Return to Sender - A Brief Analysis of a US Postal Service Smishing Campaign
In recent weeks there has been a noticeable uptick in campaigns targeting the US Postal Service (USPS) as an institution, even in the usual deluge of phishing and smishing emails and text messages. The volume of these reaching our families and co-workers within a period of weeks piqued our natural curiosity to dig into it and see where it leads. An example of one of these smishing messages is shown in Figure 1.
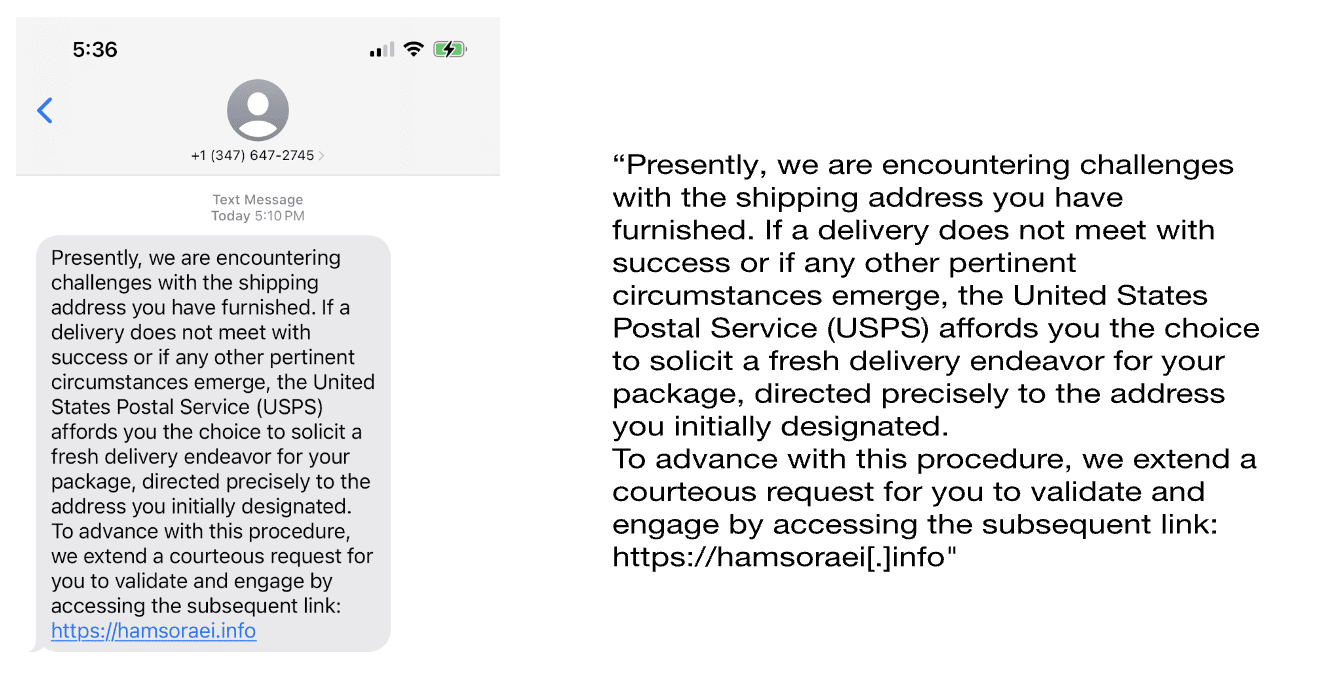
At first glance, the choice of language in the text seems suspect. Likely adopted from another phishing script and used over in this campaign, the phrasing shows signs that it was written by someone that either has English as an additional language, or has limited proficiency and likely relied on a translation service to help craft the message. Thankfully they didn’t have the foresight to use a platform like ChatGPT to help craft the content, which could have generated a more convincing lure.
Pivoting on hamsoraei[.]info
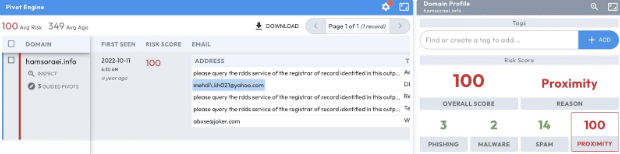
As we start to look into the domain mentioned in the text message, Figure 2 glows in the dark with a risk score of 100, the highest you can get, reflecting both the infrastructure and other previous malicious activity as well as other domains associated with it. In this case, the score is in part tied to the domain’s start of authority record (SOA), a Yahoo email mehdi\.kh021@yahoo[.]com. This unique email address, containing a backslash, is associated with 71 other domains. From here, guided pivots in Iris Investigate can be a helpful way to quickly identify more domains from this initial indicator of compromise (IOC).
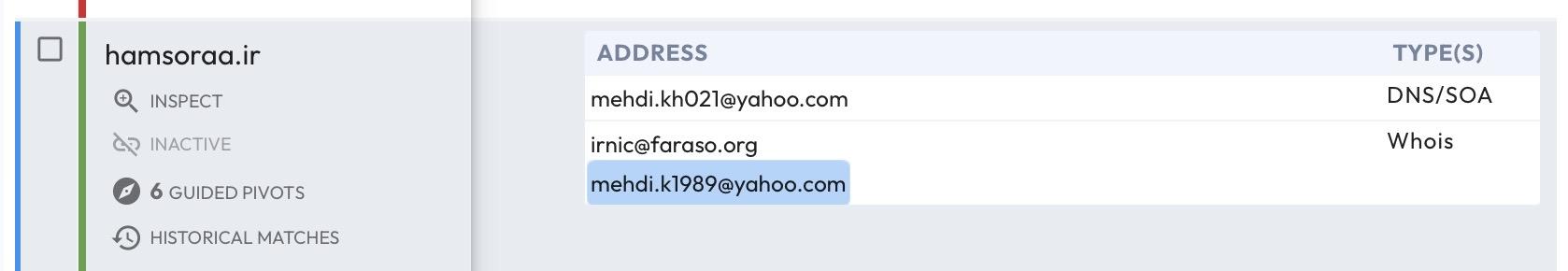
By expanding our search, we can see a host of domains registered by an email address using a familiar naming convention, mehdi.k1989@yahoo[.]com, varying only by the 5 characters after the period in the email. This second email address is associated with 63 domains which also share above average risk scores. We also note a variation of the SOA record email that is missing the “\”–this variation adds an additional 30 domains to our running count of 163 domains at this point of our investigation.
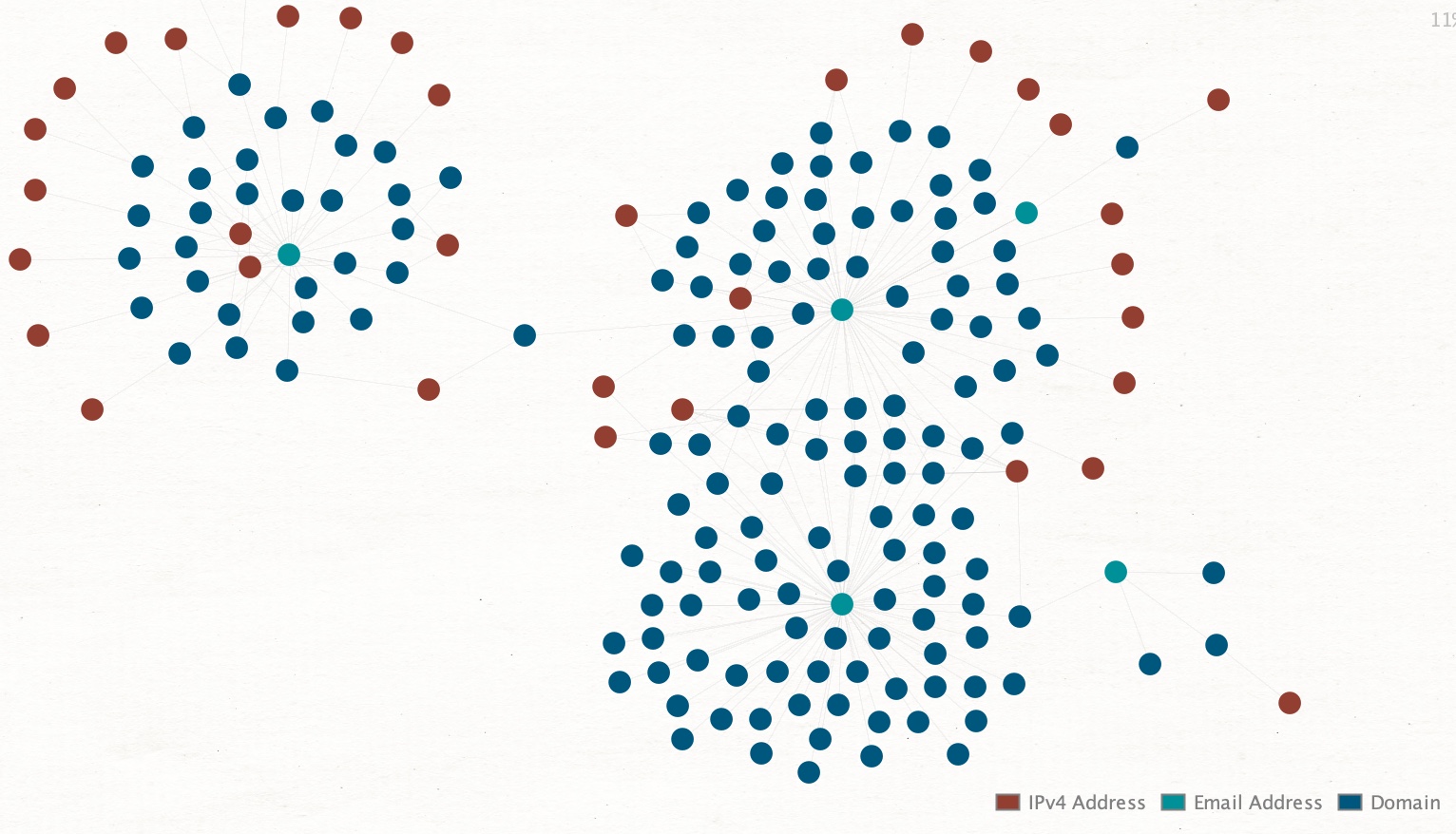
By continuing to pivot through IOCs related to this person of interest, we start to get the full picture of domains and hosting infrastructure related to our investigation. Visualization tools, such as Maltego, allow us to better understand the scope and history of activity and quickly see their connections. Figure 4 shows data from this investigation using a Maltego transform on data from the DomainTools Iris platform.
When looking at indicators like email addresses that have been associated with a fairly high degree of recidivism from a domain registration perspective, it is not uncommon for individuals to reuse these addresses for other purposes as well. This ended up being true here. By using publicly available OSINT sources, you can enumerate and connect additional items related to your investigation. In this case, the person of interest used the same email addresses not only to register for different services, but tied the emails together by using them as back up or secondary emails for a number of other accounts. When these additional accounts are included, we uncover an additional 20 domains tied to the same person.
When individuals don’t expect this data to come to light, they may become lax in what else they tie to these items, including social media and other accounts that are useful in expanding and adding new prospective avenues for inquiry. This too was present in this investigation as highlighted by the Facebook account we found in Figure 5.
Reviewing this additional social media information, we have reason to believe our person of interest is an Iranian national who lives and works in Tehran, and who may have attended the Islamic Azad University. From our investigation, it is unclear what level of fluency they have in English, but could prospectively be in keeping with our initial observation that the lure text of the smish was likely not written by someone whose native language is English.
Conclusion
Even though phishing and smishing campaigns have become an unfortunate daily fact of life, they remain a significant source of prospective harm for not only individuals, but the companies and organizations whose services they use. The resulting harm both from a loss perspective as well as the emotional toll on individuals, is added to the cost in time, money, and resources that companies face in defending their customers and ensuring that their brand reputation and business operations are not impacted.
In this article, we were able to start with a single domain found in USPS smishing campaign and pivot out to identify nearly 200 domains and several email addresses associated with this threat actor. These pivots eventually lead us to a Facebook account associated with a person of interest for this campaign.
For those organizations and the law enforcement agencies that help combat and prosecute these criminal acts, being able to quickly and thoroughly identify the infrastructure and individuals associated with it, becomes important in minimizing the harm it causes. DomainTools data and services are curated and designed to identify threats, power investigations, and respond effectively to campaigns such as this. If you want to know more, please contact us.
IOCS
Emails

