Coming up this week on Breaking Badness. Today we discuss: Wrinkles in Time, A Payday Drone, and Two Truths and a Lie.
Here are a few highlights from each article we discussed:
Wrinkles in Time
- This article from the New Yorker discusses an obscure software system that synchronizes the network’s clocks. We assume it will always work, but will it?
- Kelly has done some things in her career that aren’t exactly “glamorous,” but have enhanced the function of the Internet and NTP is one of those things that is truly fundamental to the foundations of the Internet. It makes the Internet work. Most people don’t even know it exists
- It’s kind of like DNS where you don’t think about it until it’s broken
- Many people assume computers just work, but David Mills observed this problem we’re discussing
- David Mills went to work for a company called COMSAT and was one of the contractors to develop ARPANET.
- He found that clocks in a power grid fluctuate due to temperature changes on the order of seconds every day
- When it’s hotter, the clocks when faster, when it’s cooler the clocks slow down
- That meant it was challenging for that system to keep a consistent clock. He started tinkering with how to even out that time on the ARPANET. Some networks keep reliable time and some do not - they’re compared to the reference, which is the atomic clock used to keep average time (the values of various atomic clocks around the world are averaged to create the reference time which we call Universal Coordinated Time - UTC)
- The software Mills wrote to distinguish reliable and unreliable time keepers became NTP which stands for Network Time Protocol
- This article mentions that we take global time synchronization for granted, but we had some panic around this concept at the beginning of the millennium with Y2K. In your opinion, why do you think attitudes have shifted back to complacency?
- Well Y2K is a calendar problem, whereas NTP is a time problem - and those are related, but still separate, but it got people thinking about it
- It was decided that it was an issue, and it should be addressed, but it really hasn’t been addressed
- There’s no market segment for time, so there’s no incentive for a company to come in and run NTP - you’re not going to get rich synchronizing the computers of the world to UTC
- It’s always been there, people are accustomed to it being there and assume it always will be there, and they don’t think about how it got there
- NTP is largely the work of David Mills and his partner, Harlen Stenn - they’ve done all the work and have written most of the code - it’s not a widely distributed thing like Linux
- How does NTP work?
- NTP syncs participating computers or clients - you can think of it as a client and server model within milliseconds of UTC
- One of the reasons it came about was to correct latency in the network
- Another function it has now, but didn’t have originally (and boy, we would miss it if it were gone) is its the basis for cryptography - if you don’t have time, you can’t encrypt things
- NTP evaluates and categorizes nodes as being more or less accurate timekeepers and it de-emphasizes less accurate timekeepers and emphasizes the contributions of more accurate timekeepers
- Most servers will calibrate their time daily and listen for updates that it gets from the main NTP servers
- If this sounds like a complex undertaking - it is. And the fact that it works at scale is nothing short of astonishing
- Vince Cerf, who is known as one of the fathers of the Internet, looked at this code and called it “wizardry.” It really is kind of magic - from the true Father Time - David Mills
- Its maintenance is handled by people who are not paid - why is funding so hard especially when it’s so integral to the Internet?
- NTP is trying to bootstrap itself into a foundation - called the Network Time Foundation and they currently bring in just a few hundred thousand dollars a year, which pays their server costs, basically. It doesn’t begin to cover the costs to extend and perpetuate NTP as a service that’s freely available to the Internet
- There are other things on the Internet that work like this - last week Kelly was at a conference and met the creator of the public suffix list. He discussed that he put all this unpaid work into this and the public suffix list is used by Mozilla, Cloudflare, Google Chrome, etc. These huge companies use this as a reference as to what the list of effective TLDs is, and they don’t pay for it - it’s just this guy who’s doing this. So what happens if he can no longer do this?
- There’s a metric called the “hit by a bus” factor, which is the idea of, what would happen if this guy got hit by a bus? The thing is, for the public suffix list and NTP, if David Mills and Harlen Stenn got hit by a bus, it would be catastrophic for all of us. They have the institutional memory of time
- People think of this like “free beer” as an example. Which is, someone buys you a beer and you don’t have to think about how that was paid for or where it came from - it’s just here. It’s the same for open-source technology - you don’t motivate people to pay for it
- What do you see in the next 5 years for NTP given the prevalence of the Internet of Things (IoT)?
- Kelly believes NTP will endure - the install base is too large and there’s apprehension of giving this over to a private company
- She noted that a large proportion of computers that run NTP run version 3 (the current version is version 4) - people are going to be reluctant to deviate from what works
- Google can try to create their own, but she doubts it will get a lot of traction
A Payday Drone
- The concept of consumer drones used for hacking has been discussed over the past decade, and now we’re seeing these sorts of attacks actually take place
- This popped up on Twitter sometime last week. It was relayed to Greg Linnares, a security researcher, about drones finding employee MAC addresses and use drones to gain physical access to the network and then breach
- The Register spoke to someone (off the record) from that company about drones being used in this way
- What they noticed was an employee was logged into two spots at the same time. One being their house (a few miles away) and the other spot was on-site
- They used WiFi sniffer devices to find where the signal was coming from and it led them to the roof where they found two drones
- One looked like it crash landed, but the other one looked operational
- The Phantom drone was carrying a modified Pineapple device, which if you’ve attended a conference, it’s a tricked out router so you can listen to signals or spoof signals and get folks to hop onto it
- So you have one drone to do the WiFi sniffing and the other does the malicious bidding once you have the employee’s MAC address
- They were caught editing the internal Confluence page for this organization
- But it sounds like the organization caught this early on before anything too malicious occurred
- We don’t know who was behind this at this time
- We have to take everything here with a grain of salt - it being reported on Twitter for one
- It is within the realm of possibility and if it actually were to occur, this is probably how it would happen
- How paranoid should we be about drones and roofs?
- This is something that needs to be taken into the threat model for organizations
- It could be as simple as throwing a camera on the roof
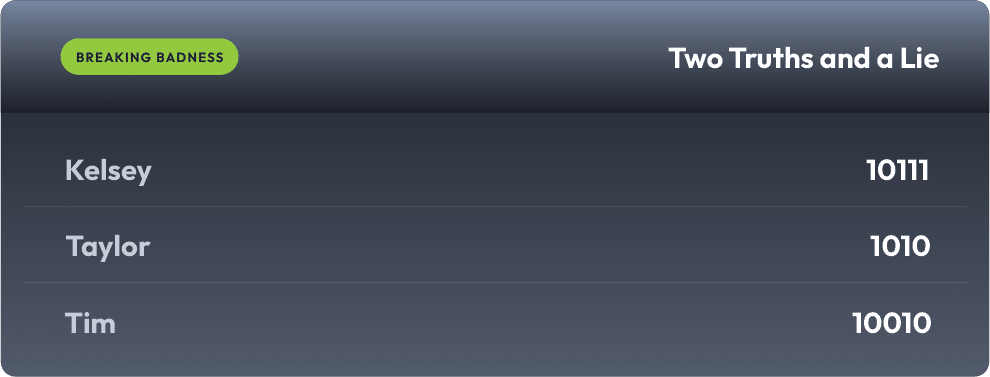
Two Truths and a Lie
Introducing our newest segment on Breaking Badness. We are going to play a game you are all likely familiar with called two truths and a lie, with a fun twist. Each week, one us with come prepared with three article titles, two of which are real, and one is, you guessed it, A LIE.
You'll have to tune in to find out!
Current Scoreboard
This Week’s Hoodie/Goodie Scale
Wrinkles in Time
[Kelly]: 10/10 Hoodies
[Taylor]: 10/10 Hoodies
A Payday Drone
[Kelly]: 3/10 Hoodies
[Taylor]: 2.5/10 Hoodies
That’s about all we have for this week, you can find us on Twitter @domaintools, all of the articles mentioned in our podcast will always be included on our podcast recap. Catch us Wednesdays at 9 AM Pacific time when we publish our next podcast and blog.
*A special thanks to John Roderick for our incredible podcast music!

