Merry Phishmas: Beware US Postal Service Phishing During the Holidays

For Cybercriminals, the Season of Giving is a Season for Taking
Special note: A podcast is available on this topic, you can tune in below.
below.
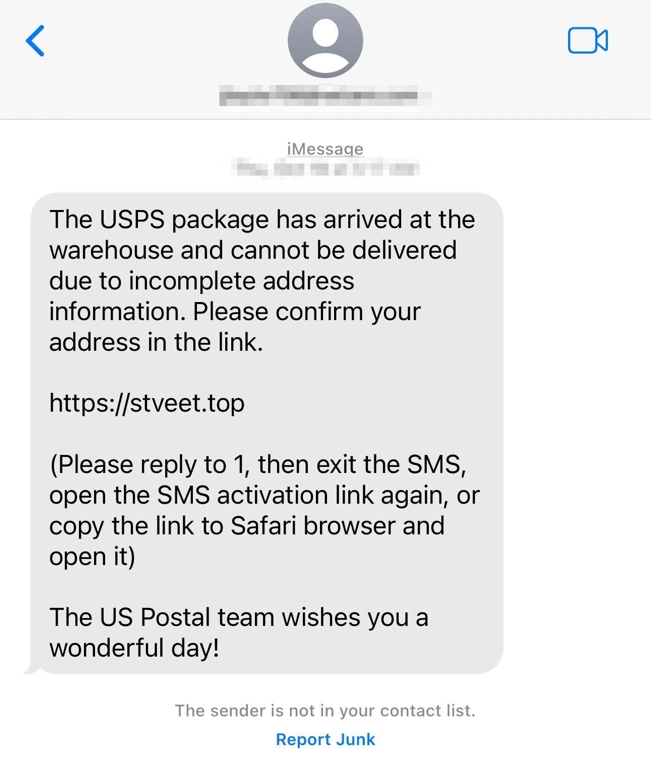
With the holiday season approaching, DomainTools urges the public to exercise increased caution and remain vigilant against the threat of US Postal Service-themed (USPS) package redelivery phishing attacks. DomainTools is monitoring several USPS phishing campaigns, including activity that aligns with known tactics, techniques, and procedures of the China-based “Chenlun” phishing actor and their affiliates that other researchers have described (Figure 1). But USPS phishing is by no means limited to a small cadre of threat actors, and this reality makes protecting potential targets challenging.
DomainTools believes the large volume and comparably high success rate these phishes generate will encourage other threat actors in eastern Asia and elsewhere to follow. Evidence suggests this may already be happening, with “Chenlun” adjacent threat actors following a similar targeting trajectory and “borrowing” content. To understand this shift, one must first consider the key value drivers these phishes offer cybercriminals and what motivates them to target one organization over another. In the context of USPS phishes described here, some reasons for such a targeting shift include:
- The primary phishing lure delivery method (email-to-SMS and/or iMessage) is less suspicious to recipients, less easily filtered by platform providers, and more deliverable to targets. Within the context of an undeliverable package, receiving a text message alert seems plausible. More successfully delivered phishing lures mean more potential engagement with a deployed phish.
- “Chenlun” phishes are somewhat difficult to detect when deployed and properly configured, and they capture the “look and feel” of a trusted brand. A well-designed phishing kit using modern web development frameworks paired with robust lure sending capabilities makes a deployed phishing kit more polished and convincing.
- The high volume of domain registrations and hosting infrastructure associated with “Chenlun” appears to be controlled by a small group of people. They have relatively disciplined OPSEC and a preference for offshore hosting providers. In essence, the longer a heavily promoted and higher quality phish remains deployed, the more likely it will convert targets into victims.
- Location also matters when considering risk. Threat actors whose physical presence is in countries which may not enforce punitive actions can make cybercrime campaigns more durable.
In short, phishing actors targeting decisions are based on potential financial upside and risk tolerance. Considering these factors, USPS phishing activity will likely continue to increase until threat actor ability to send phishing lures is significantly degraded or the business decision calculus behind such phishing campaigns presents insufficient upside. This likelihood is supported further by past phishing activity by “Chenlun” and others that first sought to impersonate the postal services of other countries before apparently prioritizing targets in the United States. The reason for such pivoting is almost certainly a decision based on cost-benefit analysis.
That said, opportunities exist to improve tracking and mitigation of this and related phishing activity. To that point, the interplay between open source intelligence and domain-related data not only improves tracking of a threat actor’s phishing activity, but it can also help deter future criminality. Pairing domain-related data with other data sources for pivots can prove a potent combination for anti-phishing operations that also offer valuable footholds for understanding the how and why of a particular phishing campaign.
The Deceptive Simplicity of USPS Package Redelivery Phishes
Impersonating one of the most recognized and trusted brands in the United States offers significant upside to cybercriminals, and the “Chenlun” kit uses layered deception to accomplish its purpose: the theft of payment card and billing data. Stolen data from these phishes will likely be used for payment fraud in addition to being shared or sold within cybercrime communities.
After interacting with a malicious domain from a phishing lure, targets are greeted by a simple (and false) choice designed to use anxiety to produce action: share sensitive data or risk losing a package. A target sees USPS branding with a warning message: “Delivery failed, addressee unknown” (Figure 2). The kit also uses an IP location service to geolocate visitors to make the phish appear more convincing. Within the context of the holiday season, the social engineering undergirding such a phish appears especially compelling–and sinister.
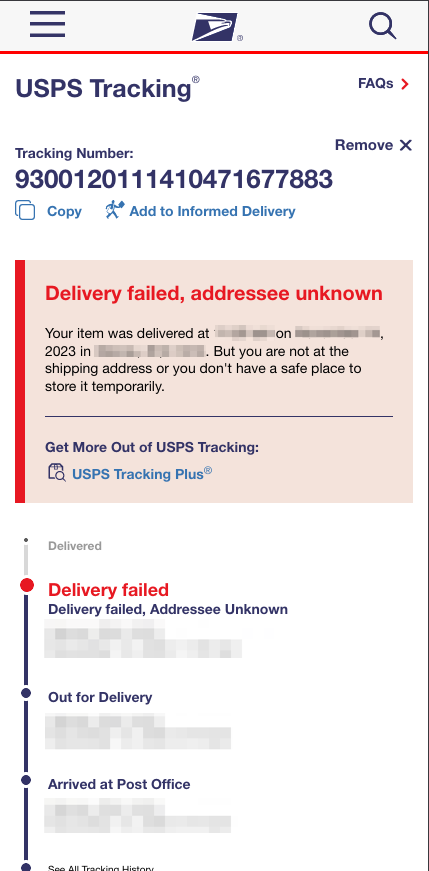
location information was based on IP address geolocation.
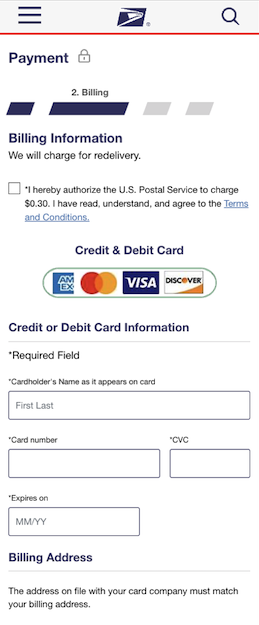
In addition to collecting contact information from a target, this phish exists to build just enough trust that a victim discloses payment-related data on the “payment” page, its ultimate goal (Figure 3). Notably, this kit uses fairly good validation techniques to identify and filter invalid results.
Artifacts in “Chenlun” Phishing Kits
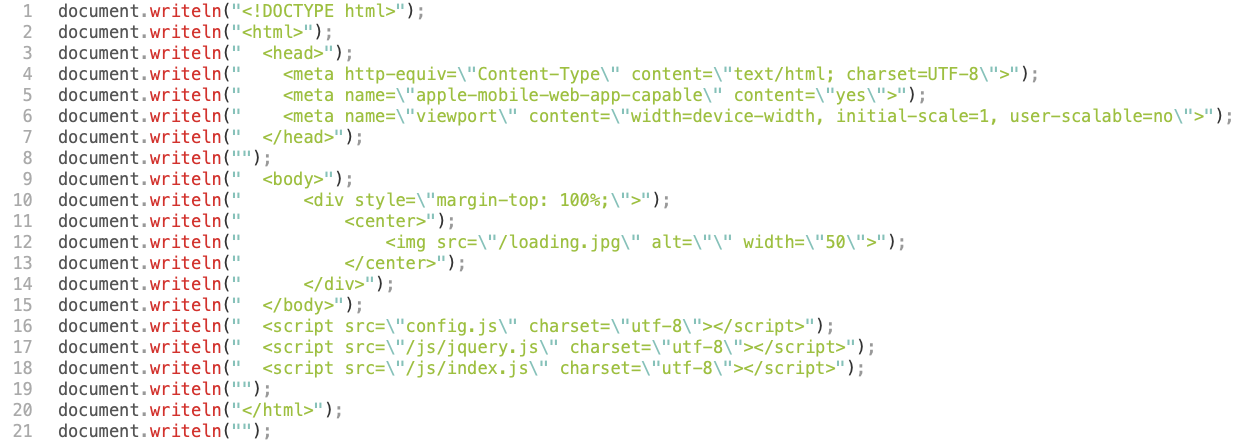
Notable characteristics of “Chenlun” phishing kit include its configuration files and anti-detection functionality (Figure 4). When implemented properly, these techniques make phish detection through manual or automated means more difficult and thus increase the lifespan of a deployed phish. When not implemented properly, these techniques add complexity and become counterproductive. The “Chenlun” phishing kit is a mixture of both good and bad, with each presenting potential footholds for investigators.
To date, identified “Chenlun” phishes use one of two distinctive configuration files. In Figure 5, an easily accessible configuration file reveals parts of the phishing kit’s functionality and how it processes form data. These findings align with what Spanish security researcher g0njxa reported: exposed Telegram API credentials, Telegram chat IDs, and flawed management panels. One need only look to the file named “urlConfig.json” for exposed Telegram API credentials.
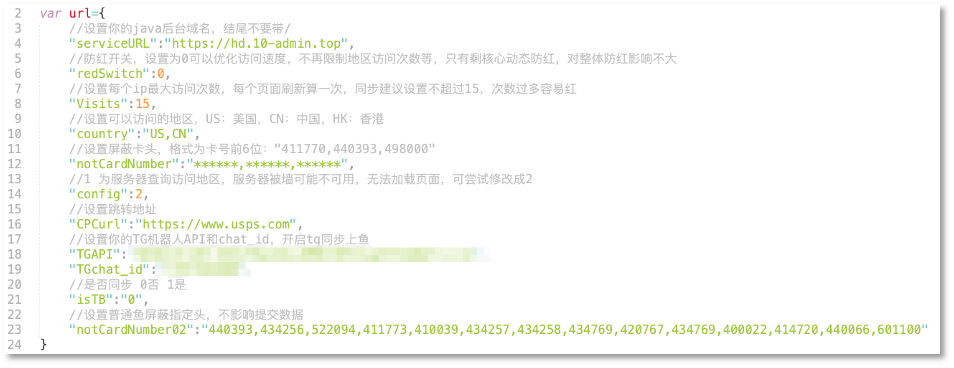
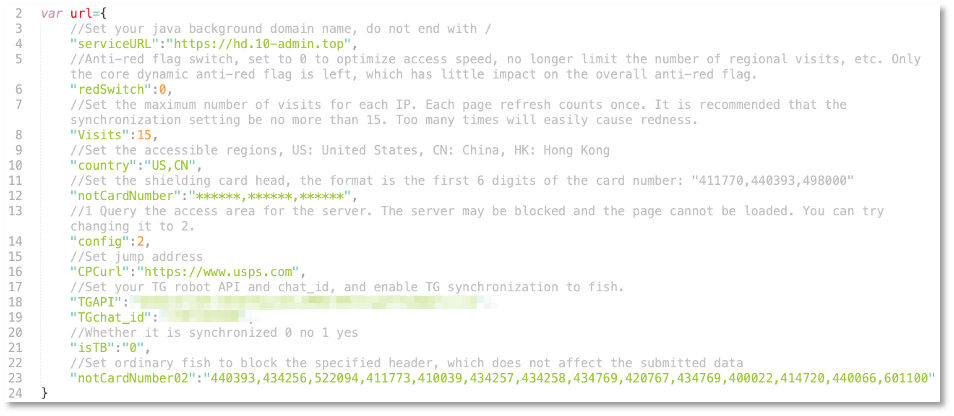
These configuration variables reveal additional phishing kit details, including how phished payment data is formatted when posted to a specific Telegram chat along with the Telegram API credentials required to do so. Some other notable configuration variables include:
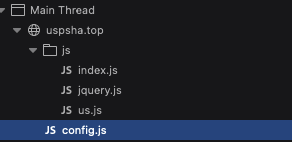
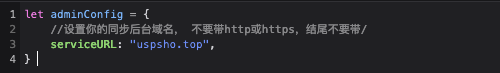
A secondary type of “Chenlun” phish uses a different file structure and configuration. For example, a phish deployed at uspsha[.]top has “config.js” for its primary configuration file (Figures 6-7).
“Chenlun” Activity Targeting Beyond the United States
“Chenlun” also has a history of targeting postal services in other countries. Notably, Correos de Chile is a frequent target. The file structure, configuration files, and objective these phishing kits bear an uncanny similarity with those impersonating the USPS. Moreover, historical analysis of this threat actor’s targeting suggests Spanish-language postal services were targets before the USPS. The same applies for countless other countries.

Linking Additional Domains with Linkfly
Another helpful characteristic of “Chenlun” phishing is its frequent use of the “Linkfly” service which appears to be for phishing campaign tracking and URL redirection. This reveals a useful pivot: the website title “USPS – Linkfly” (Figure 9).
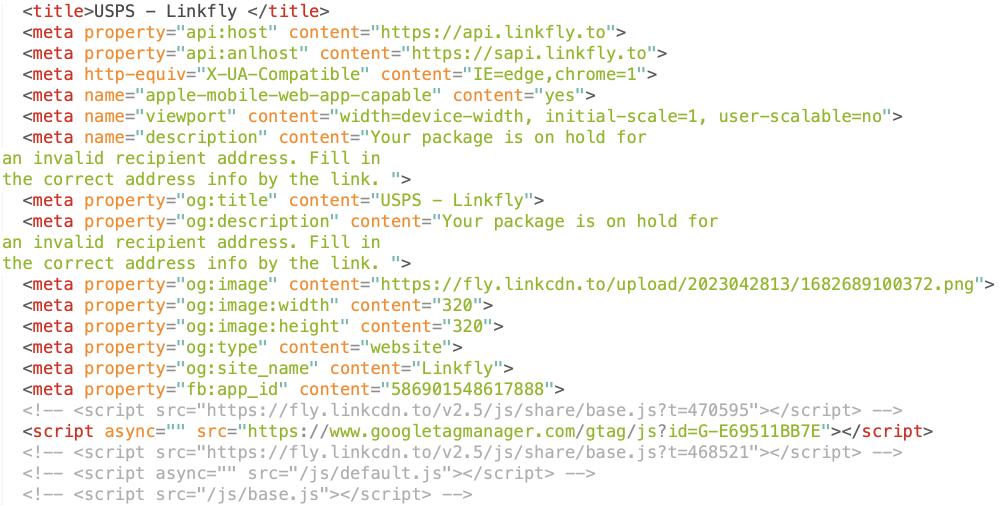
Using the website title search functionality in DomainTools Iris Investigate reveals several hundred domains with the “USPS – Linkfly” website title, each with a very high risk score. Many of them redirect traffic to the legitimate USPS[.]com, another helpful indicator. A few examples of these domains are listed below; a more complete list is provided in the Appendix:
admin-2022[.]life
admin2022[.]monster
deliver-usps-address[.]com
delivery-usps[.]top
error-usps-info[.]com
iq0j6ohh7[.]us
uspsc9[.]top
uspsofficialservice[.]com
uspspsf[.]top
usptrackiht[.]top
usptrackxp[.]top
The domain naming conventions and choices of TLD for these domains closely resemble already identified “Chenlun” phishing domains–including ones used for phishing management panels. Further, several domains identified using the title “USPS – Linkfly” used configuration files containing the same Telegram API credentials mentioned earlier.
Despite disciplined use of domain registration privacy across “Chenlun” phishing domains, one exception provides several useful pivots. The domain iq0j6ohh7[.]us from the list above has the following–certainly fictitious but thankfully distinctive–registrant information assigned to it:
Matt Kik
40 Wall Street
New York, NY 10005
United States
t9296258844@gmail[.]com
This same email address appears in whois records for several hundred additional suspicious domains whose purpose is likely to serve as malicious redirection domains. Pivoting further with the domain registrant name “Matt Kik” for domains that also use the address “40 Wall Street” revealed a set of additional registrant email addresses. One such email address is 7user@csmsonline[.]com.
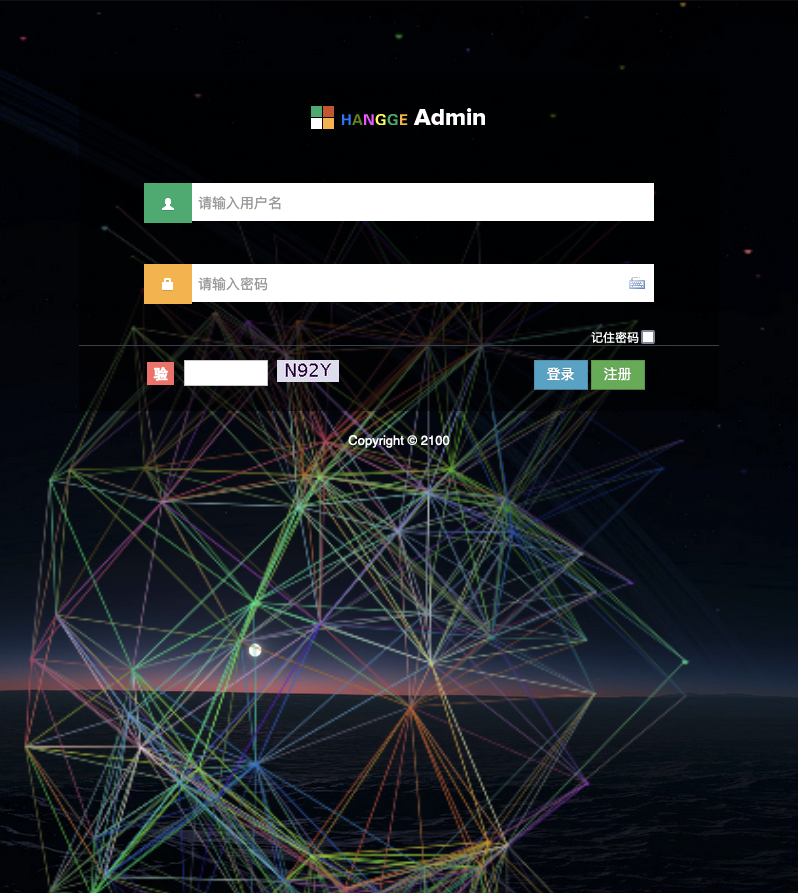
Visiting the URL https://csmsonline[.]com/smscloak reveals a login panel titled “SMS Admin” (Figure 10). The directory /smscloak likely refers to SMSCloak, a two year old company in Shenzhen offering an international SMS integration platform and marketing copy service for SMS advertisements. The extent of this panel’s current functionality remains unclear. While the presence of such a panel is not inherently malicious, it is notable given its proximity to “Chenlun” phishing activity and the phishing actor’s stated preference for SMS phishing lures.
A Profitable Niche in the Global Phishing Market is Reason for Concern and Watchfulness
The phishing economy is notoriously–probably impossibly–difficult to conquer. Phishing kits are easily stolen, modified, and shared by other threat actors attempting to capitalize on a kit’s success. Even phishing operations like the now-defunct 16Shop that tried to license and encrypt their phishing kits ultimately ceded significant ground to upstarts borrowing heavily from cracked versions of their phishing kits. And those phishing operations soon faced the same problem: phishing kits are easy to create and procure but astonishingly difficult to perfect. While the “Chenlun” phishing actor uses centralized management infrastructure which gives them a modicum of control over their phishing campaigns and customers, creating a competing service would pose few technical challenges if suitable lure delivery infrastructure were available. In phishing, the only constant is the steady drip of change.
DomainTools continues to keep a watchful eye on USPS package redelivery phishes, especially those associated with “Chenlun.” But having a positive impact and making the Internet a better, safer place from cybercrime requires vigilance. DomainTools remains ever curious about who the next 16Shop and “Chenlun” rising through the ranks will be.
Conclusion
During this holiday season, SMS-based phishing messages pretending to be from the USPS can wreak havoc with people’s celebrations and gift giving. As first reported by others, DomainTools continues to track the “Chenlun” threat actor and the phishing kits they use. The kits themselves are generally well-constructed, with configuration files to limit access to specific counties and dedicated Telegram channels to receive stolen data. Other indicators, such as website titles, provide for meaningful pivots to identify additional domains and Whois information to track the full scope of activity from this actor.
We recommend people be skeptical of all SMS messages related to package delivery. This is especially true if the message asks for additional payment information. Many vendors provide different ways to track packages through dedicated apps or websites. The US Postal Service itself provides an “Informed Delivery” service where you, as a US resident, can get information from them directly for all physical mail and package delivery that you can expect on any given day.
We ask that you tell your family, friends, and neighbors to be watchful for USPS phishing attempts. Family and community is what the holiday season is all about, and protecting someone from fraudsters is without question a lasting gift.

