Exploiting Your Adversary’s Weak Spot: DNS Domain Names – A Natural Fit for SOAR
Sometimes it feels like the bad guys hold all the cards but they have weak spots too. We just have to know where to look. For instance, most attack scenarios require early on that the attacker gain persistence and that it’s very difficult to do that without making a sound. But here’s another example: bad guys widely rely on DNS and domain names just like everyone else.
In most attack scenarios bad guys have to stand up some infrastructure to host things like staging, command and control and exfiltration destinations. To varying degrees attackers may use compromised assets of other unwitting organizations or infrastructure they directly control. But they have to be ready to move when their virtual hideout is discovered shutdown or added to a threat intel list. That means the IP addresses of their C&C servers and related infrastructure may change frequently. So they use the same technology everyone else uses to find the current IP address for a given resource – domain names.
In this real training for free event, we will provide an overview of the important role DNS and domain names play in today’s attack scenarios and explore proven risk factors for predicting the threat potential of a domain name that comes across your radar whether from a DNS server log, phishing email or any of many other log sources. We will look at how to interpret
- When was the domain registered?
- How many other domains share characteristics with this domain?
- What is the email/website infrastructure for the domain?
- Learning from older malicious domains to recognize new ones
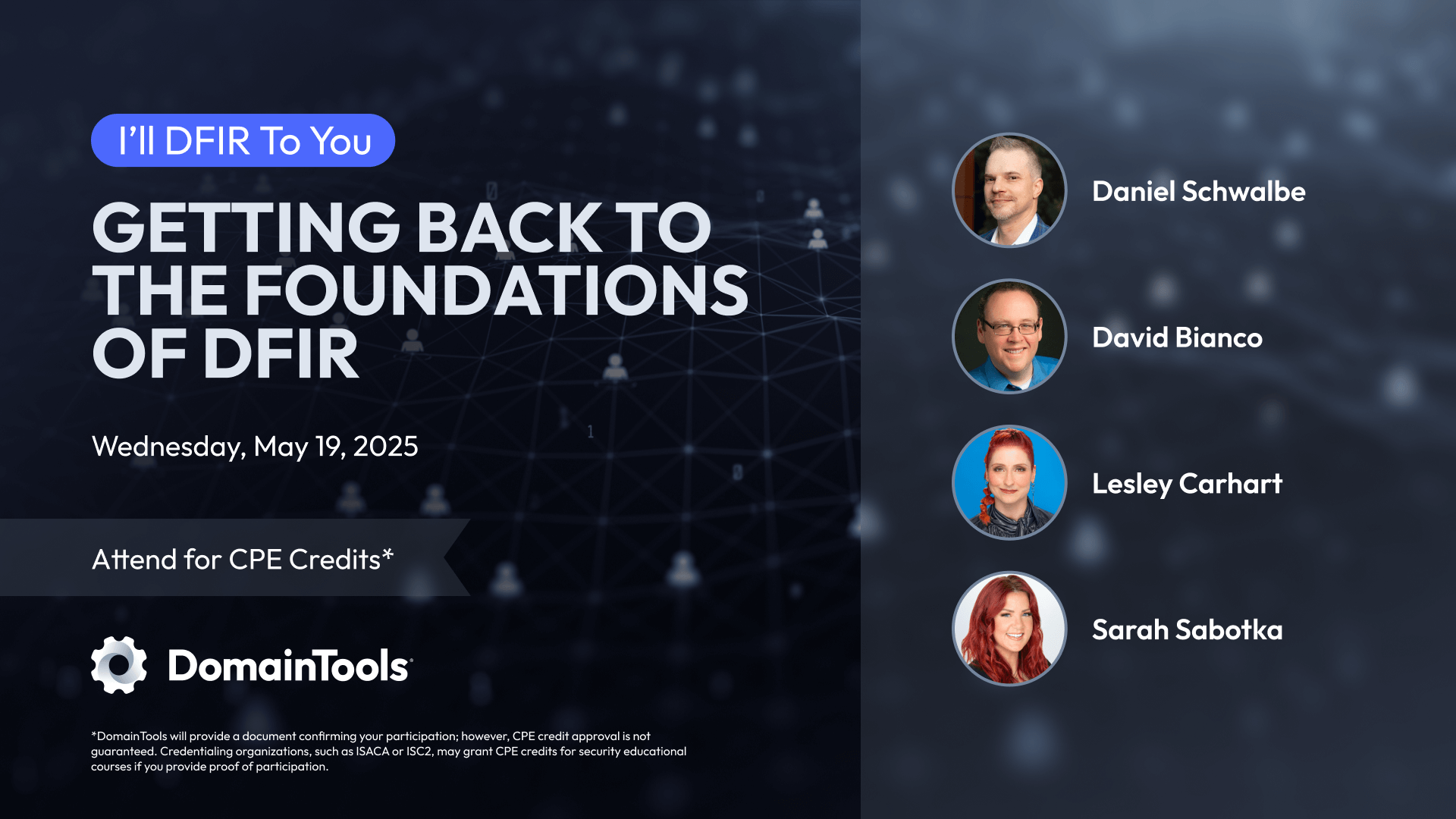
But no organization can manually assess every domain name and that’s where Security Orchestration and Automation come in to play. Our sponsor, DomainTools, is a leader in domain name risk analysis and will briefly show how they are working with SIEM, UEBA and other partners to accelerate threat detection with real world SOAR scenarios.