Iris Investigate Brand Protection
For your convenience, we’ve included the video transcription below
Greetings and welcome to the use case overview for Brand Protection with DomainTools Iris. When it comes to leveraging domain registration data for brand protection, we can sort the malicious domains that we come across into two broad buckets. One is domains that are targeting external users, these may be domains that are looking to capitalize on our brand to target our customer relationships, so they could be used for credential harvesting.
Leveraging Domain Data for Brand Protection
So think of the endless number of fake Netflix login pages or Comcast login pages targeting users right now. They may be looking to use these domains for payment skimming so the Magecart group in particular has look-alike domains when they are breaking into your e-commerce pages. They are going to use it to sell counterfeit goods, they may be used to drop ransomware onto a system. These domains are targeting external users and could also be targeting our business relationships, so you may be a part of the long tail vendor chain for someone for the way they are utilizing your brand for business email compromise phishing, wire fraud or to gain initial access or to gain lateral movement, once they have that initial access through lateral spearphishing. We also have domains that are targeting our internal users, these are also going to be used for credential phishing, they could be targeting your vendor relationships, so they could use say your identity access management or a single sign on providers in conjunction with your brand to target your internal end users, internal end users, your office suites, your cloud providers. Those different vendor relationships you have are ripe for abuse, same for business email compromise phishing, they could be utilizing your brand just to get wire fraud directly from you or to gain initial access ahead of a data breach or planting ransomware across your network.
Domains Targeting External & Internal Users
Now when it comes to the remediation cycle for these, for domains that are targeting external users we want to discover those, investigate, monitor, and then initiate a takedown. Sometimes this process will happen very quickly or sometimes you may do the model and have to keep an eye on them for a longer period of time. For domains that are targeting your internal users, that cycles very similar but you do have an option to block, so when you discover you can block and you can also block after you have investigated if you find additional domains that could be used to target you across malicious actor infrastructure, you can block those as well.
Brand Protection with Iris: Discovery Options
Now that discovery phase is really important, Iris can help in a lot of different ways, for here knowing is half the battle. The easiest ones are going to be things like hey domains that begin with our brand, or contain our brand or end with our brand, just in the domain name string itself, you are going to find a lot there, if you have got a popular brand.
Passive DNS
Looking in Passive DNS and utilizing your brand in wild card searching to see if you are being utilized in any subdomain activity. In this case we are hunting for bank login but we picked up Chase, a domain that is spoofing Chase as well here so that long URL there could be used to trick a user, right they might not see that it’s out of a dot cf so if they’re on a mobile device that can be tricky to see the full URL. But hunting for Passive DNS here you can find all of the different registered domains that are utilizing your brand as a subdomain and then export them into the Iris Pivot Engine.
Google Analytics
We can also do discovery via Google Analytics codes, these trackers are used on your site to take a look at the traffic that there getting but there often picked up when bad guys are looking to scrap your login page they’ll pull those in almost on accident f they are very lazy they will just leave those up and when we go hunting for those in the wild we will just pick those up.
So here we can see we have 170 domains or so that are utilizing the JP Morgan analytics tracker code. If we get a better look at those, we can see clearly that a lot of these have nothing to do with JP Morgan, the one on top there we’re observing on a blocklist today, that’s why we see that Risk Score of 100. The other ones below there that have a little broken paper clip next to them, tell us that these are inactive domains, so they are either older domains that were owned by JP at some point in the past or they’ve infringed them and taken them down.
Whois
Within Iris the data set, we have got a lot of other discovery options that are available, our Whois data is that we pull we’re getting itless frequently but certainly some registrars are still passing us that data, so looking for maybe your street address or your phone number within those registrations can be very helpful.
SSL
Looking in the SSL certs that we are pulling in to find the subjects that it might contain either your full brand name or a partial matches can be helpful. Same for hunting in SOA records, looking where folks might spoofing for your domain name there as well, looking at mail servers that might contain your domain name or your brand name rather or the SSL org also another way to go hunting for your particular brand within our data set.
You know when we are doing these types of broader hunts, it can be helpful up front to tag our own infrastructure, so run an investigation across all of your own infrastructure and then give that a tag, we can then take that tag and filter that out when we are doing our searching for potential infringing domains out in the wild. So, we are always filtering out the noise that might be our own registered domains.
Iris Investigation Walkthrough
Now we’ll run through a sample investigation targeting brand protection here inside of Iris. This particular investigation starts with a Japanese shipping and logistics company, Sagawa. We picked up hundreds of spoofing registrations occurring over, starting in late 2018 and going on through 2019. They were leveraging this brand, they were sending out SMS messages to end users saying hey your package was unable to be delivered. You can go here and download an application to track the package in real-time. So, this is the landing page of one of those sites that are under an effort to get someone to grab that APK onto their device. Once that APK is on their device it starts to hunt for their banking login information and it starts redirecting users who are trying to go to their bank login page to the spoofed sites here. So, here’s a quick collection of the screen shots that we pulled from some of the spoofing sites ofthe banking providers us there. Very convincing. Now this is at scale, we picked up thousands of registrations if we combined this with the Sagawa domains between 2018-2019 again targeting Rakuten, Softbank, DoCoMo, KDDI and Yahoo. The Yahoo ones in particular are also very convincing, trying to pull those credentials.
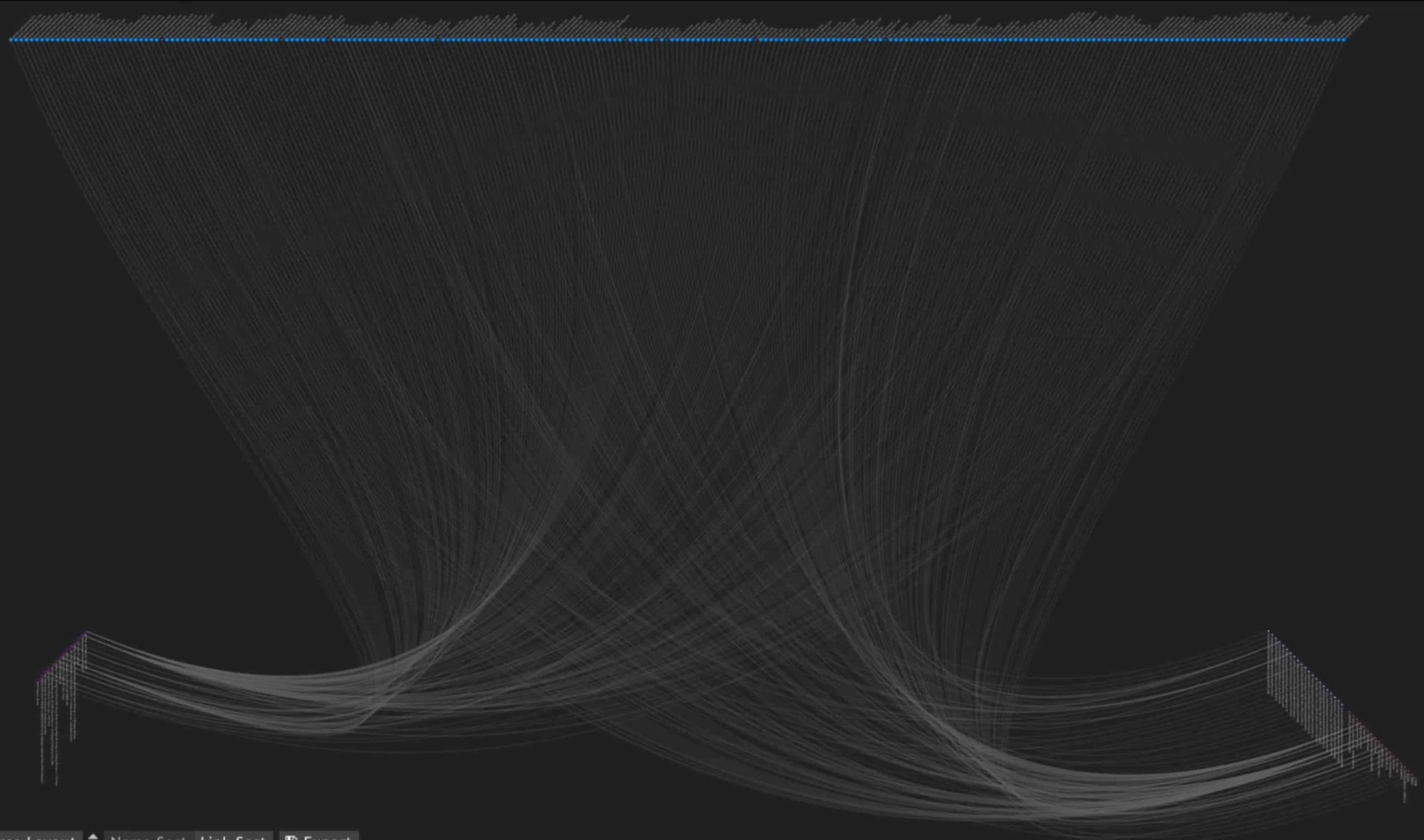
Iris Pivots
Now when we explore these domains within the Iris data set, we have a lot of options at our disposable for pivoting right, so right away for yahoo-accounts[.]com. The 100 lets us know that it’s on a blocklist, that IP address there is highlighted, letting us know that that’s going to be helpful for us but we’re pulling in names server data, registrar data, contact data the SLA records or Whois if we can get those SSL certificates, analytics codes, redirects, mail server, SPF info, all that data can useful in an investigation in particular in this investigation here. If we were to look for an IPV4 and take a look at the other domains that are hosted there by expanding here, we’ll see that hey it’s not just yahoo-accounts but it’s a large collection of Yahoo, Softbank, Rakuten, Docomo all kind of cohabiting that same IPV4 address. Over the course of this particular investigation we were able to expand and pivot to bring these things in, but we’re also looking at things like registrant orgs. So here we see ones that are tied to a couple 100 registrations within our data set. Getting a better look at those and tell us hey those are also connected to our starting point. Not only do we see Yahoo, Rakuten, Apple but also the more generic support-039.info. Those are probably targeting other brands at the subdomain level, we can go hunting for that back in our Passive DNS data Pane.
Contact street addresses can also allow us to pivot us across the data that are connected to those same for email addresses. We run historical matches against our entire 20 year database pulling this database so we can find any older activity that might be tied to these registration details as well. Things like phone numbers, IPV4s, SSL certificates, all came in handy in this particular investigation and we ended up with like I said nearly 2,000 total domains that might be connected to various bits of infrastructure, registration details and web content that we pull into Iris. Once we have these larger lists it’s time to start thinking about blocking and tackling right. So when we found a bunch of adversary infrastructure in the wild, there are lots of different ways to get that out of Iris, primarily we can very quickly highlight all those domains and then copy them to our pasteboard so we can get them where we need to go. We also have the option to download the entire Pivot Engine via CSV or Stix 1.2, 2.0. and XML or JSON for the end users who need that out there.
Monitoring
And when it comes to monitoring them, Iris Pivot Engine is getting updated daily, so we are, you know, we are pulling in frequent pulls for Whois hosting infrastructure, mail server records as in SSL certificates. Changes across all of that could be clearly instrumental is saying hey now this was parked now its become active. Now you can pull screenshots and use that in our evidence as well. Now when it comes to remediation that kind of thing can be really helpful.
Takeaways about Takedowns
So some quick takeaways about takedowns. Your resolution time frames are going to vary wildly and the options at your disposal vary wildly based on the TLD space domain, based on the registrar, or the hosting provider, but regardless the one thing that you are going to need is data. That data can be found inside of our Iris platform. Maybe it’s the Whois abuse contact data, maybe it’s the infrastructure abuse contact data. But it can also take the form of historical screenshots, historical Whois data, or infrastructure observation details we’ve made either in the Pivot Engine or with the Passive DNS data. MX records also very helpful here. This is all going to help you when it comes to that takedown process when you are working with brand protection inside the Iris data set.