Coming up this week on Breaking Badness. Today we discuss: Chaos Strikes Back, BEC is a Scam Dunk, and our fun new game, two truths and a lie.
Here are a few highlights from each article we discussed:
Chaos Strikes Back
- ChaosDB is the name for a Microsoft Azure Cosmos DB cloud vulnerability found by the folks at Wiz. These are the same folks, who a few weeks back, brought us that interesting cloud DNS cross-account vulnerability that allowed anyone to take over a zone they didn’t own essentially. Their research team has been doing a lot of interesting cloud security research and are building up this cloud vulnerability community.
- Cosmos DB is Microsoft’s answer to hosted Cassandra basically. It’s a NoSQL data store, scales infinitely, all the blah blah blah cloud promises. Anyways, interacting with that data can be done through Jupyter Notebooks. Jupyter Lab is this environment for writing and documenting the code you’re working on, we use them a lot in the research world as kind of sandbox environments. You create notebooks which can then be rerun and it’s a very useful way to work with huge data stores and share your work. We’re big fans here at DomainTools and I even have a host of my personal notebooks up on GitHub, it’s great, it’s industry standard. That said there was a vulnerability in Microsoft’s hosted Jupyter Notebooks implementation that sat on top of CosmosDB that allows an attacker to go from one of their notebooks, to a victim’s notebook instance, to then full admin rights on the victim’s databases. Every Cosmos DB user was affected so this is thousands of organizations.
- They discovered the vulnerability in August, but it had been a problem for months beforehand. Microsoft has since disabled the feature but literally every single Cosmos DB user was affected. If you have Cosmos DB in your environment it’s time to rotate some keys and assume you’ve been compromised.
- Microsoft fixed the issue by disabling the feature, but only communicated out to 30% of the potential victims according to Wiz. This is an interesting space and something that’s been being discussed in the cloud security research community about whether or not these vulnerabilities need to have some sort of CVE-like structure. CVEs work for traditional application vulnerabilities because the version remains and is vulnerable, but for these managed service offerings Microsoft or Amazon or whoever updates their service and the vulnerability becomes largely irrelevant. I think companies then think “oh it’s fixed, nothing to see here, move along” and that it’s over.
- If you use CosmosDB you’re affected so rotate your keys. This provided anyone access to your full CosmosDB instance with full administrative rights. That could’ve been leveraged any number of ways. It doesn’t look like this was exploited before, but you have to assume that you’re affected when it’s something this trivial to exploit. It’s a big deal.
BEC is a Scam Dunk
- This little town in bucolic and booze-tax-free New Hampshire became the victim of a so-called business email compromise attack, to the tune of $2.3 million in a number of separate but undoubtedly related events. The first one they noticed was a payment to a local school district – that one was for $1.2 million—that did not go through. Or rather, it half went through: the money left the town’s bank, but it never made it into the school district’s. Then it turned out that there were a couple of others that involved a construction contractor. Same deal…the train left the first station, never arrived at the second, so to speak.
- Let’s brush up on BEC (business email compromise), let’s go full taxonomy here. First you got your social engineering in general…manipulating humans rather than manipulating machines. Then you got your phishing. I can’t imagine that there’s anyone listening to Breaking Badness who is not familiar with your phishing. Then you got a species of phish that’s known as your Business Email Compromise. That’s where you use phishing – often in combination with other techniques including phone conversations, text messages, what have you; anyway, you use these methods to get your victim to make a funds transfer into what they think is a legitimate account, but instead they are paying the criminal. In the case of the charming and ideally-situated Peterborough, the lure was that the criminals were posing as these accounts payable recipients—the school district and the contractor. Another way that BEC often goes down is that the criminal poses as a corporate executive and asks a subordinate to make a wire transfer at their behest—usually in a hurry. So there you have it.
- On Jul 26, 2021, the date that the town select board (basically the town council) discovered the fraud related to the school board. They did the right things for the aftermath of discovering this kind of fraud, putting a hold on the transfer, though that was too late, and getting in touch with the Secret Service. Not the bulletproof vest ones, the ones who are more obviously part of the Treasury Department. So then on August 18th they learned of the transfers to the faux contractor. And on the 23rd, they issued a press release describing the scheme.
- There isn’t any information at this point on who carried out this attack, but the smart money says it’s criminals who are responsible. In the fullness of time we may find out more about who specifically defrauded the verdant and lively community.They certainly can expect to investigate because they already are. As to recovering the funds….in the sense of clawing them back from the criminals, while that’s not absolutely impossible, it’s pretty rare. There’s a higher chance that they’ll get at least some relief in the form of insurance coverage, but they don’t yet know about that either. Cyber fraud insurance is certainly a thing, and it’s probably a good industry to invest in if you are into that sort of thing.
- Since they don’t yet know whether or to what extent this historic and scenic community will be made financially whole after these thefts, it’s hard to know. Of course it will embolden other criminals looking to pull of BEC’s against municipalities, and it is certainly being studied by those cyber insurance actuaries. And even though this is not the R-word, there are some parallels in terms of the recovery phase after the event and what kinds of legislative or policy or best practices changes might come along.
- Every single person is vulnerable to social engineering. In fact, anyone who thinks they cannot be socially engineered is probably more likely to fall victim to it than a person who acknowledges that it can be pretty darned hard to tell sometimes whether something is legitimate or not. And notice that in these attacks, no electronic systems were hacked…it was just the humans. So the role of the defender becomes things like user education (which I emphatically support) and maybe to some extent making sure that the email filtering is as good as possible – we don’t know exactly how the emails were structured in this attack, but if they did something like use a spoof domain to look like the sender was coming from a trusted entity, then some email systems do have ways to discover and block those. But if you pull back a bit from what we strictly think of as defenders, there are things like policies you can put in place to defend against these. For example, if it’s the CEO version of this, you could have a situation where you make sure every employee who is empowered to make wire transfers has the CEO’s cell phone number, and calls them before making any transfers (or if they’re one of these weird places where people work in an “office,” they might even stroll over to that person’s office and ask in person.
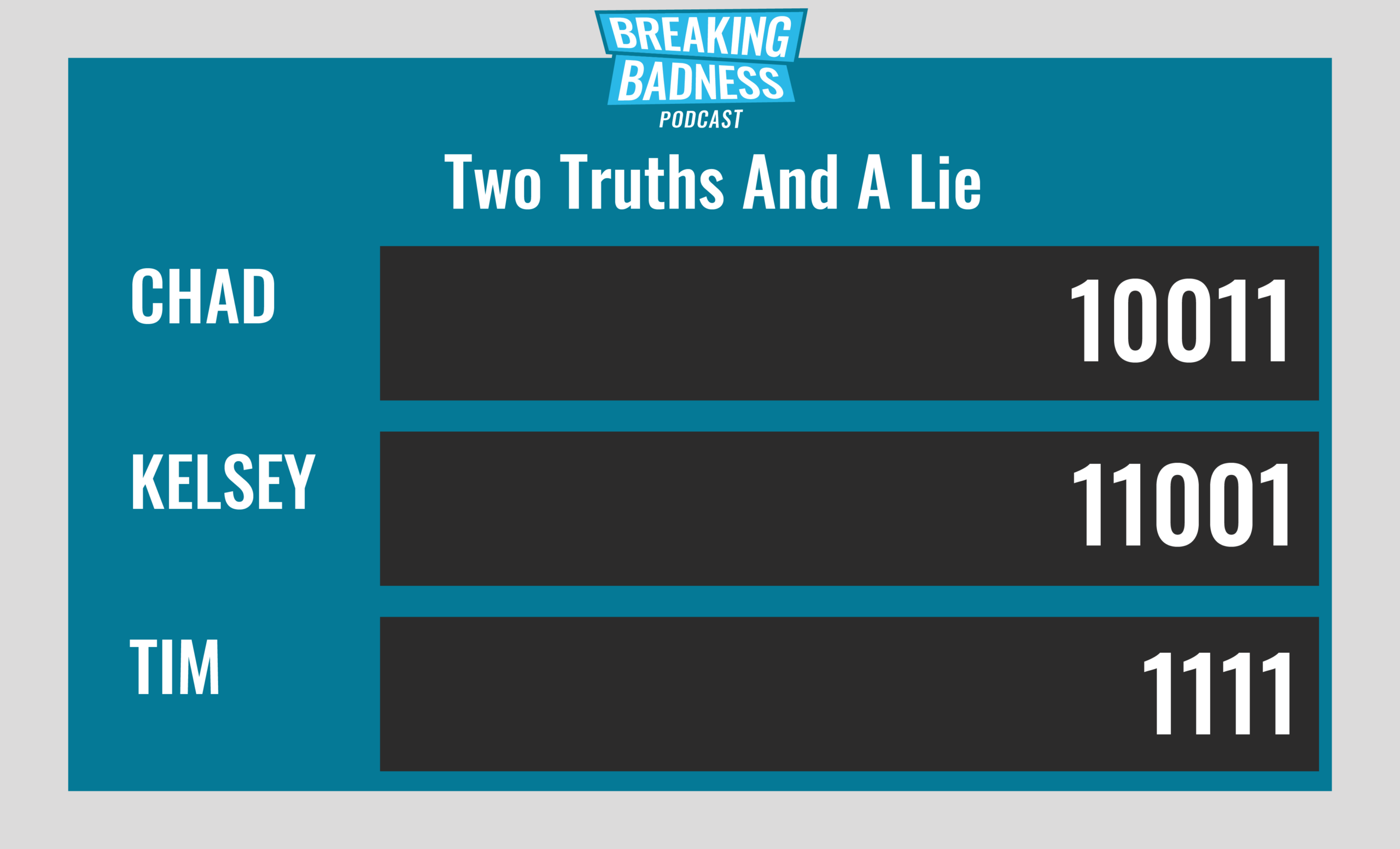
Two Truths and a Lie
Introducing our newest segment on Breaking Badness. We are going to play a game you are all likely familiar with called two truths and a lie, with a fun twist. Each week, one us with come prepared with three article titles, two of which are real, and one is, you guessed it, A LIE.
You’ll have to tune in to find out!
Current Scoreboard
This Week’s Hoodie/Goodie Scale
Chaos Strikes Back
[Chad]: 7/10 Hoodies
[Tim]: 9.1/10 Hoodies
BEC is a Scam Dunk
[Chad]: 9/10 Hoodies
[Tim]: 8/10 Hoodies
That’s about all we have for this week, you can find us on Twitter @domaintools, all of the articles mentioned in our podcast will always be included on our podcast recap. Catch us Wednesdays at 9 AM Pacific time when we publish our next podcast and blog.
*A special thanks to John Roderick for our incredible podcast music!

