PhishEye
Overview
Phishing is among the most common—and costly—vectors used by criminals for attacks and data breaches. According to the Anti Phishing Working Group, the numbers of new phishing domains are increasing almost every quarter. Chances are, your company, your employees, and your customers, have been targeted. In many cases, the domains involved in these attacks are meant to mimic your own brand names or domains to trick victims into falling for the attack.
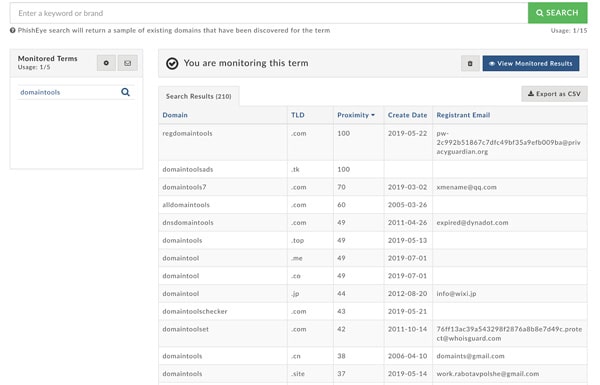
DomainTools PhishEye is a potent new tool in your battle against these nefarious domains and the criminals who operate them. Leveraging DomainTools’ unique visibility into over 315 million current domains—the largest database of its kind anywhere—PhishEye finds domains that mimic your properties, whether by typo or by combining your brand with other terms—terms like “account,” “login,” “online,” or countless others.
PhishEye is simple, yet powerful. Enter a keyword, and PhishEye will show a sample of the existing domains that mimic that term. Then, you can set an alert to be notified of any new domain registrations that match the same criteria. DomainTools processes around 5 million new Whois records every day, making it virtually impossible for phishers to hide their doings from your PhishEye alerts.
Getting Started
Once your account has been provisioned with PhishEye, you can find the tool here:
https://research.domaintools.com/phisheye
Be sure you are logged in, or log in when prompted.
PhishEye has two main areas of function: configuration and alerting. For most users, alerting is the priority.
You set up your PhishEye alerts by starting with a search to find relevant domains. PhishEye uses a number of algorithms to find domains that are relevant to your keyword:
- Typos such as character substitutions or repeated characters (e.g. domaint00ls.com or domaintoools.com) and several other kinds of typos
- More technical variants such as bitflips
- Substring inclusions (e.g. domaintools-account.com)
- …and several other kinds of variants
PhishEye searches the DomainTools database for domains that are pertinent to the keyword. When you view the search results, you have the option to set up an alert on the term. Or, you can run a different search based on another keyword.
Entering Search Terms
You search on one keyword at a time, and then decide whether you want to monitor that term. You can make exclusions if you believe that your term will result in irrelevant “noise” domains. This is especially relevant for words that are both short and generic; for example, for the term “chase,” PhishEye would find matches in any domains that included the word “purchase,” “chased,” etc. To exclude certain matches, use a hyphen with the words to exclude:
- chase -purchase -chased
NOTE: Your search term must consist only of the characters that are valid for domain names: (a-z, 0-9, -)
Configuring Alerts
After running a search, you set up alerts by clicking the “+ Start Monitoring” button. Alerts are delivered in two ways: by email, and, optionally, via the PhishEye API (covered later).
Email Options
Enter the email addresses to which the alerts should be sent. PhishEye allows up to ten email recipients. If you have a larger group of personnel who need to see the alerts, you may want to configure an email alias that includes all of the users.
There are two formats—Summary and Detailed. The detailed view is great for getting a quick overview of the domains that PhishEye discovers, but be aware that some email filtering systems may trigger on the alert emails due to the nature of the domains contained in them. If you are concerned about this, choose the Summary view. Both views tell you how many domains were discovered for each keyword you are monitoring.
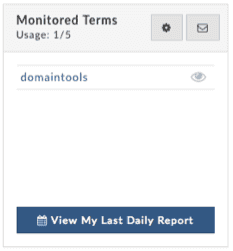
Viewing Alert Reports
When PhishEye discovers new domains corresponding to your monitored keywords, you can see details about the domains in the daily reports interface.
When you click View My Last Daily Report, PhishEye presents the report from the most recent day on which it found results for one or more of your terms. It may be that some days go by without any new domains, so this report may not always show “today.”
When you have alerts configured and receiving results, any time you log in to PhishEye, you will be taken to your Daily Report page.
The report is organized per keyword. The table includes the following fields:
- Domain (links to Whois page for the domain)
- TLD
- Risk Score (as calculated by the Domain Risk Score)
- Created Date
- Registrar
- Registrant Email
- IP addresses (links to the IP Whois page)
- IP Country
- Name Servers
You can sort on any of the columns to pinpoint domains of interest.
Controls in the Report Table
- “Today” or date: clicking this item, above the table to the left, brings up a menu that allows you to select an earlier daily report. Reports go back 7 days.
- Back: this takes you back to the main PhishEye configuration page
- Export: allows you to export PhishEye domains as a .csv or to DomainTools Iris (more detail below)
- Expand: this control, at the upper-right, toggles the table between a compact view and a full-width view. NOTE: even when expanded, on some screens you may need to scroll horizontally to see all data.
- Keyword (in table section header): clicking the keyword takes you to a view of the last 7 days’ reports for that keyword
- Per-keyword export (down arrow icon): this control gives you the option of a .csv or Iris export of only the domains matching this keyword
- Hide/Show: toggles between showing and hiding the domains for each keyword
Export to Iris or .csv
If you need to learn more about the domains that PhishEye discovers, with a click, you can export them to DomainTools Iris for a deeper exploration of the domains, their infrastructure, and the threat actors controlling them. There are two options:
- Create New Investigation: Opens Iris in a new tab and instantiates a new investigation with the domains from PhishEye as the query
- Add to Existing Investigation: provides a hash which can be used with the Import function in the Advanced view in Iris, to add the PhishEye domains to an existing Iris investigation
Many PhishEye users will wish to block the discovered domains in an email or messaging security system, or to query for them in a SIEM or other alerting or forensics tool. The .csv export function gives you the domains in a broadly consumable format to enable custom blocking or querying.
Search and Alert Usage Limits; PhishEye API
PhishEye searches and alerts are counted separately. The base PhishEye package enables 15 searches and 5 monitors. This allows you to get a feel for which of your keywords may bear the closest watching.
When multiple people on an account have access to PhishEye, it is important to understand the relationship between the access limits and the terms shown in the PhishEye UI.
- Usage is shared: Any search and any alert done by any member of the account count against the overall usage. If Alice and Bob both have access on a group membership with PhishEye, and Alice searches for 3 terms and sets alerts for one of them, Bob will have 12 remaining searches and 4 alerts.
- Users see only their own monitored terms: Bob and Alice will not see each other’s terms in the PhishEye UI. Since usage is shared, this means that the usage for alerts could be higher than what any given user sees in their monitored terms. In the scenario above, if Alice configures one alert, then Bob will see his usage at 1 of 5 alerts, even though he won’t see any terms in his “Monitored Terms” window. If Bob then sets up two more terms (and Alice still has her single original term), she will then see usage at 3 of 5, but just the one term in her Monitored Terms window.
- API and Web UI: the PhishEye API is purely for alerts. It does not cover the search function. Specifically, the API pulls alerts for the terms for the account holder who has the API key. In the above scenario, if Alice’s DomainTools login is the one to which the API key is tied, then the API will get alerts for domains matching the term(s) Alice has configured, but not the terms Bob has configured. Therefore, if multiple users on a group account have access to PhishEye, and you wish to use the API, you must coordinate among group members to make sure the user with the API keys is the user who sets up the alerts in the PhishEye UI.
Information about the PhishEye API is here: https://www.domaintools.com/resources/api-documentation/phisheye


