DomainTools 101: DNS Shadow Hack-Attacked
In this article we will dive into the attack vector known as domain shadowing, and how it can land an innocent blog on a blocklist of known bad domains. A domain shadowing attack begins when the credentials that are used to setup and maintain your domain have been compromised. Once a malicious user has access to your DNS account they will then begin to set up new sub domains off of your root domain. This is especially hard to detect for a few reasons:
- Attackers don’t need to have access to your web server.
- Even if you are notified and search on your server, you won’t find anything because the new subdomain that they set up is being hosted someplace completely different, trading on the reputation of the root domain to peddle malware to unsuspecting visitors.
In this example I’m going to share details that will illustrate the aftermath of the attack, and how DomainTools can be used to unearth this type of cyber assault.
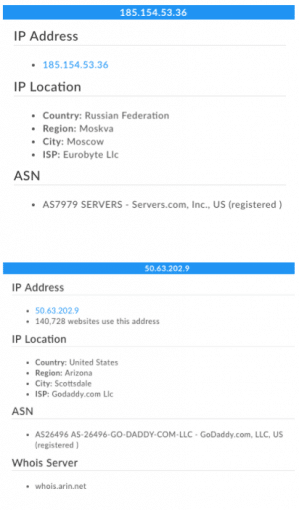
I was looking for some good examples of this particular type of exploit, so I searched on twitter for #rigek, which is one way security responders share information about ongoing attacks. This one is specific report out of over 40,000 sites that were compromised and using the RIG exploit kit. It was reported that the RIGEK was being hosted on the following url: new[.]60windowsin60days[.]com. To begin my investigation, I started by copying and pasting the url into DomainTools Iris Investigate. I was able to learn that this domain was registered and owned by Susan Pace at WJW Fox8 with the email address of susan.pace[@]fox8[.]com. A quick peek into the Passive DNS tab of Iris Investigate with this url uncovered a subdomain that is pointed at a server in Russia. This seemed rather odd, considering Fox8 is based out of Cleveland, Ohio. Next, I wanted to see where their root domain was being hosted, so I did some research in Iris Investigate and learned that it is being hosted in Scottsdale, Arizona.
In this recent article from Threatpost, we can see that this was a very targeted attack on users who have used GoDaddy and as the primary domain registrar. They found over 40,000 of these subdomains that have been compromised.
I wanted to understand the extent of the breach and so I dug into the email address that was used to register these domains, and identified four domains that have reportedly been compromised. Each one of the four domains has subdomains that point to Russia.
- 60windowsin60days[.]com
- fox8recipes[.]com
- hondafastbreak[.]com
- myblurryeyes[.]com
By digging a little deeper with the IP address using passive DNS, I noticed more domains that were compromised that are using that same IP address, one that was registered under privacy. Based on the name, however, is also related is fox8creative[.]com. All four of these domains have a sub domain that is test, top, and new.
I know that GoDaddy has implemented some changes to help prevent this type of attack going forward, but based on the dates of some of data I’m seeing inside of Iris Investigate this type of attack is still an issue. I would suggest that whether you own a single domain, or north of 30,000 domains, you should make sure your account hasn’t been compromised, and I would advocate for implementing a two-factor authentication for your domains.
Good luck hunting.