Coming up this week on Breaking Badness. Today we discuss: Emotet Your Bottom Dollar, Somewhere Over the Ransomware, and our fun new game, two truths and a lie.
Here are a few highlights from each article we discussed:
Emotet Your Bottom Dollar
- Emotet has long plagued everyone in the defender circles. It was so effective and you would see Emotet samples crop up everywhere when doing searches. Seemed ubiquitous.
- This was the first instance that someone noticed a new payload, and sure enough it was followed by a press release by the DoJ after the analysis by milkream popped up on Twitter. Funny how Twitter is always the fastest way to receive security news.
- The DoJ press release highlighted all the law enforcement partners they worked with and that they used these partners to load the uninstaller on tier 2 and tier 3 servers in the Emotet bot network.
- This payload uninstalls the Emotet software on April 25, 2021. People originally thought that this was actually March 25, 2021, but that’s due to analysts forgetting that programmers always count from zero. In any case, it is a rather simple DLL that just cleans up the associated Emotet files and removes its persistence mechanisms.
- Persistence for Emotet was obtained through both a registry run key that fires off on boot and a system service. Pretty typical stuff for most malware. It’s effective and works so most pieces of Windows malware use it.
- There’s a bit of code problem with how they were intending to move the law enforcement file into the temp directory. Since they got the syntax wrong a file path is just created then the cleanup routine runs. Minor glitch.
- If the uninstall isn’t immediately called, there is another DLL that gets called and it looks and operates like a regularly obfuscated Emotet DLL, this is different from the uninstall DLL.
- The final option built into this payload calls out to a law enforcement controlled C2 server. From what I understand this was meant to be an “if Emotet operator figured out how to stop the uninstall” DLL. This way they would get some telemetry of what is happening.
- Emotet has seen its bot network largely dismantled, but I doubt that will be the end. We talk about this with takedowns and government action on the podcast all the time and I just don’t really see a world where unless an operator is behind bars that they’d stop. In fact, this is probably a good chance to fix things they didn’t like in their original code, improve upon mechanisms that could keep them from getting uninstalled in the future. If anything we’ll see a more effective Emotet emerge from this. That said I like these rogue elements—the removal of the bots, the removal of webshells on vulnerable Exchange servers, and even people doing rogue patching of vulnerable IoT devices to stop the Mirai variants. People get offended because you touched THEIR device on THEIR network, but when you aren’t paying attention and taking care of it yourself someone needs to come along and do cleanup. Just my take, but I’m also not against a little red team work to get the job done.
Somewhere Over the Ransomware
- The ransomware task force is a really interesting development. It’s a group composed of leadership from some of the big players you’d expect, like Microsoft, Palo Alto Networks, and Rapid7, as well as NGOs like the Cyber Threat Alliance, Global Cyber Alliance, and the Institute for Security and Technology.
- A few ransomware stats highlighted by this task force: example, the average payment is over $312K, up 171% over 2019 according to Palo Alto. Chainalysis says that total payments are over $350M, which is a 300% increase over the prior year. Average downtime is 3 weeks, per Coveware, and the number of US organizations hit in 2020 was 3 x 800, or 2400.
- The framework is organized around four goals: deter ransomware attacks through a nationally and internationally coordinated, comprehensive strategy; disrupt the ransomware business model and reduce criminal profits; help organizations prepare for ransomware attacks; and respond to ransomware attacks more effectively. All of those sound like motherhood and apple pie, but when you look at the actual 48 recommendations, they get very specific about some of the ways they see governments and the private sector being able to help with these things. Would you like me to do a dramatic reading of all 48?
- No? OK, well basically they’re looking to a coalition of government and private sector organizations, and one of the key things is that they need everyone globally to be on the same page. International cooperation is one of the points they really hammer home. There are other collective efforts they propose, like pooling a “war chest” for insurance companies to carry out subrogation activities, which is where they attempt to recover losses on behalf of the insured—they can’t often really afford this on an individual basis, but with the pooling of funds that is the basis of insurance in general, this becomes more possible.
- The asks for Congress were interesting. One of them is that they want to shield companies from legal liability in taking defensive measures. For example, today, a telecommunications company that blocks malicious traffic can actually face some legal liability for doing so. This task force wants Congress to provide some legal indemnification for these kinds of actions. They’re very clear that they aren’t advocating authorizing hacking back, however.
- The report lays out some good steps we can take as an industry to help dismantle ransomware. Mostly they can be summarized as encouraging information sharing within industry and across industry to government lines. If you come back to those four high level goals of deterring attacks, disrupting the business model, helping organizations prepare for attacks, and helping them respond to attacks, there’s something for the security industry in each of those. Disruption of the business model is going to be one of the tougher ones for our industry to participate in, IMHO; there’s going to have to be a lot of regulation and cooperation to get, for example, the cryptocurrency industry to become more forthcoming with payment indicators.
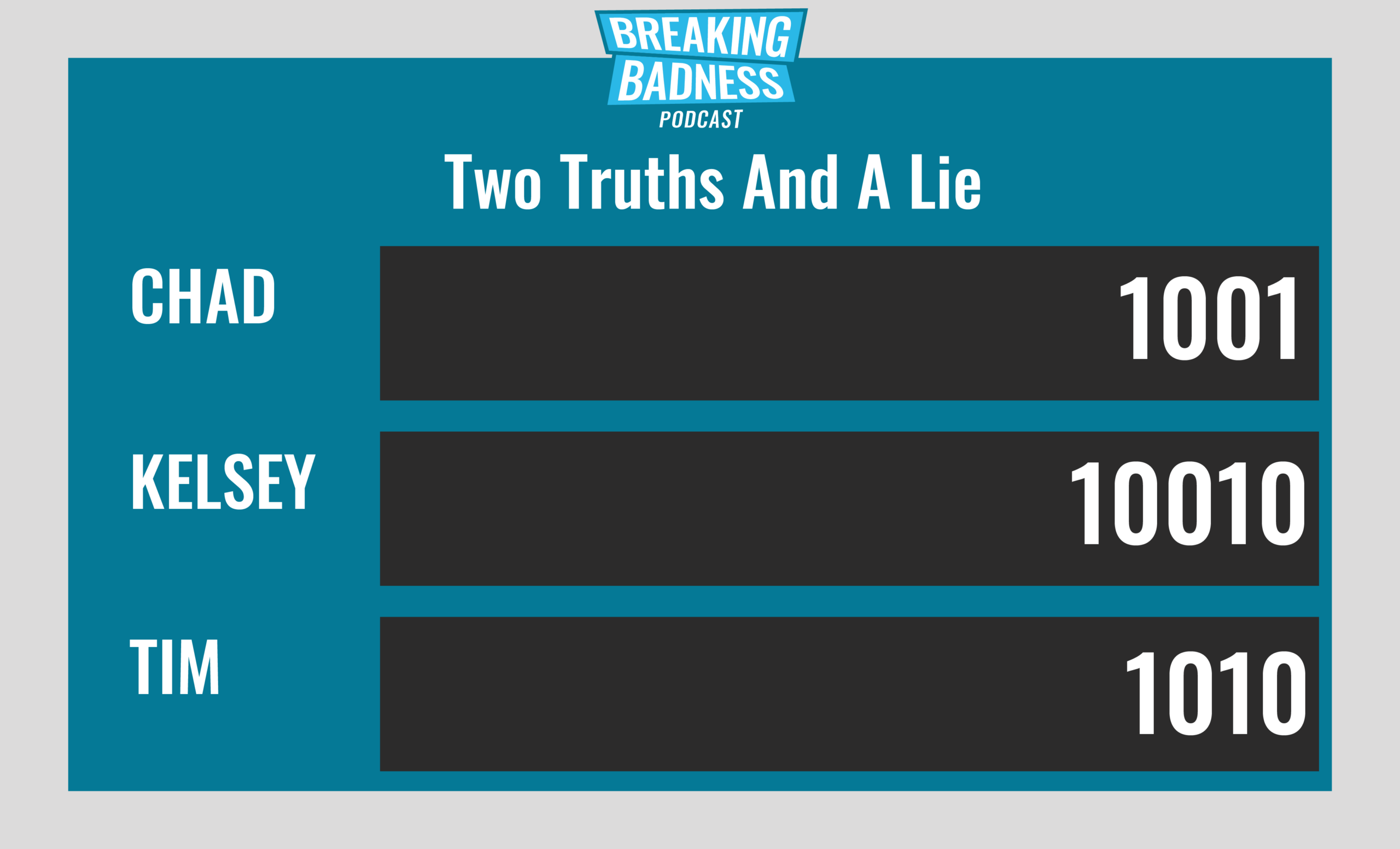
Two Truths and a Lie
Introducing our newest segment on Breaking Badness. We are going to play a game you are all likely familiar with called two truths and a lie, with a fun twist. Each week, one us with come prepared with three article titles, two of which are real, and one is, you guessed it, A LIE.
You’ll have to tune in to find out!
Current Scoreboard
This Week’s Hoodie/Goodie Scale
Emotet Your Bottom Dollar
[Chad]: 5/10 Anti-Hoodies
[Tim]: 9/10 Anti-Hoodies
Somewhere Over the Ransomware
[Chad]: 7/10 Anti-Hoodies
[Tim]: 6/10 Anti-Hoodies
That’s about all we have for this week, you can find us on Twitter @domaintools, all of the articles mentioned in our podcast will always be included on our podcast recap. Catch us Wednesdays at 9 AM Pacific time when we publish our next podcast and blog.
*A special thanks to John Roderick for our incredible podcast music!




