Coming up this week on Breaking Badness. Today we discuss: Threat Actors Go On A Supply Chain Attack PHP, BazarCall Me Maybe, and our fun new game, two truths and a lie.
Here are a few highlights from each article we discussed:
Threat Actors Go On A Supply Chain Attack PHP
- On March 28th, 2021, members of the PHP project noticed two malicious commits from Nikita Popov and Rasmus Lerdorf. Both of whom say their individual git accounts were not compromised. Since PHP manages—or rather managed—their own git repository on their own servers this points to the server itself being compromised as otherwise it would be difficult to check in commits as those users.
- Commits are version control systems are pieces of software, git for example, that keep track of all the changes to a code base. When you make a change as a developer you commit that change to the repository so that everyone can grab the changes. Repositories then keep track of every change that has ever been made so that if a mistake is made you can find out who added in that mistake and roll back the changes one at a time until you get to a working state for the software. It’s a collaboration tool essentially to allow hundreds of people to work on a single project.
- The infamous line 370 (or the malicious commit) would allow someone to inject code using just an HTTP header. The reason for that is it evaluates the string sent to it so you could potentially put whatever you want in there. This could have been disastrous if it had been released.
- In terms of repercussions if this malicious code was fully committed, nearly 80% of the world’s websites that run PHP—assuming admins updated which I guess, uhhh, thankfully PHP admins aren’t known for—would be vulnerable to a situation where attackers could just send a malicious header when connecting to the website and the server would run whatever they sent. This would be extremely easy to take over a server then. We’re super lucky this didn’t just sneak by and that the people on the PHP mailing list were paying attention.
- I think SolarWinds has brought it back en vogue you know. These things all have their seasons and right now this is where attackers are concentrating because it allows them to circumvent a bunch of new detections out there that spot anomalies and what not. We’ve got a situation where a lot of that developer-minded stuff is pretty loose. You’ve got packages from repositories like NPM and PIP just implicitly trusted, you’ve got a lot of trust in vendors that’re using those packages, and you’ve got a lot of high profile things that get no eyes on them in the network because they’re just a part of doing business. This makes them juicy targets. I think from this we’ll see a lot to do with verifying code, packages, and what not again. There’s a reason signed commits exist and it’s because this has all happened before, will happen again, and it just takes making the abstractions we use to implement these things a bit more seamless for developers.
BazarCall Me Maybe
- As you mentioned, this is a piece of malware that targets Windows systems. It’s a first stage loader in the form of a maldoc that I’ll describe in a moment, which then calls out to later stage loaders that in turn will pull down various kinds of nasty, including some of the usual suspects out there like TrickBot, IcedID, Gozi, and others too.
- With a traditional phishing email, once you send it, as the attacker you sort of hope for the best, right? It’s the UDP of attack techniques: spray and pray. Fire and forget. You have no control over what the human does once you’ve sent it. But with this method, you have a chance to interact with the target, and you have a chance to use your winning personality to convince them that you’re for real and that you’re here to serve them.
- The lure here is that you have a free trial to some service that is about to end. The psychology of it is clever, because it appeals to the “opt out” mentality. If you receive this email, you can’t really recall starting the trial (since you never did, of course) but the one thing you know is that you want that thing canceled before your credit card gets dinged. So you call the number. The friendly and cheerful call center operator asks you for your unique customer ID from the email, and it’s off to the races.
- The winning and cheerful customer service operator directs you to a website, which has a very of-the-moment-looking front end, where you’re prompted to enter that customer ID.
- When you’re trying to cancel an online subscription, of course: an Excel document. I jest, of course. Who would actually expect that? Here is where the call center people have to earn their pay. They have to convince you not just to download this Excel file, but also to (you knew this was coming, right?) enable macros, and maybe disable antivirus while you’re at it, because of course you want nothing to stand between you and the cancelation of that payment. So if they succeed with their social engineering and you download this document and duly enable macros, it then swiftly calls out to a loader which opens the pipe to a bunch of additional malware. So, you see, this is the TCP of malware lures: there’s a handshake of sorts, and a confirmation of the connection. Good stuff.
- It looks like this was brought to you by your pals at TrickBot, and it’s another -aas. Not a donkey, but in this case it’s distribution as a service. They can boast some famous clients, too, like the UNC1878 group, which Randy believes is a customer of this service. (UNC 1878, in case you haven’t memorized every actor group yet, is a group that FireEye identified about a year ago, and they seem to operate a lot of TrickBot, Ryuk, Maze, and other ransomware. They like healthcare facilities, charmers that they are. UNC means un-categorized, so if you’re wondering where they are based, you’ll have to just keep on wondering.
- This is a tricky one for detection mechanisms to trigger on, and samples aren’t making their way to the likes of VirusTotal. Also, the service is being run, unfortunately, pretty competently. They’re constantly changing up their infrastructure (in this case, phone numbers are one of the things they keep changing) to avoid detection. I wish they were worse at their jobs, frankly.
- The distribution mechanism is clever, and preying on people’s aversion to something (like getting charged for something they don’t want) rather than trying to convince them in an email that they should opt in to something, is paying off. On the other hand, you have to think that being asked to download an Excel spreadsheet, and then—this is the whopper—to enable macros, is a HUGE tell. Yes, there are obviously folks who aren’t infosec savvy that won’t recognize how sketchy this is, but I think they probably have a decent rate of attrition once they get to that stage of the call. Time will tell.
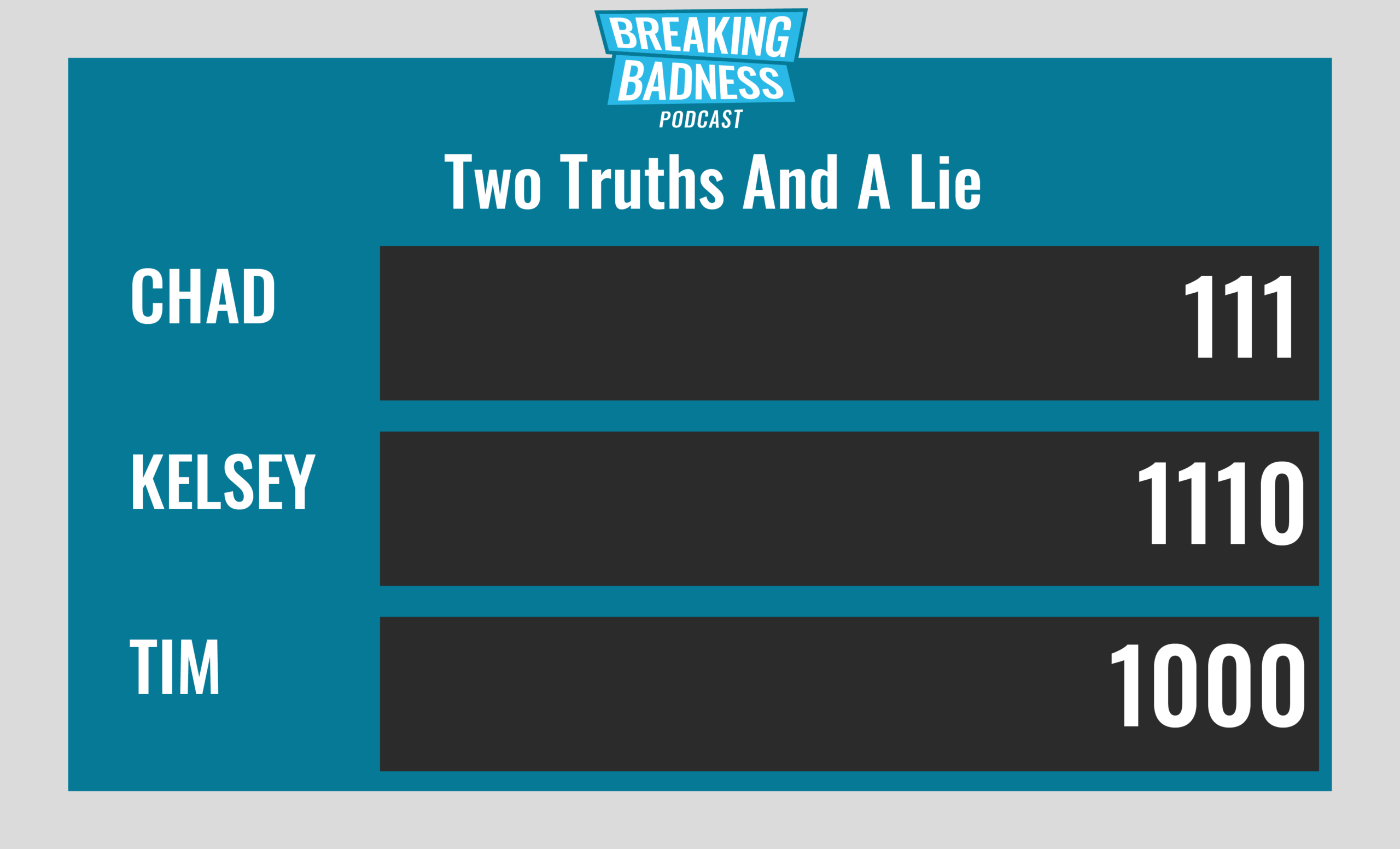
Two Truths and a Lie
Introducing our newest segment on Breaking Badness. We are going to play a game you are all likely familiar with called two truths and a lie, with a fun twist. Each week, one us with come prepared with three article titles, two of which are real, and one is, you guessed it, A LIE.
You’ll have to tune in to find out!
Current Scoreboard
This Week’s Hoodie/Goodie Scale
Threat Actors Go On A Supply Chain Attack PHP
[Chad]: 9/10 Hoodies
[Tim]: 10/10 Hoodies
BazarCall Me Maybe
[Chad]: 4/10 Hoodies
[Tim]: 4/10 Hoodies
That’s about all we have for this week, you can find us on Twitter @domaintools, all of the articles mentioned in our podcast will always be included on our podcast recap. Catch us Wednesdays at 9 AM Pacific time when we publish our next podcast and blog.
*A special thanks to John Roderick for our incredible podcast music!

