and from a networking standpoint, it’s basically identical to being on a LAN in an office.
- So if you imagine an intruder waltzing into an office (and they typically do waltz, though more and more of them are deploying the foxtrot and even the tango) and plugging a laptop into the corporate LAN, that would be extremely scary, right? Especially if they’re as poor a dancer as I am. Well, this RCE grants the same level of access.
- According to the research, victims include US defense, finance, and governmental organizations, and also various organizations in Europe. Actually, Mandiant said that aerospace companies in those regions but also Asia have been hit. Certainly these are high-value targets. Bob’s Muffler Shop is probably not going to be hit here, unless it’s a front for the CIA (which is always possible, given how crappy they are at mufflers). Anyway, it’s the sort of targeting that we typically see from APT groups.
- Mandiant is going pretty strongly with China in their attribution. Two of their UNC groups—that’s “uncategorized”—2630 and 2717—are the ones they see as most likely. These are both activity groups that Mandiant ties to the Chinese government.
- They saw 2630 actively harvesting credentials from Pulse Secure login flows, and 2630 is a group that they had seen last summer targeting American defense companies. They also think that UNC2630 may have ties to APT5, which is Chinese. They base their attribution on a combination of infrastructure, tooling, and on-network behavior, as well as the targeting. The attribution to 2717, as well as the characterization of that group in general, are a little more tenuous, and they are quick to say so in their reporting.
- Unfortunately we can’t tell them to patch the VPN servers yet, because the patch is not out as of today. It’s being estimated for the first week in May or so. In the meantime, the extremely urgent thing to do is to change Active Directory credentials, since it’s entirely likely that the threat actors are moving freely around the protected environment using existing user creds. There are other things they can do, all of which take a lot of work on the part of the network security team, but there’s not really any avoiding that. Assuming that Pulse Secure supports it, they should immediately enable two-factor authentication for critical resources *inside* the network. This is important to note—the vulnerability is able to bypass 2FA for the Pulse Secure device itself, so what I’m talking about here is another layer of authentication for users that have VPN access. It’s a pain, but it’ll help. For work-from-home employees, they can also restrict access to the VPN server to those IP addresses known to belong to legitimate employees. This is FAR from foolproof, since many residential ISPs rotate the IPs of their users, but it is another step that can help tighten security.
- Another option, also a lot of work but it’s possible, is to switch to a different vendor’s VPN appliance. There are tons of them out there. For a company with thousands of employees, that’s going to be a big lift, but unfortunately, really any of the mitigations here are going to be significant efforts. The password resets are probably the least work, but with the vuln unpatched, the actors can use the same methodology to steal the new creds too. This measure would slow them down but not stop them entirely.
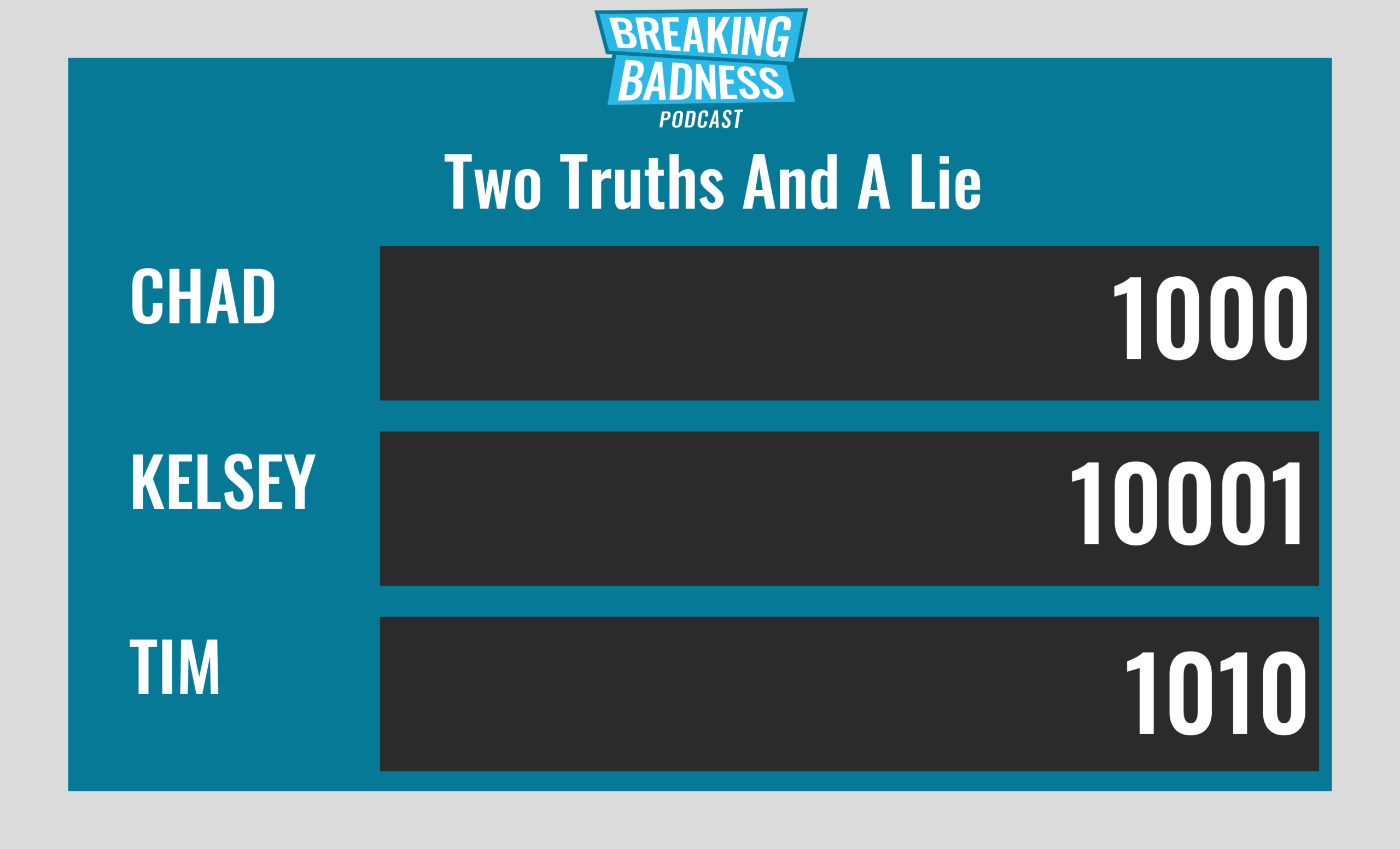
Two Truths and a Lie
Introducing our newest segment on Breaking Badness. We are going to play a game you are all likely familiar with called two truths and a lie, with a fun twist. Each week, one us with come prepared with three article titles, two of which are real, and one is, you guessed it, A LIE.
You’ll have to tune in to find out!
Current Scoreboard
This Week’s Hoodie/Goodie Scale
Telling Cellebrite From Wrong
[Chad]: -11/10 Hoodies
[Tim]: 0/10 Hoodies
Keep Your Finger on the Pulse of RCEs
[Chad]: 11/10 Hoodies
[Tim]: 11/10 Hoodies
That’s about all we have for this week, you can find us on Twitter @domaintools, all of the articles mentioned in our podcast will always be included on our podcast recap. Catch us Wednesdays at 9 AM Pacific time when we publish our next podcast and blog.
*A special thanks to John Roderick for our incredible podcast music!




