Digital Threat Intelligence Proactively Protects Your Data From Internet-Based Threats
Enjoy a guest blog written by David Monahan as a supplement to his published work “EMA Radar for Digital Threat Intelligence Management: Q4 2017”.
*The following blog solely represents the views of David Monahan
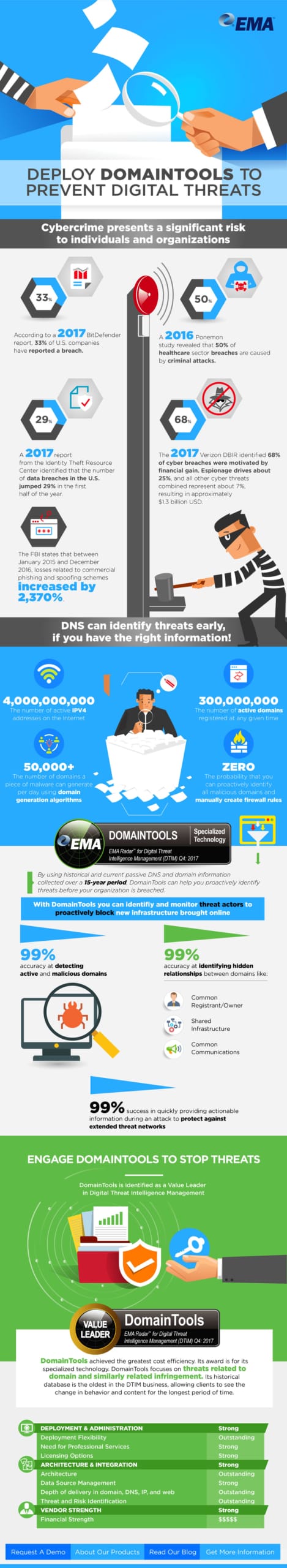
Data breaches have two primary drivers. Sixty-eight percent are driven by financial gain, twenty-five percent are motivated by espionage, and seven percent are motivated by other reasons like sociopolitical statements or revenge. One thing that 100 percent of all large-scale or otherwise orchestrated attacks have in common is the need for command and control infrastructure. Threat actors originating from organized crime, rogue hackers, and nation-states are creating new domains at a breakneck pace. A single piece of malware can use domain generation algorithms to create more than 50,000 domains a day to protect its command control network.
All of this activity falls directly into the purview of digital threat intelligence management (DTIM) solutions. DTIM is a specific term for the evolution of technologies that started out as threat intelligence feeds of the early 2000s, and then morphed into threat intelligence platforms. Threat feeds were volumes of information contributed and collected throughout the common Internet about potentially threatening activities. Feeds were fraught with problems and were a caveat emptor situation. The information had virtually no quality control, so duplication of events was a huge problem. Events did not age over time, so much of the data became stale. There was no prioritization, filtering, or analysis of the data before it was sent to or picked up by the recipient. All of these issues formed massive data dumps that only large organizations with the budgets and manpower to perform data parsing and analysis could use.
Threat intelligence platforms were the natural next step. The vendors in this space saw the problems from data feeds. Concerned researchers, security professionals, and forward-thinking entrepreneurs collaborated to deliver better threat warning data. They recognized the operational difficulties of processing the data, so they created the platforms to deduplicate, filter, prioritize, and age out data. Doing so brought the data down to a much more manageable volume using commonly available processing and storage. The vendors also incorporated user interfaces for searching and analysis. This huge change meant operations gained the ability to better interact with the threat data and were no longer dependent on scaling their SIEMs to use the data.
With improved analysis algorithms and the elasticity of the cloud, DTIM expanded the monitored content and took advantage of advances in data analysis and user interface design. With these improvements, DTIM now delivers only the purest distilled information as actionable results to analysts. DTIM also provides the opportunity to identify and stop data theft much earlier in the lifecycle. After a breach, the gap between the theft and detection is the most significant issue. In 98 percent of the cases, the compromise and theft take only minutes, while theft discovery takes weeks to months. To add insult to injury, the majority of thefts are not identified internally but by third parties, who then notify the victims that their information is out in the web somewhere. Forward-thinking organizations that aggressively seek to close that gap are investing in DTIM to reduce the opportunity for attack by identifying malicious infrastructure faster and then blocking it from interacting with the organization.
Companies like DomainTools are delivering proprietary technology to hunt for and identify pertinent information online. In the 2018 Enterprise Management Associates “DTIM Radar Report™” DomainTools achieved the coveted Value Leader award. This award was presented based on DomainTools’ cost efficiency compared to other vendors in the space. It was the farthest right in the Value Leaders category for deployment cost efficiency. Some of the other ratings it received to support the Value Leader were:
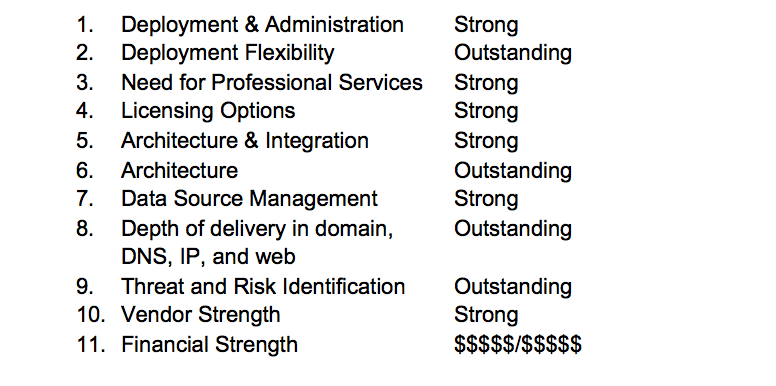
It also was given an award for its specialized technology. DomainTools focuses on threats related to IP addresses, hosts, domain, and similarly related infringement. Its historical database is the oldest and most complete in the DTIM sector, allowing clients to see the change in behavior and content for the longest period of time. No one is immune to Internet-based threats and fraud. The larger your organization’s Internet presence is, and the more it is relied upon for business revenue and growth, the more you should consider how you are going to proactively protect it.
Below is a quick look at data featured in the full report: